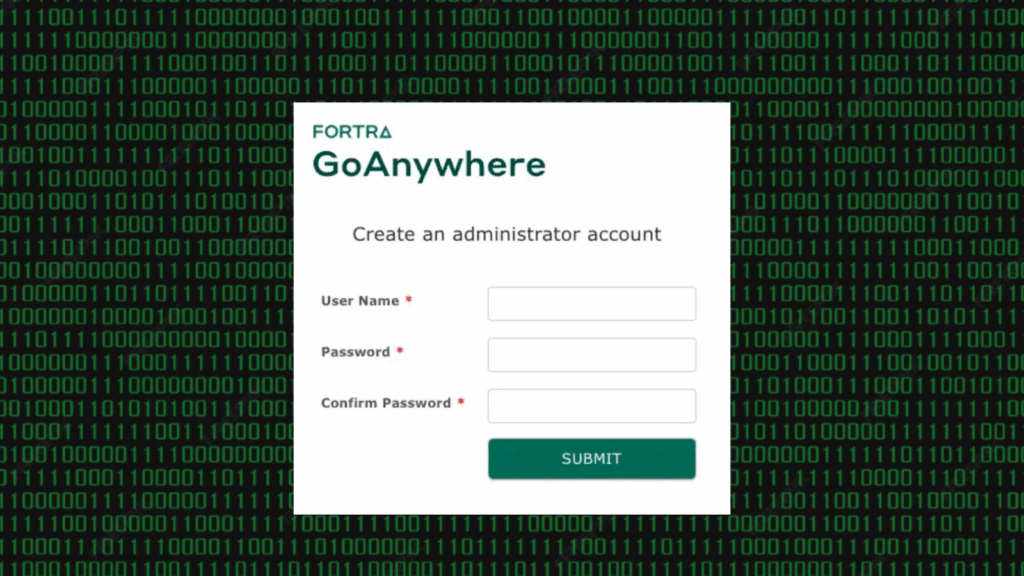
Fortra has officially disclosed the complete timeline of events surrounding the exploitation of CVE-2025-10035, a critical vulnerability in its GoAnywhere Managed File Transfer (MFT) software. The flaw has reportedly been under active attack since at least September 11, 2025.
Investigation and Initial Discovery
According to Fortra, the investigation began on September 11 after a customer reported a potential vulnerability. The internal team quickly discovered suspicious activity linked to the issue and immediately took action.
That same day, Fortra alerted all on-premises customers whose GoAnywhere admin consoles were publicly accessible on the internet. The company also informed law enforcement authorities to begin a coordinated response.
Patch Development and Release
A temporary hotfix addressing the flaw was released the very next day for versions 7.6.x, 7.7.x, and 7.8.x of GoAnywhere MFT.
Full patch releases, labeled versions 7.6.3 and 7.8.4, were made available on September 15. Three days later, the CVE-2025-10035 identifier was officially published, confirming the issue as a tracked vulnerability.
Scope and Security Recommendations
Fortra clarified that only customers with publicly exposed admin consoles are at risk. Other web-based components within the GoAnywhere MFT architecture are not impacted.
The company acknowledged a limited number of unauthorized access reports but assured users that it continues to monitor the situation. As preventive steps, Fortra strongly recommends users to:
- Restrict admin console access from the public internet
- Monitor system activity for any suspicious behavior
- Keep software versions updated to the latest release
Technical Details of CVE-2025-10035
The vulnerability is caused by a deserialization flaw in the License Servlet, which can allow unauthenticated command injection.
Earlier this week, Microsoft reported that the threat group Storm-1175 has been actively exploiting the vulnerability to deploy Medusa ransomware since September 11. However, investigators still do not know how attackers obtained the private keys necessary to exploit this flaw.
Expert Commentary
Benjamin Harris, CEO and founder of watchTowr, commented,
“Fortra’s confirmation of unauthorized activity linked to CVE-2025-10035 proves that this vulnerability is not theoretical. The attackers appear to have bypassed or fulfilled the cryptographic requirements needed for exploitation.”