Cybercriminals linked to the financially motivated group GoldFactory have launched a new wave of mobile attacks across Indonesia, Thailand, and Vietnam by posing as government authorities and local service providers.
According to a technical assessment released by Group IB, the campaign has been active since October 2024 and relies on doctored versions of legitimate banking applications. These altered apps silently install Android malware on victims devices while maintaining much of the original functionality to avoid suspicion.
GoldFactory has been operating since at least June 2023 and was previously associated with custom malware families such as GoldPickaxe, GoldDigger, and GoldDiggerPlus, targeting both Android and iOS platforms. Researchers believe the group is highly organized, Chinese speaking, and closely linked to Gigabud, another Android malware strain identified in mid 2023.
The latest attack wave was first detected in Thailand, later spreading to Vietnam by early 2025 and reaching Indonesia around mid 2025.
Group IB recorded more than 300 variants of modified banking apps, which resulted in nearly 2,200 infections in Indonesia alone. Expanded analysis uncovered over 3,000 malicious artifacts responsible for more than 11,000 total infections. About 63 percent of these tampered apps were aimed at Indonesian users.
The attack pattern remains consistent. Threat actors impersonate local government units or utility companies, contact users by phone, then push them to click links delivered through messaging apps like Zalo. The links redirect to fake Google Play Store pages that distribute malware variants such as Gigabud, MMRat, or Remo.
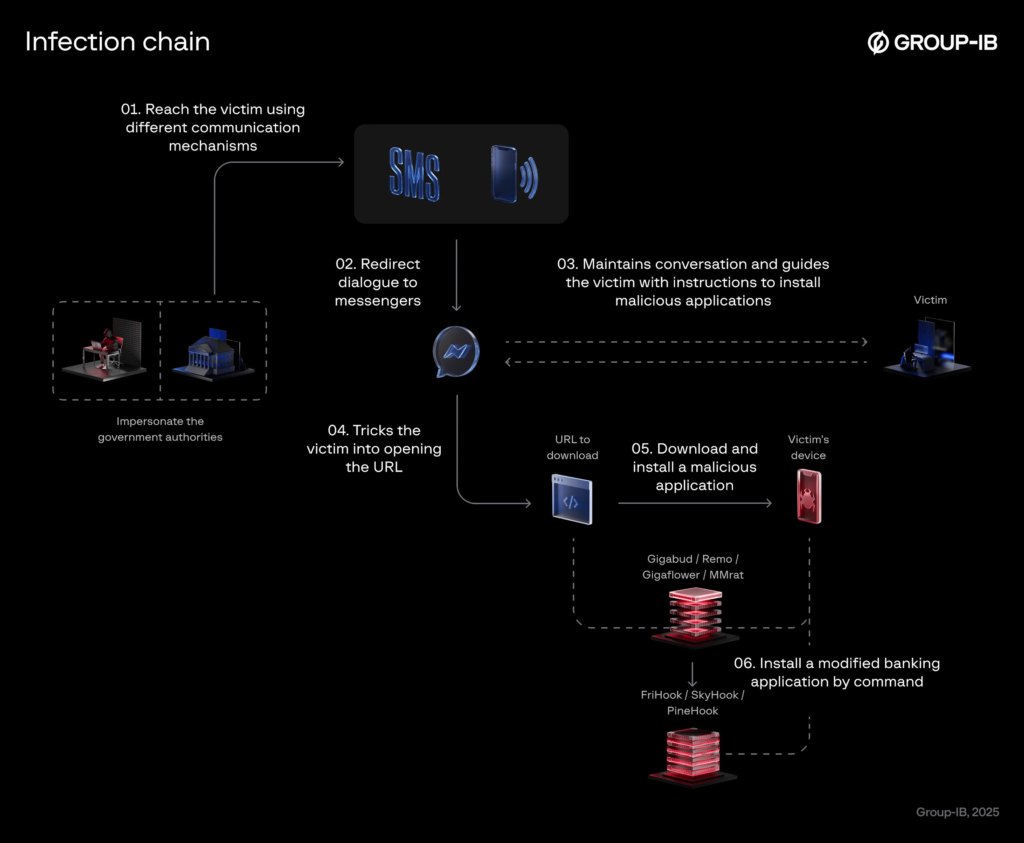
These first stage droppers disguise themselves as trusted mobile apps and then deploy a secondary payload that abuses Android accessibility services, enabling remote device control.
Group IB researchers explained that the malicious modules are injected into portions of real banking apps. This keeps core features intact while allowing the malware to bypass built in security controls. The injected frameworks fall into three main families, FriHook, SkyHook, and PineHook, each using different hooking methods to run malicious routines at runtime.
Despite technical differences, the modules share capabilities that allow attackers to:
Hide accessibility enabled apps
Disable screencast detection
Modify Android app signatures
Conceal installation sources
Generate fake integrity tokens
Access victims banking balances
SkyHook uses the Dobby runtime framework, while FriHook embeds a Frida gadget inside the original app. PineHook relies on the Pine Java hooking framework.
Investigators also discovered a development stage Android malware version named Gigaflower. This advanced variant builds on Gigabud and supports around 48 commands that allow attackers to stream device activity through WebRTC, read interface content, log keystrokes, trigger fake update screens, and extract data from images using an integrated text recognition engine. A QR code scanning feature is currently under development to capture information from Vietnamese ID cards.
Interestingly, GoldFactory appears to have abandoned its former iOS malware approach. Victims are now told to borrow an Android device from a relative to continue the process, a shift likely due to tighter security restrictions and app moderation on iOS devices.
Researchers noted that earlier campaigns targeted KYC verification systems, but the newer attacks manipulate legitimate banking apps directly, enabling much more effective financial fraud. The use of tools like Frida, Dobby, and Pine allows threat actors to scale operations quickly while keeping development costs low.
Found this article interesting? Follow us on Twitter , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


