Cybersecurity researchers have uncovered a stealthy method that enables attackers to extract Windows secrets and credentials without triggering alerts from most Endpoint Detection and Response (EDR) solutions. This approach can be used after gaining initial access to a system, allowing attackers to perform lateral movement across networks while staying hidden from standard monitoring tools.
How Windows Stores and Protects Secrets
Windows relies on the Local Security Authority (LSA), which operates inside the lsass.exe process, to manage sensitive information. It maintains two main in-memory databases that map to registry hives on disk:
- SAM Database: Handles user, group, and alias objects. It links to the SAM registry hive and stores user credentials. While it contains passwords, there is no straightforward API to extract them in plaintext.
- Security Database: Stores policy details, trusted domain data, account objects, and secret objects. It maps to the SECURITY registry hive and contains cached domain credentials and machine keys.
Although these databases can be accessed using RPC interfaces such as MS-SAMR and MS-LSAD, they do not provide a simple way to decrypt secrets. Accessing them requires interacting directly with the SAM and SECURITY hives.
To safeguard these hives, Discretionary Access Control Lists (DACLs) limit access to SYSTEM-level accounts. Furthermore, all sensitive values, like user credentials and machine keys, are encrypted and require additional data from the SYSTEM hive to generate a valid decryption key.
Challenges with Traditional Credential Dumping
Attackers have historically used multiple techniques, both locally and remotely, to capture credentials. However, modern EDR tools and Windows Defender aggressively monitor common approaches. For example:
- Direct interaction with lsass.exe memory is high-risk and almost always triggers alerts.
- EDRs use kernel-mode callbacks (such as
CmRegisterCallbackEx) to track registry access attempts, particularly those targeting sensitive keys likeHKLM\SAMorHKLM\SECURITY. - To reduce performance overhead, EDR vendors typically watch only a list of high-risk APIs and registry paths, leaving some lesser-known functions unmonitored.
The Newly Discovered Evasion Method
According to researcher Sud0Ru, a newly identified method combines two Windows internals to bypass EDR detection.
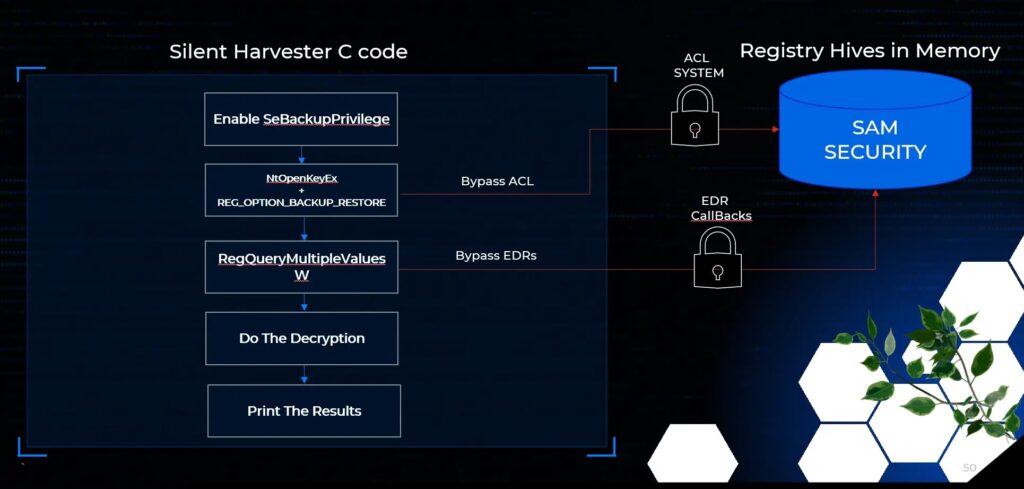
1. Bypassing ACL Restrictions with NtOpenKeyEx
By using the undocumented native API NtOpenKeyEx with the REG_OPTION_BACKUP_RESTORE flag, attackers can bypass registry ACL checks if they hold the SeBackupPrivilege (granted to administrators). This provides direct access to the protected SAM and SECURITY hives, even without SYSTEM-level privileges.
2. Evading Detection with RegQueryMultipleValuesW
Normally, security tools monitor calls like RegQueryValueExW to detect malicious registry access. Instead, this method uses the lesser-known RegQueryMultipleValuesW, which can fetch multiple registry values at once. Since this API is rarely monitored, attackers can extract encrypted secrets without raising alarms.
Why This Technique Works
- The entire operation is performed in memory, leaving no on-disk evidence.
- Attackers avoid commonly tracked API calls, slipping past most EDR detection logic.
- It exploits legitimate Windows functionality that security vendors often overlook.
Conclusion
This discovery highlights how attackers can exploit native Windows features to bypass mature security systems. While the stolen secrets still require decryption, the collection method itself represents a significant challenge for defenders, proving that even advanced EDR tools can miss stealthy, well-crafted techniques.