The U.S Federal Bureau of Investigation (FBI) has issued a new security alert, stating that cybercriminals are increasingly impersonating financial institutions to steal money and confidential information. These activities are directly linked to a major rise in account takeover fraud, a type of cybercrime that has already caused losses exceeding two hundred sixty two million dollars since the beginning of the year.
According to the FBI, more than five thousand one hundred victims have reported incidents so far. The schemes target individuals, small businesses, and large organizations across various industries.
Account takeover fraud occurs when attackers gain unauthorized access to online banking systems, payroll accounts, or health savings accounts. Criminals typically rely on social engineering methods that use fear, urgency, and deception. These tactics include fraudulent text messages, phone calls claiming to be customer service, and emails that guide victims toward phishing websites.
These malicious pages trick users into entering their login credentials. In some cases, victims are urged to click on links that appear to report suspicious transactions. Once criminals obtain the username, password, and multi factor authentication code, they reset the account password and secure full control.
The FBI noted that some criminals impersonate bank staff to convince victims that firearms or other purchases were made using their accounts. They then connect victims with another criminal pretending to be law enforcement, increasing the pressure and gaining access to sensitive information.
The agency also highlighted the growing use of search engine optimization poisoning. This tactic manipulates search results to place fraudulent links above legitimate websites, causing victims to unknowingly visit fake banking pages.
Once an account is compromised, cybercriminals immediately transfer funds into accounts they control. The money is later moved to cryptocurrency wallets, making it difficult to trace.
Cybersecurity experts emphasize that many of these attacks take place because criminals understand internal banking processes and money movement workflows. Saviynt chief trust officer Jim Routh stated that traditional verification methods, especially manual phone call checks and SMS authentication prompts, remain the most effective controls. He added that the widespread dependence on passwords, even when passwordless systems exist, continues to fuel these incidents.
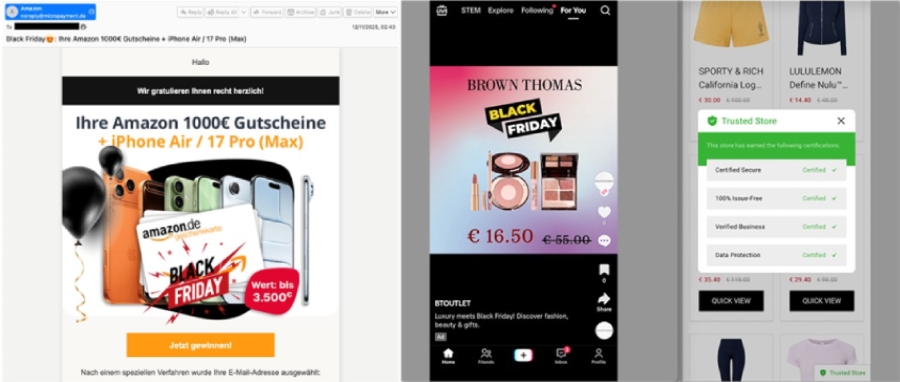
Several cybersecurity companies, including Darktrace, Flashpoint, Fortinet, and Zimperium, have warned that the holiday season is a high risk period. Threats include Black Friday scams, QR code fraud, fake gift card sites, and phishing campaigns impersonating Amazon, Temu, and other major brands. Many attackers are now using artificial intelligence tools to craft convincing emails and fraudulent websites.
Fortinet FortiGuard Labs reported identifying more than seven hundred fifty malicious domains created for holiday related scams during the last three months. Over one point five seven million stolen login credentials linked to major e commerce sites have also been found circulating through underground markets.
Attackers are simultaneously exploiting vulnerabilities in Adobe or Magento systems, Oracle E Business Suite, WooCommerce, Bagisto, and other e commerce platforms. The list includes security issues identified as CVE-2025-54236, CVE-2025-61882, and CVE-2025 47569.
Researchers from Zimperium noted a four times increase in mobile phishing sites that use well known brand names to trick users into clicking links or downloading malicious applications.
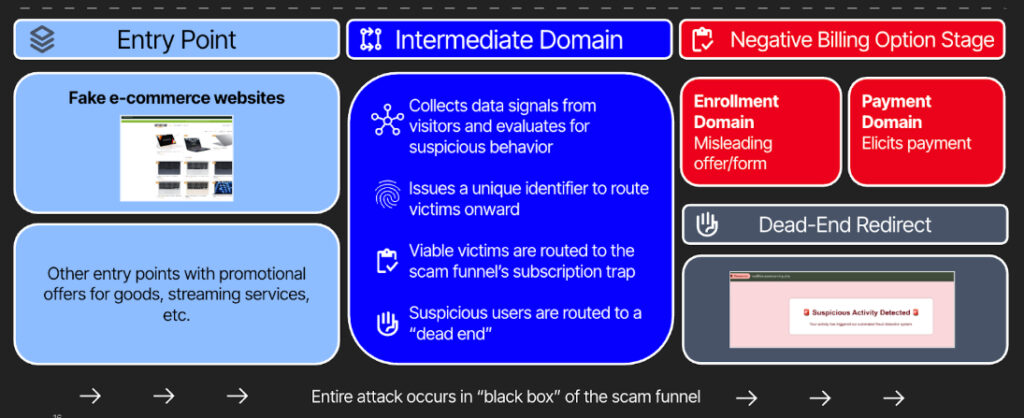
Threat intelligence company Recorded Future also warned about a rise in purchase scams involving fake e commerce stores. These operations use multistage attack funnels and traffic distribution systems (TDS) to ensure that only carefully selected victims proceed to the final fraudulent transaction page. Because victims authorize the payments themselves, criminals receive instant financial gains.
Some fraud operations also use recovery service scams, performing two back to back fraudulent transactions to maximize the value of stolen card details.
Recorded Future stated that a sophisticated dark web infrastructure supports these fraud schemes. Criminals run advertising campaigns using stolen credit cards to promote scam sites, which then steal more payment card data and continue the cycle.


