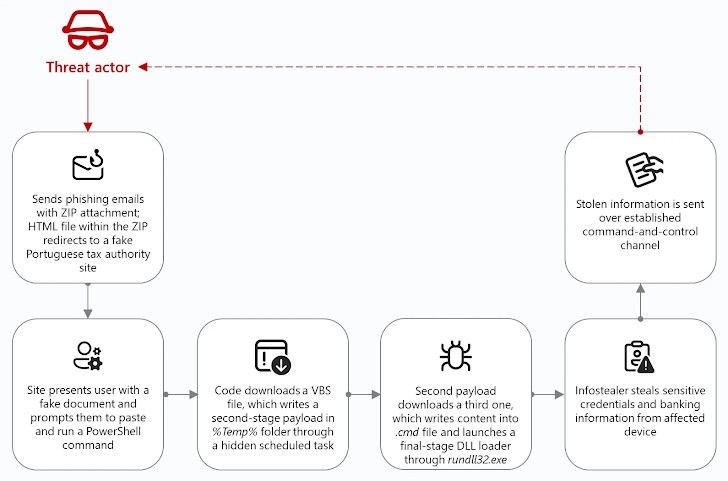
Threat actors are increasingly using a deceptive method known as ClickFix to spread a powerful backdoor called CORNFLAKE.V3.
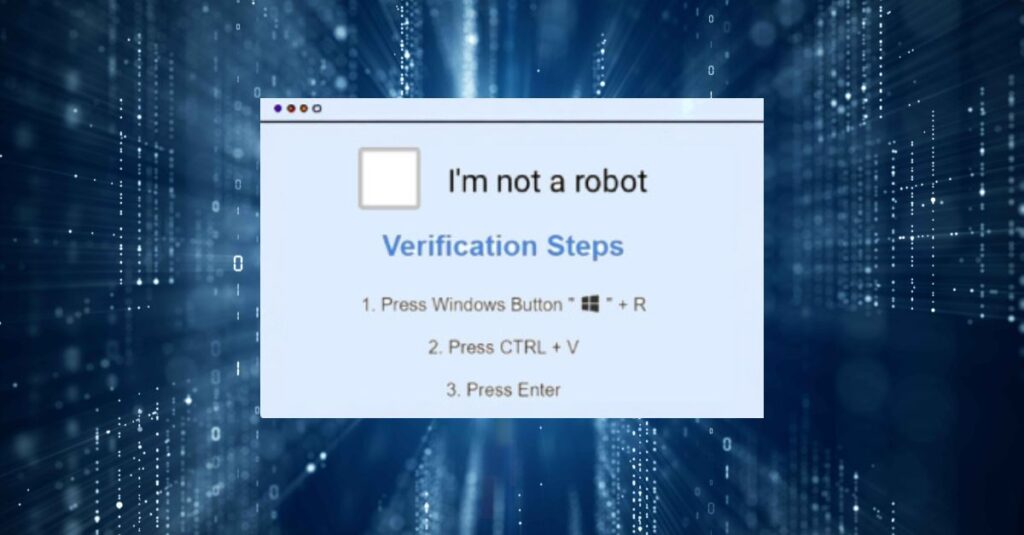
How ClickFix Works
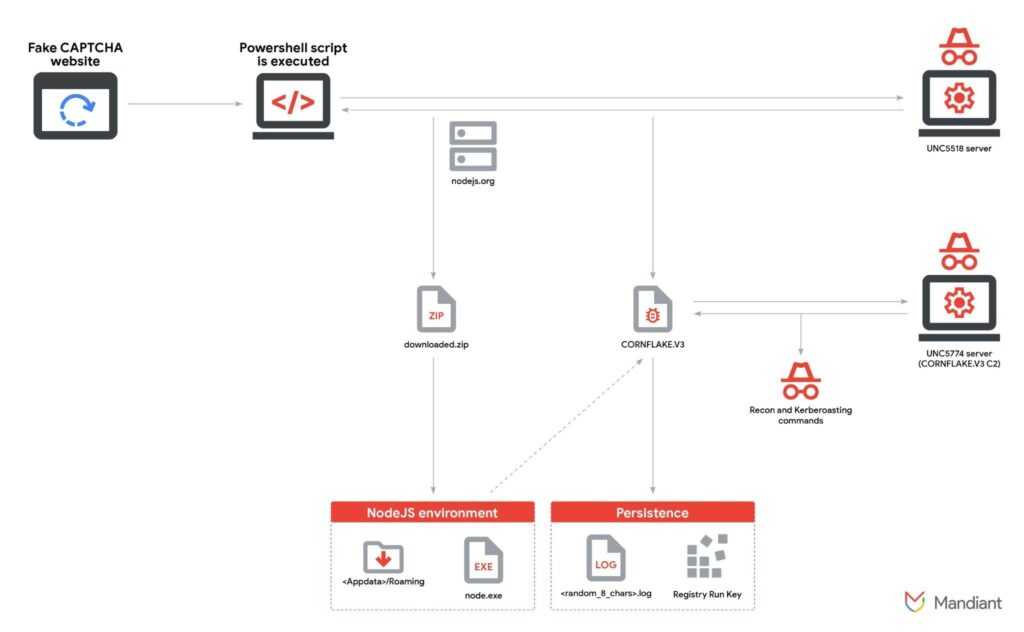
According to Google-owned Mandiant, the campaign is operated by UNC5518, an access-as-a-service group. Attackers lure victims to fake CAPTCHA pages, tricking them into following instructions that ultimately provide attackers with access to their systems. This access is later monetized or handed over to other hacking groups.
Mandiant’s report explains that ClickFix convinces users to copy a malicious PowerShell script and run it through the Windows Run dialog. Once executed, the script launches a dropper that installs additional malware from a remote server.
Groups Using CORNFLAKE.V3
The compromised access is sold or shared with other groups such as:
- UNC5774, a financially motivated threat group using CORNFLAKE to deliver multiple payloads.
- UNC4108, which employs PowerShell-based tools like VOLTMARKER and NetSupport RAT for unknown objectives.
Technical Breakdown of CORNFLAKE.V3
- Delivered in both JavaScript and PHP versions.
- Functions as a backdoor capable of executing payloads via HTTP (executables, DLLs, scripts, and PowerShell commands).
- Collects system information and communicates with external servers through Cloudflare tunnels for stealth.
- Compared to CORNFLAKE.V2 (which acted only as a downloader), CORNFLAKE.V3 adds persistence through Windows Registry Run keys and supports multiple payload types.
Payloads include:
- An Active Directory reconnaissance tool.
- A Kerberoasting credential theft script.
- A secondary backdoor called WINDYTWIST.SEA, which enables reverse shells, TCP traffic relay, command execution, and self-removal.
The Growth of ClickFix Kits
Over the past year, ClickFix kits have become widely popular among cybercriminals. They trick users into pasting commands into Windows Run, PowerShell, or Terminal, under the disguise of CAPTCHA checks, Cloudflare Turnstile verifications, or even Discord server authentications.
Attackers often combine ClickFix with phishing, SEO poisoning, malvertising, and drive-by downloads. Microsoft notes that configurable ClickFix builders are being sold in underground markets for $200 to $1,500 per month. These kits generate fake landing pages and malicious commands designed to bypass antivirus tools and Microsoft Defender SmartScreen.
Recommended Security Measures
To reduce the risks of ClickFix-based attacks, experts recommend:
- Disabling the Windows Run dialog box in enterprise environments where possible.
- Running regular phishing and social engineering simulations.
- Enabling detailed logging to detect suspicious script execution.
- PowerShell script block logging for detecting obfuscated commands.
- Restrictive execution policies such as AllSigned or RemoteSigned.
- Group Policy hardening, including limiting Run menu access and monitoring Windows Terminal paste actions.
USB-Based Infections and Cryptocurrency Mining
Mandiant also uncovered a separate campaign that spreads malware via infected USB drives. When users run malicious LNK files, it triggers a chain that delivers multiple malware components, including the XMRig cryptocurrency miner.
Key components of the USB attack include:
- DIRTYBULK, a DLL launcher.
- CUTFAIL, a malware dropper that installs additional payloads like HIGHREPS and PUMPBENCH.
- PUMPBENCH, a backdoor that performs reconnaissance, communicates with PostgreSQL servers, and installs XMRig.
- XMRig, used for mining cryptocurrencies such as Monero, Dero, and Ravencoin.
image import

Mandiant emphasizes that the low cost and effectiveness of USB-based infections make them a favored technique among cybercriminals.