Cybersecurity researchers have revealed a new supply chain attack that targets the NuGet package manager using a malicious typosquat of Nethereum, a well-known Ethereum .NET integration library. The main goal of this attack is to steal crypto wallet keys from unsuspecting developers and users.
Malicious Package Discovered
The harmful package, named Netherеum.All, was discovered to include code that decodes a command-and-control (C2) server and exfiltrates sensitive data such as mnemonic phrases, private keys, and keystore files, according to security firm Socket.
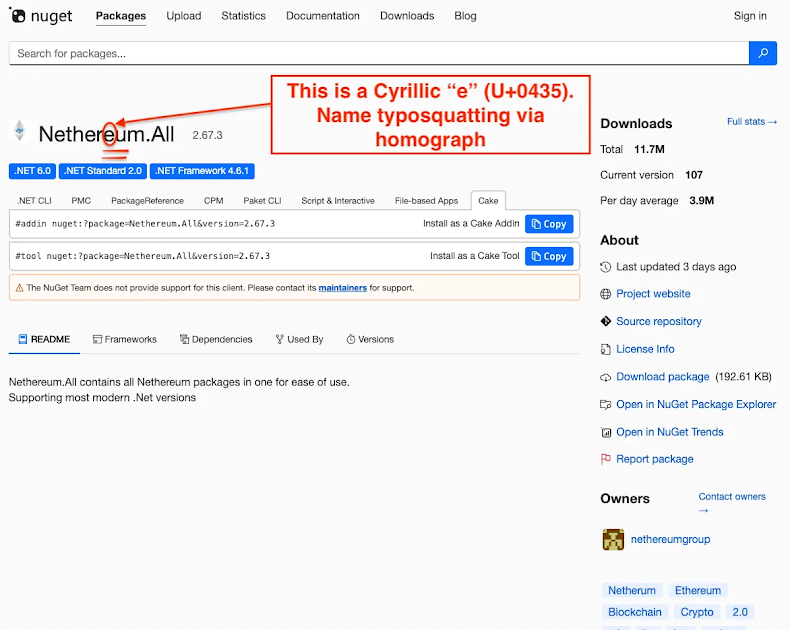
The package was uploaded by a user identified as “nethereumgroup” on October 16, 2025, and was later removed from NuGet four days later due to a violation of the platform’s Terms of Use.
How the Attack Works
The threat actors cleverly replaced the last letter “e” in Nethereum with a Cyrillic homoglyph “е” (U+0435). This subtle change made the fake library look identical to the original, tricking developers into installing it.
To make the package appear more legitimate, attackers artificially inflated download counts, falsely claiming 11.7 million downloads. This suspiciously high number helped the package rank higher in NuGet search results and made it appear trustworthy.
“A threat actor can publish many versions, then script downloads of each .nupkg file through the v3 flat-container or loop nuget.exe install and dotnet restore with no-cache options from cloud hosts,” explained security researcher Kirill Boychenko. “By rotating IPs, changing user agents, and parallelizing requests, they boost volume while avoiding client-side caching.”
Deceptive Code and Payload
Inside the malicious NuGet package, the main payload resides in a function called EIP70221TransactionService.Shuffle. This function parses an XOR-encoded string to locate the C2 server (solananetworkinstance[.]info/api/gads) and exfiltrates stolen crypto wallet data back to the attacker’s infrastructure.
Further investigation revealed that the same threat actor previously uploaded another deceptive NuGet package named “NethereumNet” with similar malicious functionality earlier in the month. The NuGet security team has already taken it down.
Broader Trend of Homoglyph Attacks
This is not the first time such homoglyph-based deception has been detected in the NuGet repository. In July 2024, researchers from ReversingLabs identified several malicious packages that mimicked legitimate ones by replacing certain characters with look-alike alternatives, successfully evading casual inspection.
Unlike other open-source repositories such as PyPI, npm, Maven Central, Go Module, and RubyGems, the NuGet repository does not restrict naming schemes to ASCII characters, except for prohibiting spaces and unsafe URL characters. This lack of restriction gives attackers more room to exploit homoglyphs.
Security Recommendations
To protect against such supply chain threats, developers are advised to:
- Verify the publisher’s identity before installing any library.
- Check for sudden download spikes or suspiciously high counts.
- Monitor outgoing network traffic for connections to unknown or suspicious domains.
- Use security scanning tools to inspect packages before integration.