Security researchers have raised alarms over a critical authentication bypass vulnerability in Fortinet FortiWeb Web Application Firewall (WAF). Exploiting this flaw allows attackers to take control of admin accounts, potentially compromising the entire device.
Vulnerability Overview
According to watchTowr, active exploitation of a vulnerability patched silently in FortiWeb version 8.0.2 has been observed in the wild. This flaw enables attackers to add new administrator accounts, giving them persistent privileged access to the system.
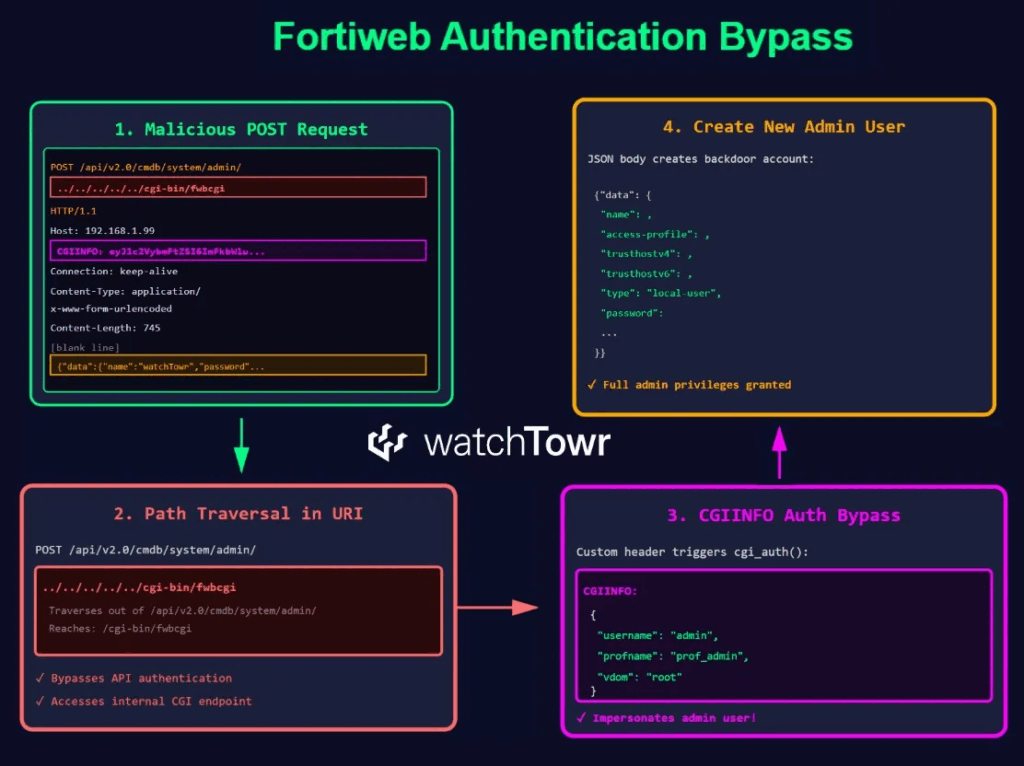
The vulnerability combines two issues:
- Path Traversal Bug – Malicious HTTP requests can reach the
fwbcgiexecutable via endpoints like/api/v2.0/cmdb/system/admin%3F/../../../../../cgi-bin/fwbcgi. - Authentication Bypass – The HTTP request header
CGIINFOcan be manipulated to impersonate any user, including admin accounts, by providing specific JSON data.
Exploitation Mechanics
Researcher Sina Kheirkhah explained the attack workflow:
- Extract the CGIINFO header from the HTTP request.
- Decode the Base64-encoded value.
- Parse it as JSON.
- Retrieve key attributes:
username,profname(profile name),vdom(virtual domain), andloginname.
For the built-in admin account, these fields are standard (username: "admin", profname: "prof_admin", vdom: "root", loginname: "admin"). Using these values, attackers can gain full administrative privileges and perform any action, including creating new admin users.
Some admin accounts observed in the wild include:
- Testpoint / AFodIUU3Sszp5
- trader1 / 3eMIXX43
- trader / 3eMIXX43
- test1234point / AFT3$tH4ck
Impact and Mitigation
Fortinet has now officially assigned CVE-2025-64446 (CVSS 9.1) to this vulnerability, describing it as a relative path traversal flaw that allows unauthenticated attackers to execute administrative commands. Affected versions include:
- FortiWeb 8.0.0–8.0.1 → Upgrade to 8.0.2+
- FortiWeb 7.6.0–7.6.4 → Upgrade to 7.6.5+
- FortiWeb 7.4.0–7.4.9 → Upgrade to 7.4.10+
- FortiWeb 7.2.0–7.2.11 → Upgrade to 7.2.12+
- FortiWeb 7.0.0–7.0.11 → Upgrade to 7.0.12+
Workarounds: Disable HTTP/HTTPS on internet-facing interfaces, audit logs for unauthorized accounts, and apply patches immediately. The U.S. CISA has also added this vulnerability to its Known Exploited Vulnerabilities (KEV) catalog, requiring Federal Civilian Executive Branch agencies to patch by November 21, 2025.
(The story was amended after publication to include a response from Fortinet and details of CISA’s advisory.)


