Google has announced a coordinated effort with industry partners to dismantle the infrastructure of a suspected China linked cyber espionage group identified as UNC2814. The campaign is confirmed to have compromised at least 53 organizations across 42 countries, making it one of the most extensive cyber espionage operations uncovered in recent years.
According to a joint report released by Google Threat Intelligence Group and Mandiant, the threat actor has a sustained record of targeting international government institutions and major telecommunications providers throughout Africa, Asia, and the Americas. Investigators believe additional infections may have occurred in more than 20 other nations.
Long Term Global Cyber Espionage Activity
Google has been tracking UNC2814 since 2017. Over time, analysts observed the group leveraging API calls to communicate with software as a service applications, effectively using them as command and control infrastructure. This technique allows malicious traffic to blend in with legitimate cloud service communications, making detection significantly more difficult.
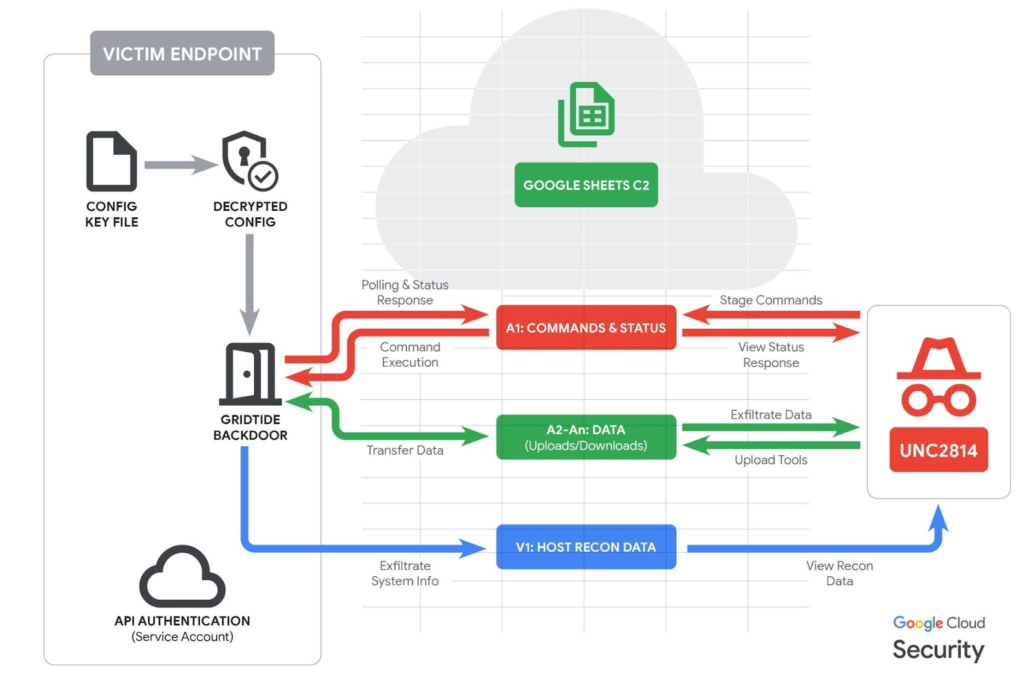
At the center of the campaign is a previously undocumented backdoor known as GRIDTIDE. This C based malware abuses the Google Sheets API as a covert communication channel. By embedding commands and transferring data through spreadsheet cells, the attackers disguised command and control traffic as routine cloud activity.
GRIDTIDE supports file uploads and downloads, remote execution of shell commands, and bidirectional communication between infected systems and attacker infrastructure.
Dan Perez, a researcher at Google Threat Intelligence Group, noted that not all confirmed intrusions can be definitively tied to GRIDTIDE. However, he emphasized that many victim organizations appear to have been compromised for several years without detection.
Infection Methods and Lateral Movement
The exact initial access vector remains under investigation. However, UNC2814 is known for exploiting vulnerable web servers and edge network systems. Once inside, the attackers reportedly used service accounts to move laterally within networks through SSH connections.
The group also relied heavily on living off the land binaries to perform reconnaissance, escalate privileges, and maintain persistence. To ensure long term access, the attackers created a malicious service located at:
/etc/systemd/system/xapt.service
After activation, a new malware instance was executed from:
/usr/sbin/xapt
Another significant component of the operation involved deploying SoftEther VPN Bridge to establish encrypted outbound connections to external infrastructure. The abuse of SoftEther VPN tools has previously been associated with multiple Chinese state aligned threat groups.
Evidence suggests that GRIDTIDE was deployed on systems storing personally identifiable information, indicating a strong focus on intelligence collection and surveillance activities. Despite this, Google stated that it did not observe confirmed data exfiltration during its disruption efforts.
How GRIDTIDE Used Google Sheets for Command and Control
The malware utilized a structured cell polling system within Google Sheets to enable two way communication:
A1 was used to check for attacker commands and overwrite the cell with execution status responses such as Server Command Success
A2 through An were used to transfer command outputs and file data
V1 stored system information collected from the compromised endpoint
This innovative use of legitimate cloud services significantly complicated traditional detection mechanisms.
Infrastructure Takedown and Defensive Measures
As part of the disruption effort, Google terminated all attacker controlled Google Cloud projects, disabled identified UNC2814 infrastructure, blocked malicious accounts, and revoked access to abused Google Sheets API integrations used for command and control operations.
Google described the campaign as one of the most far reaching and impactful cyber espionage operations encountered in recent years. Formal victim notifications have been issued, and support is being provided to organizations with verified compromises.
Ongoing Threat Landscape
The exposure of this campaign highlights a broader pattern of Chinese nation state groups embedding themselves within networks for long term strategic access. It also reinforces the growing risk posed by vulnerable edge devices, which often lack endpoint detection capabilities but provide direct access to internal enterprise environments.
Google warned that the scale of UNC2814’s activity, spanning confirmed or suspected operations in more than 70 countries, represents a serious threat to telecommunications providers and government sectors worldwide. Although rebuilding such an extensive infrastructure will require significant effort, the company expects the threat actor to attempt re establishing its global operational footprint.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


