Cybersecurity firm watchTowr Labs has revealed that attackers began exploiting a severe flaw in Fortra GoAnywhere Managed File Transfer (MFT) software as early as September 10, 2025, a full week before it was publicly disclosed.
According to Benjamin Harris, CEO and Founder of watchTowr, this is not simply a CVSS 10.0 vulnerability in software often targeted by ransomware groups and advanced persistent threat (APT) actors. Instead, it represents an actively exploited weakness with evidence of attacks already in the wild.
The flaw, tracked as CVE-2025-10035, is a deserialization vulnerability in the License Servlet that enables command injection without authentication. Fortra released updates last week, including version 7.8.4 and Sustain Release 7.6.3, to address the issue.
Technical Details
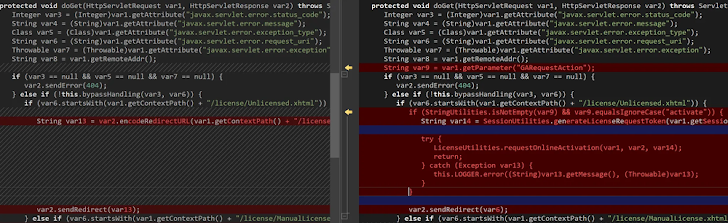
Researchers from watchTowr explained that the problem arises when attackers send a crafted HTTP GET request to the endpoint /goanywhere/license/Unlicensed.xhtml/. This request interacts with the exposed License Servlet (com.linoma.ga.ui.admin.servlet.LicenseResponseServlet) at /goanywhere/lic/accept/<GUID>, using the GUID embedded in the earlier response.
With this bypass, attackers can exploit weak deserialization protections within the License Servlet to achieve command injection. While the exact mechanics remain unclear, researchers Sonny Macdonald and Piotr Bazydlo confirmed that this flaw is critical in nature.
https://attackerkb.com/topics/LbA9ANjcdz/cve-2025-10035/rapid7-analysisCybersecurity company Rapid7 also analyzed CVE-2025-10035, stating that it is not a standalone bug but a chain of three vulnerabilities:
- An access control bypass known since 2023
- Unsafe deserialization (CVE-2025-10035)
- A still-unknown flaw involving attacker access to a private key
Evidence of Exploitation
In a follow-up report, watchTowr shared evidence of exploitation, including a stack trace, which showed attackers creating backdoor accounts. The sequence of activity involved:
- Exploiting the pre-authentication vulnerability to gain remote code execution (RCE)
- Creating a GoAnywhere user named “admin-go”
- Using that account to establish a new web user
- Leveraging the web user to upload and execute additional payloads such as SimpleHelp and an unidentified implant (
zato_be.exe)
The malicious activity was traced to the IP address 155.2.190[.]197, which VirusTotal previously flagged for brute-force attempts against Fortinet FortiGate SSL VPNs in August 2025. However, watchTowr clarified that it has not observed related activity targeting its own honeypots.
Urgent Call to Action
With strong signs of active exploitation, security experts urge all users of Fortra GoAnywhere MFT to immediately apply the latest patches if they have not already done so.
Fortra has yet to release an official statement, but given the seriousness of the flaw, quick remediation is critical to preventing further compromise.


