Cybersecurity researchers have revealed a serious vulnerability affecting Ask Gordon, the AI assistant integrated into Docker Desktop and Docker CLI, that could allow attackers to execute code and steal sensitive information. The flaw, dubbed DockerDash by Noma Labs, was fixed in Docker version 4.50.0 released in November 2025.
How DockerDash Works
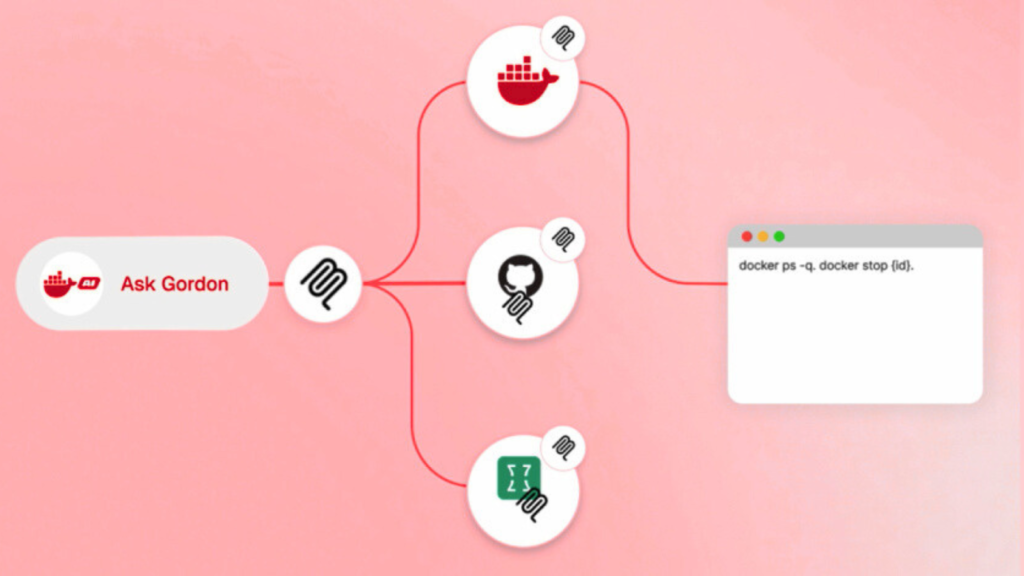
According to Sasi Levi, lead security researcher at Noma, the vulnerability exploits a metadata handling flaw in Ask Gordon AI. “A single malicious label embedded in a Docker image can compromise the environment through a three-step attack: Gordon AI reads and interprets the instruction, sends it to the MCP [Model Context Protocol] Gateway, which executes it via MCP tools,” Levi explained.
The issue arises because Ask Gordon treats unverified metadata as executable commands without any validation. This allows attackers to bypass security layers and execute commands through normal AI queries.
Impact on Docker Systems
Exploitation of DockerDash can result in remote code execution for cloud and CLI environments or data exfiltration for desktop users. The vulnerability stems from the AI’s inability to distinguish between harmless metadata and malicious instructions, a problem researchers term Meta-Context Injection.
“MCP Gateway cannot differentiate between informational Docker LABELs and pre-authorized executable commands,” Levi said. “By injecting malicious instructions into metadata, attackers can hijack the AI’s reasoning flow.”
Attack Chain Explained
In a potential attack, an adversary could:
- Create a malicious Docker image with weaponized LABEL fields in the Dockerfile
- Wait for a victim to query Ask Gordon AI about the image
- Ask Gordon to forward parsed instructions to MCP Gateway, which trusts the input as legitimate
- MCP Gateway executes the commands using victim Docker privileges
This sequence allows attackers to run code on the target system without triggering security alerts.
Data Exfiltration Risk
The same flaw can be exploited for sensitive data theft. By leveraging Ask Gordon’s read-only permissions in Docker Desktop, attackers can extract configuration details, container info, mounted directories, network topology, and installed tools using MCP tools.
The recent Docker 4.50.0 update also fixes a related prompt injection vulnerability reported by Pillar Security. This flaw could have been exploited to hijack Ask Gordon via malicious Docker Hub repository metadata.
Mitigation and Recommendations
“DockerDash demonstrates that AI supply chain risk is a serious, present-day threat,” Levi said. “Even trusted inputs can carry hidden malicious payloads that manipulate AI execution paths. Organizations must implement zero-trust validation for all contextual data processed by AI models.”
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.