A financially motivated threat cluster is systematically targeting trucking and logistics companies, weaponizing common Remote Monitoring and Management (RMM) software to infiltrate their networks. The ultimate goal of these attacks is to hijack freight operations and steal high-value physical cargo, particularly food and beverage products.
The Campaign’s Objective: Cargo Theft via Digital Intrusion
According to cybersecurity firm Proofpoint, this threat actor has been active since at least June 2025 and is collaborating with organized crime groups. Their strategy involves compromising surface transportation companies to fraudulently gain control over shipments.
Researchers Ole Villadsen and Selena Larson explained the mechanics: “In the observed campaigns, threat actors aim to infiltrate companies and use their fraudulent access to bid on real shipments of goods to ultimately steal them.” The stolen cargo is most likely resold online or shipped overseas for profit.
While these attacks share similarities with earlier campaigns against the transportation sector, there is no evidence currently linking them to the same threat actor.
The Attack Vectors: A Multi-Pronged Social Engineering Approach
The attackers employ a variety of deceptive methods to gain initial access:
- Email Account Compromise: Hijacking existing email conversations within the industry to appear legitimate.
- Spear-Phishing: Sending targeted emails to asset-based carriers, freight brokers, and supply chain providers.
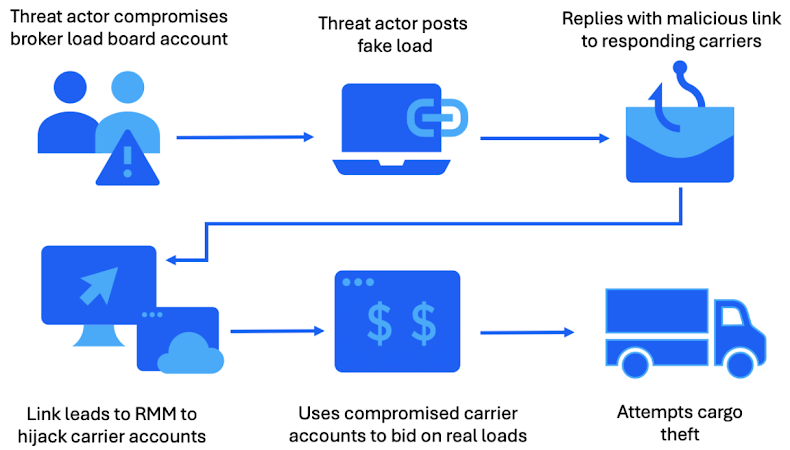
- Fraudulent Listings: Posting fake freight listings on online load boards using compromised accounts, then sending malicious links to carriers who express interest.
Proofpoint highlighted the effectiveness of this last method: “This tactic exploits the trust and urgency inherent in freight negotiations.”
The Infection Chain: From Malicious Link to RMM Deployment
The malicious links in emails lead to booby-trapped MSI installers or executables. Instead of deploying custom malware, these installers deploy legitimate and widely used RMM tools such as:
- ScreenConnect
- SimpleHelp
- PDQ Connect
- Fleetdeck
- N-able
- LogMeIn Resolve
In some cases, multiple RMM tools are used in tandem. For instance, PDQ Connect has been observed being used to silently drop and install ScreenConnect and SimpleHelp on the target system.
Post-Infiltration Activities: Reconnaissance and Operational Takeover
Once remote access is established via the RMM software, the attackers proceed with a clear set of objectives:
- Reconnaissance: They conduct system and network discovery to understand the environment.
- Credential Theft: They deploy tools like WebBrowserPassView to harvest saved credentials, allowing them to move deeper into the corporate network.
- Operational Sabotage and Fraud: In at least one confirmed case, the attackers used their access to:
- Delete existing freight bookings.
- Block dispatcher notifications.
- Add their own device to the dispatcher’s phone extension.
- Book shipments under the compromised carrier’s name and coordinate the transport for theft.
Why RMM Software is the Perfect Weapon
The abuse of RMM tools provides significant advantages to threat actors:
- No Custom Malware Required: They can use off-the-shelf software, bypassing the need for complex development.
- Built-in Stealth: These tools are common in corporate IT environments, so their activity often blends in with normal administrative traffic and is rarely flagged as malicious by security solutions.
- Legitimate Appearance: The installers are often digitally signed, making them appear trustworthy to both users and security software.
As Proofpoint noted, “end users might be less suspicious of installing RMMs than other remote access trojans.”


