Cybersecurity researchers have reported a sharp increase in brute-force traffic targeting Fortinet SSL VPN devices, raising concerns over a possible build-up to a broader exploitation campaign.
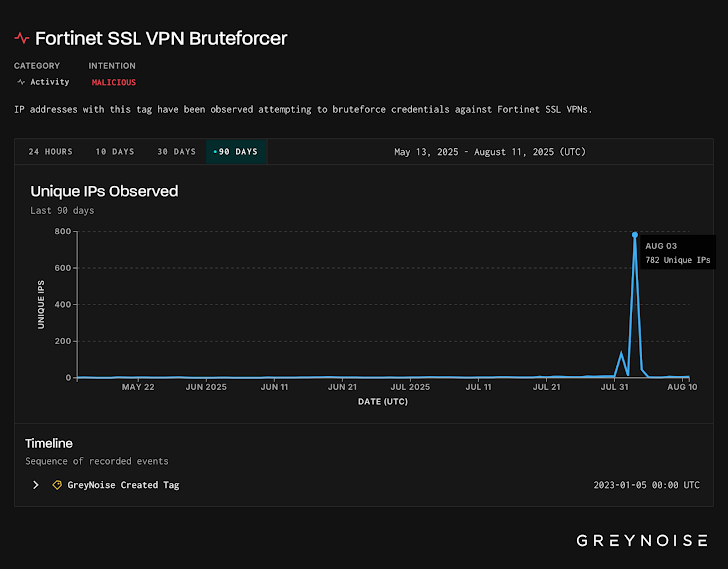
According to threat intelligence firm GreyNoise, the coordinated activity was first detected on August 3, 2025, involving more than 780 unique malicious IP addresses. Within the past 24 hours alone, 56 new IPs have been flagged as hostile, originating from the United States, Canada, Russia, and the Netherlands. The primary targets included organizations in the United States, Hong Kong, Brazil, Spain, and Japan.
Deliberate Targeting of Fortinet Devices
GreyNoise emphasized that the malicious traffic was specifically targeting the FortiOS profile, indicating that this was not random scanning but precise, intentional targeting of Fortinet’s SSL VPN technology.
Researchers identified two distinct attack waves:
- A sustained brute-force campaign linked to a single TCP signature, consistent over time.
- A sudden, high-volume spike with a different TCP signature, suggesting a more aggressive and concentrated assault.
After August 5, the malicious traffic shifted focus. While earlier attacks were aimed at FortiOS, the later wave — identified by TCP and client “meta” signatures — consistently targeted FortiManager, a critical Fortinet service for centralized network management.
Possible Test or Residential Proxy Use
A review of historical data tied to the post-August 5 TCP fingerprint revealed an earlier spike in June 2025, involving a unique client signature that traced back to a FortiGate device hosted on a residential ISP network managed by Pilot Fiber Inc.
This finding suggests two possibilities:
- The brute-force toolset may have been tested or initially deployed from a home network.
- A residential proxy may have been used to obscure attacker infrastructure.
Potential CVE Disclosure Link
The timing of this activity aligns with a well-documented pattern where malicious traffic surges are followed by the disclosure of a new vulnerability (CVE) within six weeks.
GreyNoise highlighted that such patterns are often exclusive to enterprise edge technologies — such as VPNs, firewalls, and remote access tools — which have become prime targets for advanced threat actors.
The situation underscores the importance of proactive monitoring and patch management for organizations using Fortinet products, as attackers may be preparing to exploit newly discovered flaws.


