Threat actors are exploiting the popularity of artificial intelligence (AI) by embedding malware into fake productivity and AI-enhanced tools, according to a recent Trend Micro report. This campaign, known as EvilAI, is targeting organizations worldwide across regions such as Europe, the Americas, and the Asia, Middle East, and Africa (AMEA) region.
Global Impact and Targeted Sectors
The campaign has affected industries like manufacturing, government, healthcare, technology, and retail. Countries most impacted include India, the United States, France, Italy, Brazil, Germany, the United Kingdom, Norway, Spain, and Canada. This wide distribution shows EvilAI is not an isolated incident but an evolving, large-scale cyber campaign.
How EvilAI Operates
EvilAI disguises malware within tools that appear genuine, using professional interfaces and valid digital certificates from disposable companies. These certificates are often revoked later, but by then, the malware has already infiltrated the target systems.
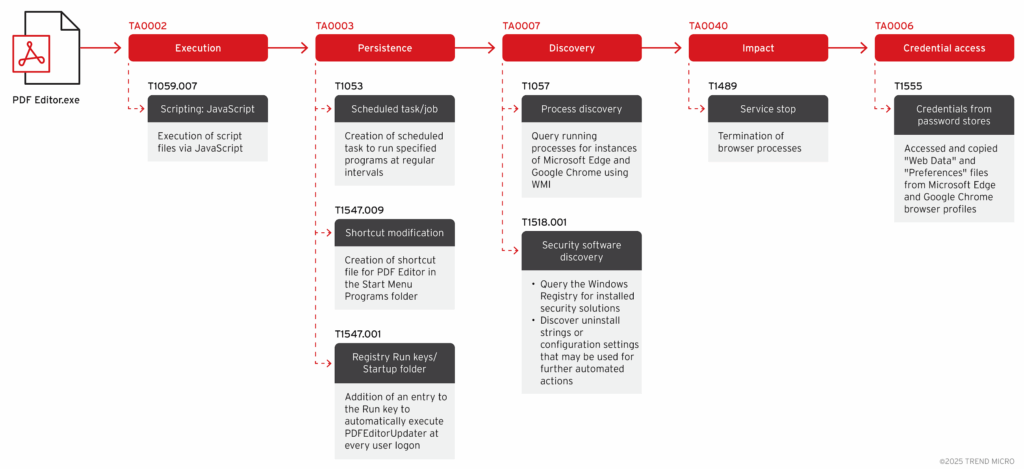
Some of the fake applications observed include AppSuite, Epi Browser, JustAskJacky, Manual Finder, OneStart, PDF Editor, Recipe Lister, and Tampered Chef. Once installed, these apps perform malicious activities in the background while looking legitimate to users.
The malware campaign leverages multiple distribution techniques, including:
- Newly registered websites mimicking trusted vendor portals
- Malicious advertisements and SEO manipulation
- Promoted download links on forums and social platforms
EvilAI enables reconnaissance, exfiltration of browser data, and persistent communication with command-and-control (C2) servers through encrypted AES channels. It also enumerates installed security software and deploys additional payloads while avoiding detection.
BaoLoader and TamperedChef Links
Researchers from G DATA, Expel, and TRUESEC discovered overlaps in infrastructure among apps like AppSuite, ManualFinder, and OneStart. Expel identified a malware variant named BaoLoader, a backdoor mainly used for advertising fraud and software installations through affiliate distribution. BaoLoader and TamperedChef share similarities, but they differ in behavior and code-signing patterns.
- BaoLoader: Often signed with certificates from Panama and Malaysia.
- TamperedChef: Signed with certificates issued to companies in Ukraine and Great Britain.
Field Effect and GuidePoint Security also uncovered more fake apps posing as calendar and image viewers. These apps used the NeutralinoJS framework to run JavaScript payloads, providing covert file system access and data theft capabilities. Attackers even leveraged Unicode homoglyphs to conceal malicious code inside seemingly harmless responses, bypassing signature-based detection.
A Broader Malware Ecosystem
EvilAI is not a single malware strain but a collection of related campaigns with different developers, infrastructures, and goals. This suggests a much larger operation that may involve a malware-as-a-service ecosystem or a code-signing marketplace.