A new security analysis has revealed that thousands of publicly exposed Google Cloud API keys could be misused to access sensitive Gemini AI endpoints once the Generative Language API is activated within a project.
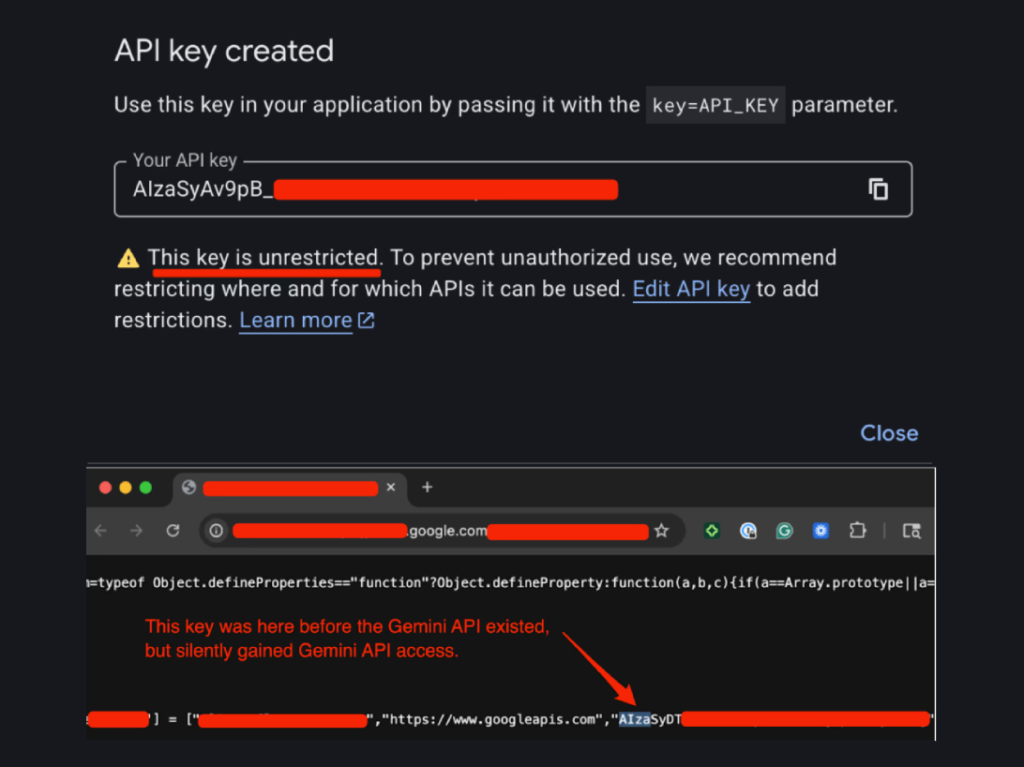
Researchers at Truffle Security identified nearly 3,000 Google API keys, recognizable by the prefix AIza, embedded in client side JavaScript code across websites. These keys are commonly used for services such as embedded maps and other Google integrations. However, once Gemini is enabled in a project, those same keys can silently gain access to powerful AI endpoints.
According to researcher Joe Leon, a valid exposed key could allow an attacker to retrieve uploaded files, access cached data, and generate AI requests billed directly to the victim’s account. The most concerning finding was that these keys were never originally intended to authenticate to Gemini, yet they automatically gained that capability after the API was enabled.
How the Risk Emerged
The issue stems from how Google Cloud handles API permissions. When developers enable the Gemini API, also known as the Generative Language API, existing API keys within that project inherit access without additional warnings. If those keys were already publicly accessible in website code or open repositories, they effectively become live AI credentials.
This opens the door for attackers who scrape websites for exposed keys. Once obtained, they can call Gemini endpoints, access paths such as /files and /cachedContents, and potentially accumulate massive usage charges through automated large language model requests.
Truffle Security reported discovering 2,863 active keys exposed on the public internet, including one associated with a Google related domain.
In a separate investigation, Quokka analyzed 250,000 Android applications and uncovered more than 35,000 unique Google API keys embedded in mobile apps, highlighting the scale of key exposure across ecosystems.
Default Settings Add to the Problem
The research also found that when developers generate a new API key in Google Cloud, the default setting is Unrestricted. This means the key automatically works with every enabled API within the project, including Gemini.
As a result, many API keys originally intended as simple billing identifiers have effectively transformed into credentials capable of accessing advanced AI services.
Security experts warn that the implications go beyond cost abuse. Even if direct customer data is not exposed, AI enabled endpoints may interact with prompts, generated outputs, and connected cloud services in ways that significantly increase overall risk.
Google Responds
Google confirmed it has worked with researchers to mitigate the issue. The company stated that proactive safeguards have been implemented to detect and block leaked API keys attempting to access Gemini services.
At this time, it remains unclear whether the exposure has been widely exploited. However, a recent user post on Reddit claimed that a compromised Google Cloud API key led to more than 82,000 dollars in charges within two days, compared to a typical monthly spend of around 180 dollars.
Mitigation and Best Practices
Organizations using Google Cloud are advised to review their API configurations immediately. Key steps include:
- Checking whether AI related APIs, including Gemini, are enabled
- Identifying publicly accessible API keys in client side code or public repositories
- Rotating exposed keys, beginning with the oldest
- Applying usage restrictions and referrer limits where possible
- Continuously monitoring billing and API activity
Security strategist Tim Erlin of Wallarm emphasized that API risk evolves over time. Even if an API change is not technically a vulnerability, it can increase exposure when permissions expand silently.
Experts stress that organizations must move beyond one time vulnerability scanning and adopt continuous API behavior monitoring, anomaly detection, and active blocking of suspicious activity, particularly as artificial intelligence services become more deeply integrated into cloud environments.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


