Fortinet has issued an important warning regarding a newly discovered security flaw in its FortiWeb product. The vulnerability, identified as CVE 2025 58034, has already been exploited in real world attacks, raising concerns for organizations that rely on FortiWeb for application security.
About the Vulnerability
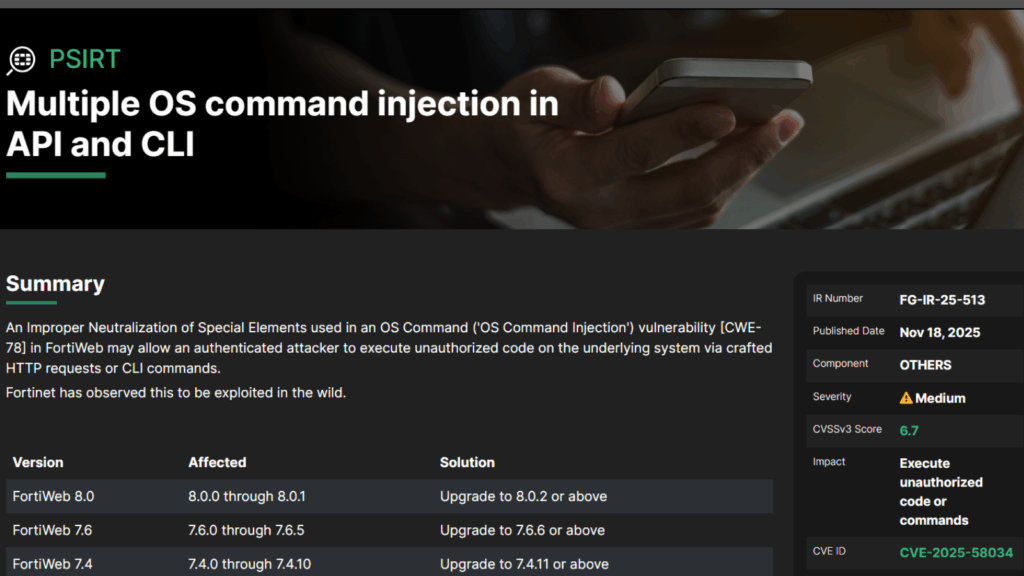
This flaw is rated as medium severity and has a CVSS score of 6.7.
According to Fortinet, the issue is caused by improper neutralization of special elements used in operating system commands. This falls under CWE 78, commonly known as OS command injection.
The vulnerability can allow an authenticated attacker to execute unauthorized code on the underlying system. This is possible through specially crafted HTTP requests or commands entered through the command line interface.
In simpler terms, an attacker must first gain valid authentication by some method, then combine that access with this flaw to run arbitrary system level commands.
Impacted Versions and Fixes
Fortinet has released patches for all affected branches. Users are urged to upgrade to the versions listed below.
Impacted and fixed versions:
• FortiWeb 8.0.0 to 8.0.1, upgrade to 8.0.2 or later
• FortiWeb 7.6.0 to 7.6.5, upgrade to 7.6.6 or later
• FortiWeb 7.4.0 to 7.4.10, upgrade to 7.4.11 or later
• FortiWeb 7.2.0 to 7.2.11, upgrade to 7.2.12 or later
• FortiWeb 7.0.0 to 7.0.11, upgrade to 7.0.12 or later
The vulnerability was reported by Trend Micro researcher Jason McFadyen through Fortinet’s responsible disclosure program.
Silent Patching Raises Concerns
This development follows closely after Fortinet acknowledged that it silently patched another critical FortiWeb flaw, CVE 2025 64446, which holds a CVSS score of 9.1.
A spokesperson stated that the company immediately activated its Product Security Incident Response Team once they became aware of the issue, and that efforts to ensure customer security are ongoing. They emphasized the importance of responsible transparency, although researchers argue that this approach leaves defenders unprepared.
Security analysts at VulnCheck commented that failing to openly communicate new security problems gives attackers an advantage. According to them, withholding information keeps defenders blind while attackers gain insights to exploit vulnerable systems.
CISA Adds the Flaw to the KEV Catalog
The United States Cybersecurity and Infrastructure Security Agency (CISA) has added CVE 2025 58034 to its Known Exploited Vulnerabilities (KEV) catalog. Federal Civilian Executive Branch agencies have been instructed to install the necessary security updates no later than November 25, 2025.