Cybersecurity experts have uncovered a large-scale phishing operation in which threat actors abused a legitimate Google Cloud feature to send deceptive emails that appeared to originate directly from Google infrastructure.
According to findings shared by Check Point, attackers misused Google Cloud’s Application Integration service, specifically its built-in email notification capability, to distribute phishing messages from a genuine Google-owned address, noreply-application-integration@google[.]com. This approach allowed the emails to bypass conventional email security controls and reach user inboxes with a high level of trust.
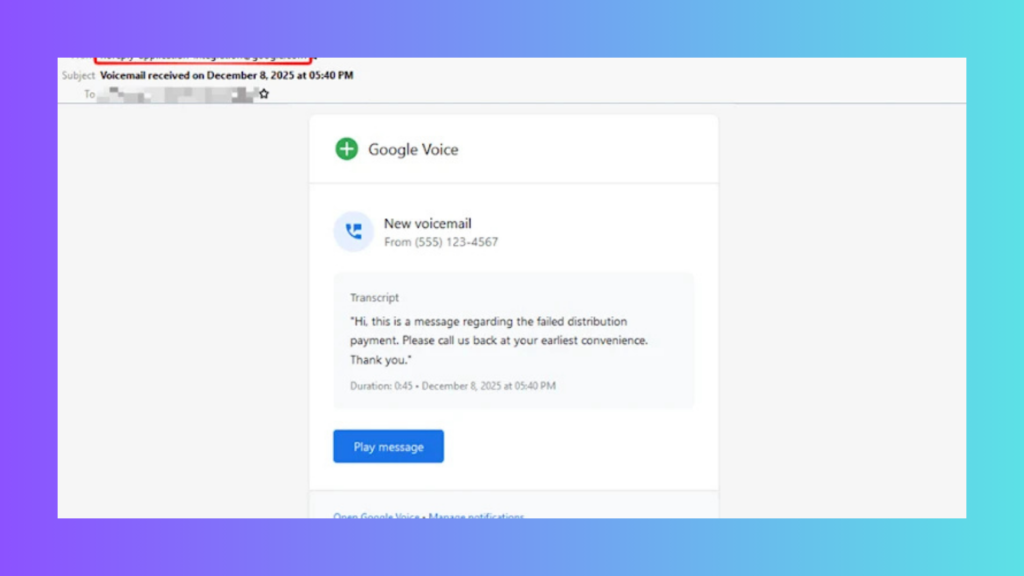
The phishing messages were crafted to resemble standard enterprise alerts, including voicemail notifications and document access or permission requests. By mimicking routine workplace communications, the attackers significantly reduced suspicion among recipients.
Check Point observed 9,394 phishing emails sent to nearly 3,200 individuals over a 14-day period in December 2025. The targeted organizations spanned multiple regions, including the United States, Europe, Asia-Pacific, Canada, and Latin America.
At the core of the campaign was the misuse of the “Send Email” task within Google Cloud Application Integration. While Google documentation limits each task to 30 recipients, attackers leveraged the feature repeatedly to reach a wide audience. The ability to send messages from Google-controlled domains enabled the campaign to effectively evade DMARC and SPF-based email authentication checks.
To further enhance credibility, the phishing emails closely followed Google’s official notification layout, language, and visual structure. Common lures included alerts about newly shared files, such as access to a “Q4” document, or notifications prompting users to review missed voicemails, encouraging immediate interaction.
Once a recipient clicked a malicious link, the attack unfolded through a multi-stage redirection process. The initial link led to content hosted on storage.cloud.google[.]com, a trusted Google Cloud service, helping the attackers maintain legitimacy during the early stages of the attack.
The redirection then moved victims to googleusercontent[.]com, where they encountered a fake CAPTCHA or image-based verification page. This step acted as a filter to block automated security scanners while allowing real users to proceed.
After passing the verification stage, victims were redirected to a counterfeit Microsoft login page hosted on a non-Microsoft domain, where entered credentials were harvested by the attackers.
In response to the discovery, Google confirmed that it has blocked the misuse of the email notification functionality within Application Integration and stated that additional safeguards are being implemented to prevent similar abuse in the future.
Check Point’s investigation revealed that the campaign primarily targeted organizations in the manufacturing, technology, finance, professional services, and retail sectors. However, entities in media, education, healthcare, energy, government, travel, and transportation were also affected.
“These industries frequently depend on automated notifications and shared-document workflows,” Check Point noted. “That reliance makes Google-branded alerts especially convincing and highlights how legitimate cloud automation tools can be repurposed for phishing without traditional email spoofing techniques.”
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.