A cybercriminal known as Detour Dog has been exposed as the operator behind large-scale DNS-powered malware campaigns that distribute Strela Stealer, an information-stealing malware. Security researchers from Infoblox have traced the attacker’s infrastructure, revealing how it fuels the spread of a backdoor named StarFish, which acts as the entry point for Strela Stealer infections.
Background and Evolution
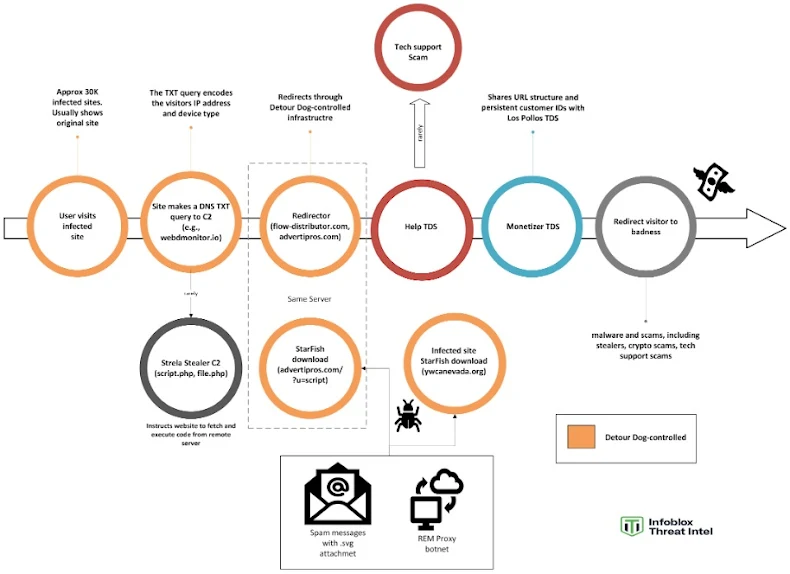
Detour Dog has been active since at least February 2020, initially linked to scam-driven redirection attacks on WordPress sites. The attacker injected malicious JavaScript that leveraged DNS TXT records to redirect users to fraudulent websites. By August 2023, GoDaddy-owned Sucuri highlighted these methods. Over time, the group’s tactics evolved, and the redirects were no longer limited to scams. Instead, they advanced to executing remote content via DNS-based command-and-control (C2) infrastructure.
Infrastructure and Attack Chain
Infoblox discovered that 69% of StarFish malware staging servers were controlled by Detour Dog. The backdoor, a lightweight reverse shell, is deployed through malicious SVG files to establish persistent access on victim systems. According to IBM X-Force, Detour Dog’s infrastructure is critical to Strela Stealer operations, with campaigns traced back to Hive0145, a financially motivated threat actor likely working as an Initial Access Broker (IAB).
Detour Dog’s setup also ties into botnets like REM Proxy and Tofsee, which were contracted to send spam emails carrying malicious payloads. These spam campaigns were distributed through loaders such as PrivateLoader, expanding the malware’s reach.
Unique DNS-Based Distribution Model
One of the most notable aspects of this campaign is the use of DNS TXT records to deliver commands. Compromised WordPress sites, which appear normal for most visitors, communicate with Detour Dog’s C2 servers. Roughly 90% of the time, the sites function as usual, while in rare cases (around 1%), they execute remote commands. This stealthy approach helps the malware remain undetected for long periods.
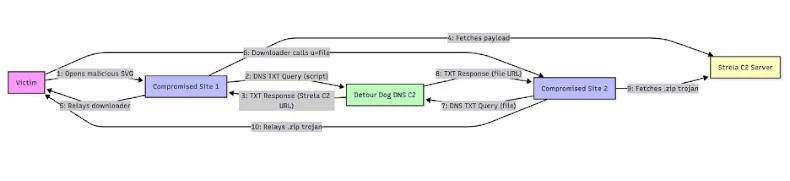
The infection chain works step-by-step:
- Victim opens a malicious document that triggers an SVG file.
- The SVG reaches out to a compromised domain.
- That domain queries the Detour Dog C2 server via DNS TXT.
- The C2 responds with a Base64-encoded command containing a “down” prefix and Strela Stealer C2 link.
- The compromised site strips the prefix, uses curl to fetch the StarFish downloader, and relays it to the victim.
- A second compromised domain repeats the same process, fetching the malware from another Strela C2 server and delivering it to the target system.
Financial Motivation and Shift in Tactics
Detour Dog was previously focused on traffic redirection scams under the VexTrio Viper ad fraud umbrella. However, with the crackdown on scams over the past two years, Infoblox suggests that the attacker shifted toward malware distribution for financial gain. This marks the first confirmed case of Detour Dog being directly involved in malware operations.
Disruption Efforts
On July 30 and August 6, 2025, Infoblox and the Shadowserver Foundation sinkholed two Detour Dog C2 domains, webdmonitor[.]io and aeroarrows[.]io. Despite these efforts, evidence shows the actor continues to operate a distribution-as-a-service (DaaS) platform, with additional unidentified files moving through their network.