Cybersecurity researchers have uncovered a new wave of the persistent GlassWorm campaign, revealing three malicious Visual Studio Code (VS Code) extensions designed to steal developer credentials and cryptocurrency. With thousands of combined installations, these extensions demonstrate a continued and evolving threat to the software development ecosystem.
The Malicious Extensions and Their Reach
The campaign involves three specific extensions that were available for download on the Open VSX Registry, a popular open-source marketplace for VS Code extensions. The identified packages are:
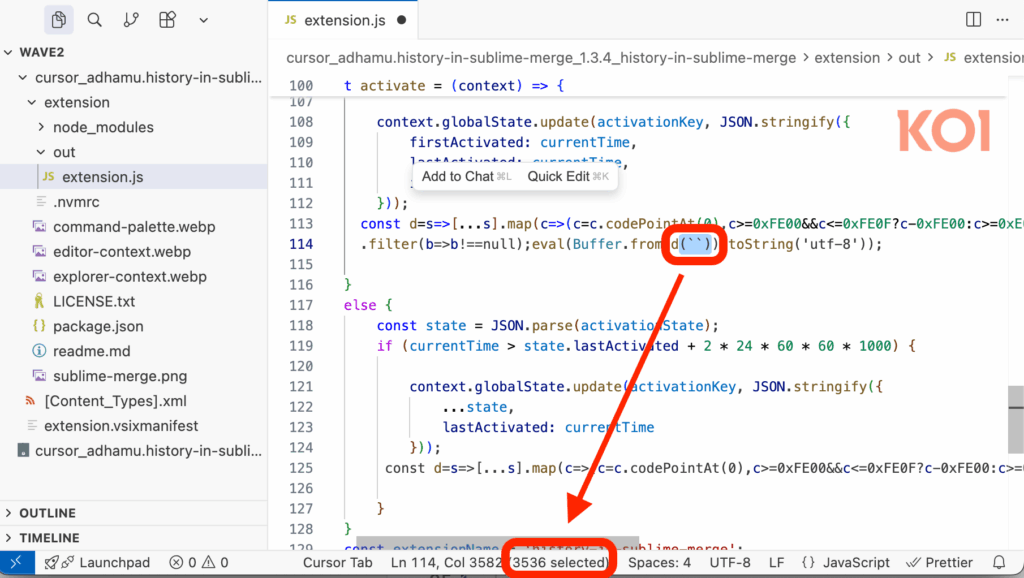
- ai-driven-dev.ai-driven-dev (3,402 downloads)
- adhamu.history-in-sublime-merge (4,057 downloads)
- yasuyuky.transient-emacs (2,431 downloads)
First documented in late October 2025, the GlassWorm campaign uses these extensions as a foothold to harvest credentials from Open VSX, GitHub, and Git accounts. The malware also drains funds from 49 different cryptocurrency wallet extensions and deploys additional tools for remote system access.
Stealthy Techniques and Self-Replication
What makes GlassWorm particularly dangerous is its sophisticated evasion and propagation tactics. The malware uses invisible Unicode characters to hide its malicious code within the extension files, making it extremely difficult for developers to spot the threat during code reviews.
Furthermore, the attackers abuse the stolen credentials to compromise additional developer accounts and extensions. This creates a self-replication cycle, allowing the malware to spread in a worm-like fashion across the ecosystem, much like a digital parasite.
A Resilient and Persistent Threat
Despite initial takedowns by the Open VSX registry on October 21, 2025, the threat has resurfaced. Koi Security’s latest report confirms that the actor is using the same invisible character obfuscation to bypass detection once again.
A key factor in its resilience is the use of blockchain-based command-and-control (C2). The attackers posted a fresh transaction on the Solana blockchain to update the C2 server address. As the researchers noted, “even if payload servers are taken down, the attacker can post a new transaction for a fraction of a cent, and all infected machines automatically fetch the new location.”
Victimology and Actor Clues
An analysis of an inadvertently exposed server endpoint revealed a partial list of victims from the U.S., South America, Europe, and Asia, including a major government entity in the Middle East.
Additionally, keylogger data from the attacker’s own machine provided crucial intelligence. The evidence suggests the threat actor is Russian-speaking and uses an open-source C2 framework called RedExt to manage their malicious browser extensions.
Escalation to Software Supply Chain Attacks
The campaign’s impact continues to grow. Recent findings from Aikido Security show that GlassWorm has expanded its operations to target GitHub directly. The stolen credentials are now being used to push malicious commits to code repositories, a clear escalation into software supply chain attacks that could affect countless downstream projects and users.