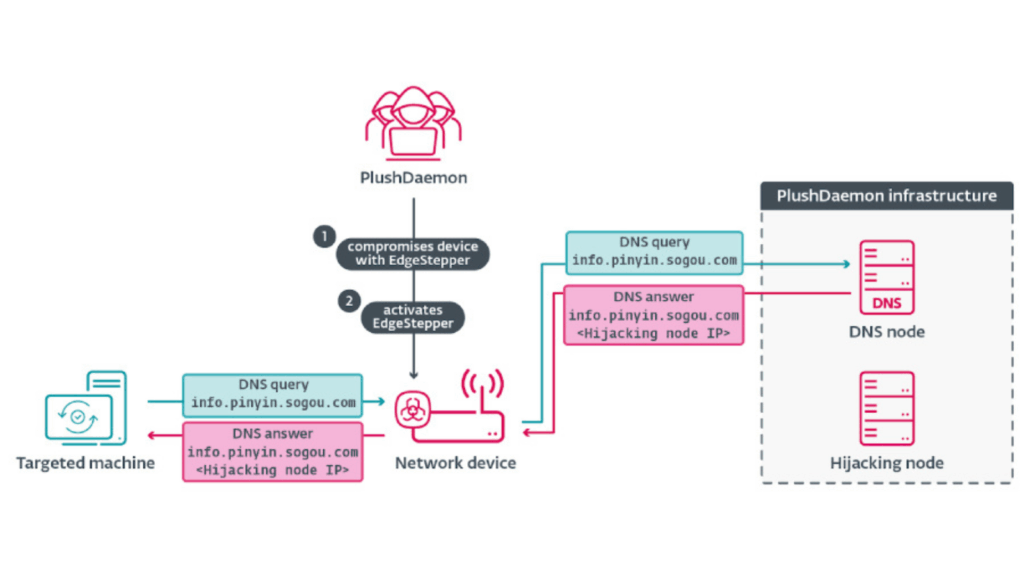
A China aligned threat actor known as PlushDaemon has been identified using a new Go based network backdoor called EdgeStepper. This tool enables adversary in the middle attacks by hijacking DNS queries and redirecting them to malicious infrastructure. Through this method, attackers can compromise legitimate software update channels and deliver harmful payloads.
How the Attack Works
According to ESET security researcher Facundo Muñoz, EdgeStepper forces all DNS requests to pass through an external malicious node. This means that any legitimate update traffic is silently routed to servers controlled by the attacker.
PlushDaemon has been active since at least 2018 and has targeted organizations in the United States, New Zealand, Cambodia, Hong Kong, Taiwan, South Korea, and mainland China. Earlier reports from ESET described how this group compromised a South Korean VPN provider named IPany to deliver another implant known as SlowStepper to multiple victims in the semiconductor and software development industries.
Additional victims include a university in Beijing, a Taiwanese electronics manufacturer, an automotive industry organization, and a Japanese manufacturing company. Recent observations show the group continuing its activity in Cambodia by targeting two more organizations with SlowStepper.
The Role of AitM Poisoning
The primary method used by PlushDaemon for initial access is adversary in the middle poisoning. Over the past two years, more China affiliated APT clusters such as LuoYu, BlackTech, Evasive Panda, TheWizards APT, Blackwood and FontGoblin have adopted this technique. ESET is currently tracking ten China aligned groups that hijack software update mechanisms to move laterally within networks.
The attack usually begins by compromising an edge device like a router through weak passwords or an unpatched vulnerability. Once the attacker gains access, EdgeStepper is deployed.
DNS Redirection Process
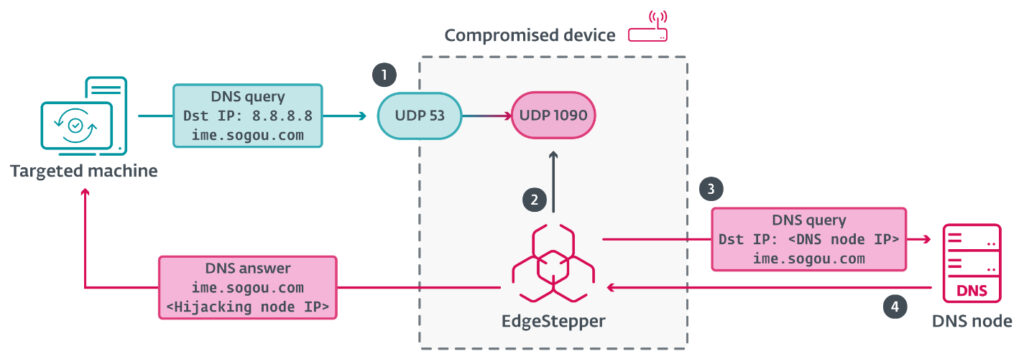
After activation, EdgeStepper reroutes DNS queries to a malicious DNS server. That server checks whether the requested domain is associated with software updates. If it is, the server responds with the IP address of the hijacking node. In some cases, the same machine acts as both the DNS and hijacking node and responds directly with its own IP address.
EdgeStepper contains two internal components. The Distributor resolves the IP address of the malicious DNS node located at “test.dsc.wcsset[.]com”. The Ruler module uses iptables rules to modify IP packet filtering settings.
Targeting Software Update Channels
The attackers specifically look for Chinese software such as Sogou Pinyin to hijack their update traffic. Through this process, the malware replaces legitimate update files with a malicious DLL named “popup_4.2.0.2246.dll”, also called LittleDaemon.
LittleDaemon acts as a first stage implant. It communicates with the attacker’s server to download a module called DaemonicLogistics, but only if SlowStepper is not already present on the device.
DaemonicLogistics then downloads and executes the full SlowStepper backdoor. SlowStepper includes capabilities to capture system information, steal browser passwords, collect files, extract data from messaging applications, and delete itself if needed.