Over the last week, cybersecurity experts have observed the rise of GlassWorm, a sophisticated malware campaign that targets VS Code extensions available on the OpenVSX Marketplace.
This attack demonstrates a concerning evolution in supply chain security within developer ecosystems.
As of October 2025, more than 35,800 installations have been affected, and the number continues to grow as malicious extensions remain active in the wild.
Severe Impact on Developers
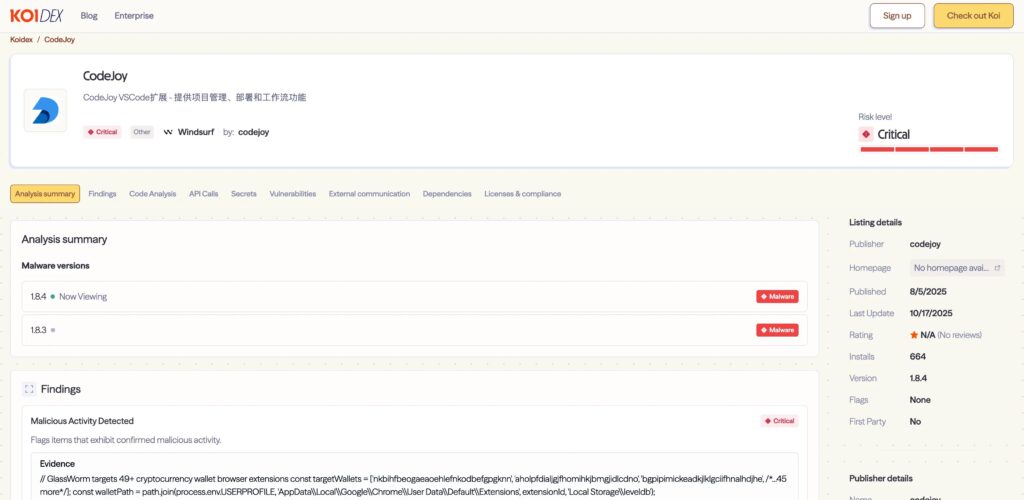
GlassWorm does more than steal credentials—it infiltrates developer machines at a deep level. The first signs appeared when Koi researchers noticed unusual behavior in the seemingly harmless “CodeJoy” extension after version 1.8.3 was released.
Although the extension passed visual code reviews, Koi’s risk detection system flagged anomalous network activity and unauthorized credential access.
Invisible Unicode Hides Malicious Code
The malware uses an innovative infection vector—hidden Unicode characters. These characters make entire blocks of JavaScript invisible in standard editors and most static analysis tools.
This approach allows malicious code to blend seamlessly with legitimate files, remaining undetected during regular inspection.
Self-Propagating Mechanism
Koi’s investigation revealed that GlassWorm harvests secrets from npm, GitHub, OpenVSX, and targets 49 cryptocurrency wallet extensions. After obtaining credentials, it hijacks additional extensions, creating a self-replicating infection cycle.
Compromised devices can then be used as proxy nodes or launchpads for remote attacks, demonstrating a distributed and resilient campaign strategy.
Advanced Command-and-Control Infrastructure
The attackers designed an “unkillable” command-and-control (C2) system using the Solana blockchain. Fallback mechanisms, including Google Calendar events and direct IP connections, make takedown extremely difficult.
All communications carry encrypted instructions, allowing GlassWorm to adapt and update dynamically in real time within compromised networks.
How the Invisible Unicode Works
GlassWorm exploits the Unicode variation selector in JavaScript files, hiding functional logic in non-rendering characters. These are ignored by editors and code review platforms but executed by JavaScript interpreters.
For example, a line that appears empty may contain a full malicious function like:
// Line appears blank but contains:
function stealCreds() {...}This method bypasses conventional code transparency, making it nearly impossible for developers to detect manually. Only specialized tools or byte-level inspections can uncover the hidden logic.
Mitigation for Developers: Updating code inspection tools and CI processes to detect non-standard Unicode characters is now a critical defense priority.