Cybersecurity researchers have identified a Ukraine-based IP network, FDN3 (AS211736), as the source of massive brute-force and password spraying attacks against SSL VPN and RDP systems. These activities took place between June and July 2025 and have raised concerns about the growing abuse of bulletproof hosting infrastructure to launch large-scale cyberattacks.
The Origin of Attacks
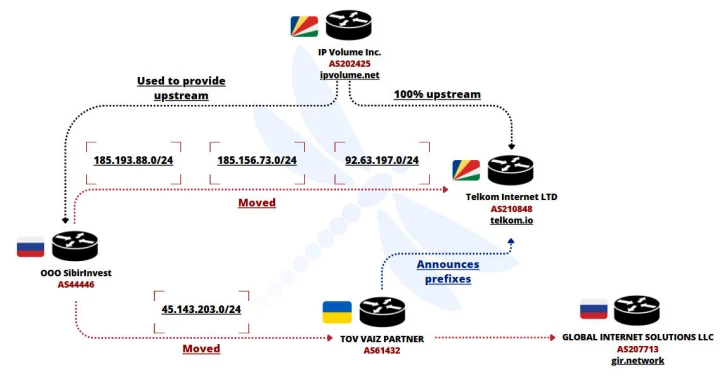
According to French cybersecurity company Intrinsec, the campaigns originated from FDN3, which is believed to be part of a larger cluster of abusive infrastructure. This cluster also includes Ukrainian autonomous systems VAIZ-AS (AS61432), ERISHENNYA-ASN (AS210950), and a Seychelles-based system known as TK-NET (AS210848).
Researchers noted that these networks, allocated in mid-2021, regularly exchange IPv4 prefixes with each other. This tactic helps them evade blacklists and continue their malicious operations.
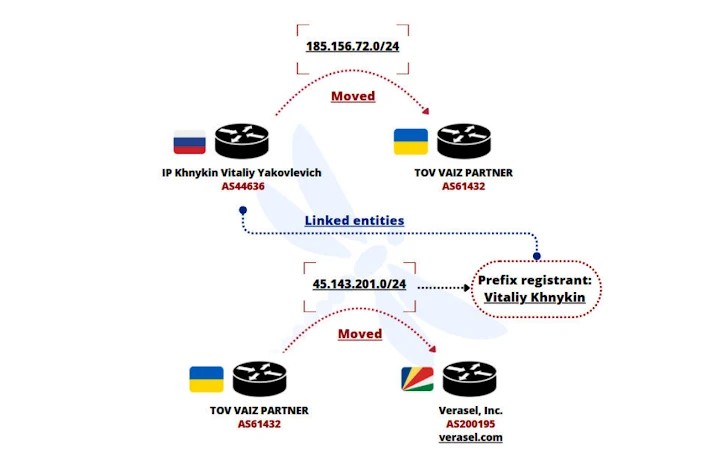
Suspicious Prefix Allocations and Connections
- AS61432: Currently announces prefix 185.156.72[.]0/24.
- AS210950: Announces prefixes 45.143.201[.]0/24 and 185.193.89[.]0/24.
- AS210848: Another network tied to Seychelles, with several prefixes overlapping with FDN3.
Some prefixes were even linked back to a Russian operator, SibirInvest OOO (AS44446), while one, 88.210.63[.]0/24, was previously tied to U.S.-based Virtualine, a known bulletproof hosting provider.
Attack Details
The IPv4 prefix range associated with FDN3 was tied to large-scale brute-force and password spraying operations. The activity spiked between July 6 and July 8, 2025, with attack waves lasting up to three days.
These attack techniques are often used by ransomware-as-a-service (RaaS) groups such as Black Basta, GLOBAL GROUP, and RansomHub to gain initial access to corporate networks.
FDN3’s other announced prefixes, 92.63.197[.]0/24 and 185.156.73[.]0/24, were previously linked to spam networks like ROZA-AS (AS212283) in Bulgaria, further highlighting the overlap of malicious infrastructure.
Bulletproof Hosting Links
Intrinsec’s investigation concluded that FDN3 and its connected networks are likely run by the same bulletproof hosting administrator. These services often operate through shell companies, including Global Internet Solutions LLC (gir.network), Global Connectivity Solutions LLP, Verasel, IP Volume Inc., and Telkom Internet LTD.
FDN3 also shares ties with Alex Host LLC, a Russian company known for providing infrastructure to malicious actors in the past, including groups that hosted Doppelganger infrastructure.
Offshore Safe Havens
The research emphasizes a recurring problem in cybersecurity: offshore ISPs located in countries like Seychelles enable bulletproof networks by offering anonymity and avoiding accountability. Such setups provide safe havens for malicious actors to continue their operations without direct legal consequences.
Emerging Threats
Parallel to this, Censys uncovered a proxy management system associated with the PolarEdge botnet, which controls more than 2,400 hosts. This system, identified as an RPX server, acts as a reverse-connect proxy gateway to manage proxy nodes and relay services.
While it remains unclear if PolarEdge directly operates the system, researchers believe it could be one of the many tools leveraged by large-scale botnets to maintain resilience.
Conclusion
The discovery of FDN3’s brute-force and password spraying campaigns underscores the evolving nature of cybercrime infrastructure. With bulletproof hosting services providing cover, attackers are able to coordinate cross-border operations that fuel ransomware and malware distribution.
Organizations relying on SSL VPN and RDP systems must adopt stronger authentication, implement geo-blocking, and monitor for suspicious IP traffic to defend against such large-scale brute-force intrusions.
Indicators of Compromise (IOCs)
| Type | Indicator | Description |
|---|---|---|
| Autonomous System (AS) | AS211736 (FDN3) | Ukraine-based, origin of brute-force campaigns |
| Autonomous System (AS) | AS61432 (VAIZ-AS) | Ukraine-based, abusive infra overlap with FDN3 |
| Autonomous System (AS) | AS210950 (ERISHENNYA-ASN) | Ukraine-based, shares prefixes with FDN3 and AS210848 |
| Autonomous System (AS) | AS210848 (TK-NET) | Seychelles-based, bulletproof hosting, overlap with FDN3 |
| Autonomous System (AS) | AS202425 (IP Volume Inc.) | Seychelles-based, Ecatel successor, bulletproof hosting |
| Autonomous System (AS) | AS44446 (SibirInvest OOO) | Russian network, prior announcer of some prefixes |
| Autonomous System (AS) | AS214940 / AS214943 (Virtualine) | U.S.-based bulletproof hosting linked to FDN3 prefix |
| IPv4 Prefix | 185.156.72[.]0/24 | Announced by AS61432 |
| IPv4 Prefix | 45.143.201[.]0/24 | Announced by AS210950 |
| IPv4 Prefix | 185.193.89[.]0/24 | Announced by AS210950 |
| IPv4 Prefix | 88.210.63[.]0/24 | Announced by FDN3, previously Virtualine |
| IPv4 Prefix | 92.63.197[.]0/24 | Announced by FDN3, overlap with AS210848, tied to Bulgarian spam ROZA-AS |
| IPv4 Prefix | 185.156.73[.]0/24 | Announced by FDN3, overlap with AS210848 |
| Related Entity | Alex Host LLC (Russia) | Linked to bulletproof hosting providers like TNSECURITY |
| Infrastructure | PolarEdge Botnet | Proxy management system observed on 2,400+ hosts |
| Infrastructure | RPX server | Reverse-connect proxy gateway tied to PolarEdge botnet |