A serious security flaw has been discovered in the figma-developer-mcp (Model Context Protocol) server, which could allow attackers to execute arbitrary code remotely. Although the issue has now been patched, experts are warning users to update immediately to prevent exploitation.
Details of the Vulnerability
The vulnerability, tracked as CVE-2025-53967 with a CVSS score of 7.5, is classified as a command injection flaw. The problem arises due to unsanitized user input, allowing malicious actors to execute arbitrary system commands on affected servers.
According to a GitHub advisory,
“The server constructs and runs shell commands directly using unvalidated user input, allowing shell metacharacter injection such as
|,>, and&&.”
Successful exploitation could enable attackers to execute remote code under the same privileges as the affected MCP server process.
How the Attack Works
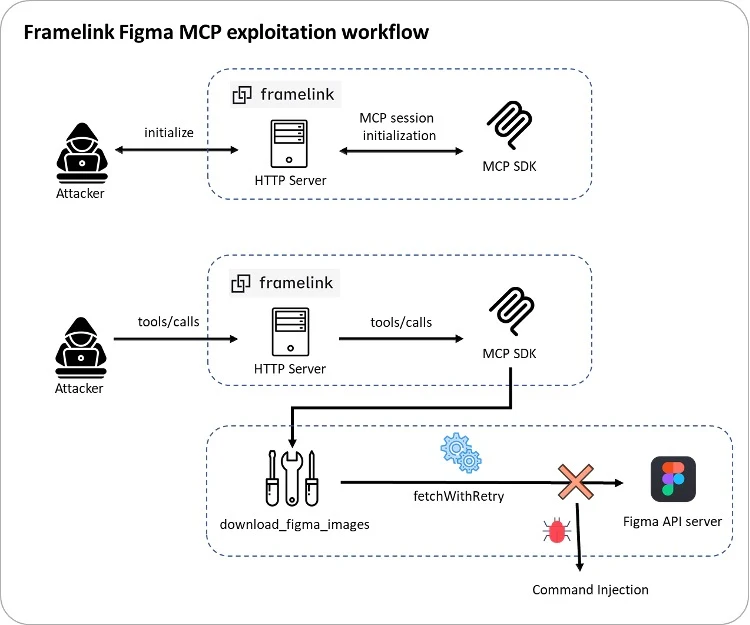
The Framelink Figma MCP server allows various operations within Figma using AI-powered coding agents such as Cursor. By manipulating this feature, an attacker could deceive the MCP client and trigger unintended actions through indirect prompt injection.
Imperva, the cybersecurity company that reported the bug in July 2025, described the flaw as a “design oversight” within the fallback mechanism. It could lead to full remote code execution and potential developer data exposure.
Security researcher Yohann Sillam explained that the issue occurs during command-line construction for sending traffic to the Figma API endpoint.
The attack sequence generally follows these steps:
- The MCP client sends an Initialize request to the MCP endpoint and receives an mcp-session-id for communication.
- It then sends a JSONRPC request with the method
tools/callto execute tools such asget_figma_dataordownload_figma_images.
The vulnerability exists in the “src/utils/fetch-with-retry.ts” file, where the code first tries to fetch content using the standard fetch API. If it fails, it executes a curl command via child_process.exec, which introduces the command injection risk.
Exploitation Scenario
Imperva’s analysis revealed that since the curl command directly interpolates user-supplied URL and header values, an attacker could inject arbitrary shell commands by crafting a malicious URL or header. This could result in remote code execution (RCE) on the host machine.
In a proof-of-concept attack, a remote threat actor on the same network (such as public Wi-Fi or a compromised enterprise device) could exploit the flaw by sending a sequence of requests to the vulnerable MCP server. Attackers could also use DNS rebinding to trick victims into connecting to malicious sites.
Mitigation and Recommendations
The issue has been resolved in figma-developer-mcp version 0.6.3, released on September 29, 2025.
Developers are strongly advised to:
- Upgrade to the latest version immediately.
- Avoid using
child_process.execwith untrusted input. - Use child_process.execFile instead, as it prevents shell interpretation and reduces the attack surface.
According to Thales-owned Imperva,
“As AI-driven development tools continue to evolve, security practices must evolve with them. This flaw highlights how even local tools can become powerful attack vectors if not properly secured.”
Additional Context
In related news, cybersecurity firm FireTail disclosed that Google decided not to patch a newly discovered ASCII smuggling vulnerability in its Gemini AI chatbot. This technique can bypass security filters and cause malicious behavior.
Other large language models (LLMs) affected include DeepSeek and xAI’s Grok.
FireTail warned that,
“This flaw is particularly dangerous when LLMs like Gemini are integrated into enterprise platforms such as Google Workspace. It can lead to identity spoofing and large-scale data poisoning, turning a simple UI flaw into a serious security threat.”


