Embargo Ransomware Rakes in $34.2 Million in Crypto Since April 2024
A recent report from blockchain intelligence firm TRM Labs reveals that the Embargo ransomware group has generated approximately $34.2 million in cryptocurrency since its emergence in April 2024. Most of the identified victims are based in the United States, particularly within the healthcare, business services, and manufacturing sectors.
According to TRM Labs, “about USD 34.2 million in incoming transactions are likely linked to the group,” with notable victims including American Associated Pharmacies, Memorial Hospital and Manor (GA), and Weiser Memorial Hospital (ID). Some ransom demands reached as high as $1.3 million.
Possible BlackCat/Alphv Connection
Researchers believe Embargo may be a successor to BlackCat/Alphv, citing technical and behavioral overlaps such as:
- Use of the Rust programming language
- A similarly structured data leak site
- Shared wallet infrastructure with other ransomware operators
While not as widespread as ransomware groups like LockBit, Akira, or Cl0p, TRM Labs notes that Embargo appears well-funded and technically capable, possibly leveraging code or expertise from past threat actors.
Laundering Tactics and Dormant Funds
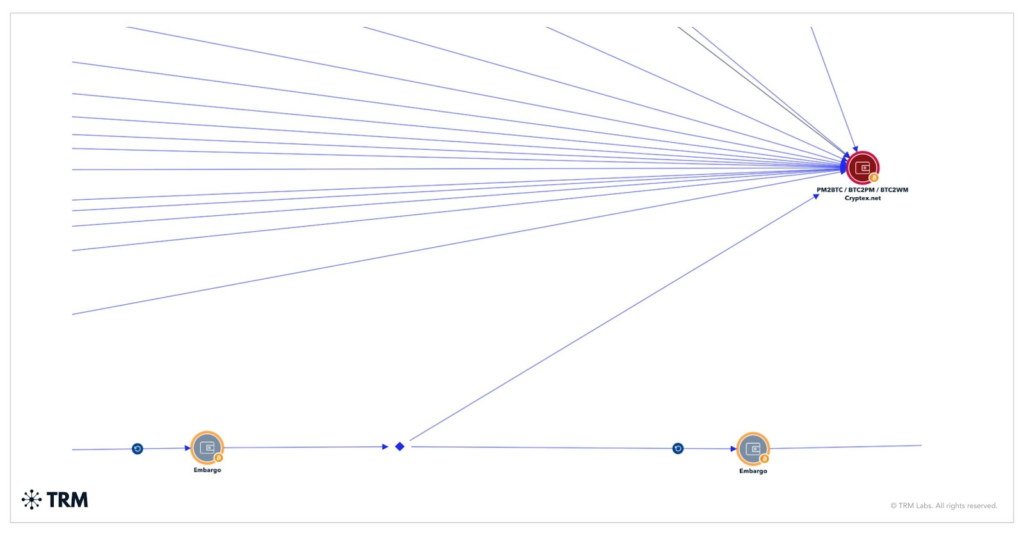
Investigations show that Embargo launders ransom payments through:
- Intermediary wallets
- High-risk exchanges
- Sanctioned platforms such as Cryptex.net
The researchers also found approximately $18.8 million sitting idle in unattributed wallets, which they suspect is part of a deliberate evasion strategy.
AI-Powered Ransomware Operations
TRM Labs warns that Embargo may be using artificial intelligence (AI) and machine learning (ML) to:
- Craft highly convincing phishing lures
- Adapt malware for new targets
- Increase attack speed and efficiency
Despite being financially motivated, the group has also used politically charged messages, suggesting potential state affiliations.
Targeting Critical Sectors for Maximum Impact
Embargo’s main targets include:
- Healthcare (posing direct risks to patient care)
- Business services
- Manufacturing
While the majority of attacks are in the US, incidents have also been observed in Europe and Asia. The group typically exploits unpatched vulnerabilities or phishing as initial entry points, then disables security defenses, removes backup and recovery options, and finally encrypts the victim’s data.
Using a double extortion model, Embargo operates its own leak site to pressure non-paying victims and sometimes names individuals, threatening to sell or publicly leak stolen data to intensify financial, reputational, and regulatory consequences.


