Cybersecurity experts have uncovered a new malware campaign, codenamed GPUGate, that exploits Google Ads and manipulated GitHub commits to deliver malicious payloads. This operation primarily targets IT and software development companies in Western Europe and has been active since at least December 2024.
Unlike typical malvertising attacks, this campaign introduces a unique twist. The attackers embed a GitHub commit within the page URL, altering the link structure so it redirects users to attacker-controlled sites rather than genuine GitHub repositories. According to Arctic Wolf, “Even when a link looks legitimate, such as GitHub, it can be modified to lead victims to counterfeit domains.”
The malicious download, hosted on a fake domain (gitpage[.]app), is disguised as a 128 MB Microsoft Software Installer (MSI). Its oversized nature helps it bypass most online security sandboxes. Once installed, the malware uses a GPU-based decryption method to keep its payload hidden on systems that lack a real GPU. This tactic effectively filters out virtual machines, older analysis environments, and common sandbox setups used by researchers.
To evade detection further, the installer includes junk files as fillers, terminates if GPU functions are absent, and halts execution if the GPU device name is shorter than 10 characters.
The infection chain continues with a Visual Basic Script that launches a PowerShell script running with administrator rights. This script disables Microsoft Defender protections, establishes persistence through scheduled tasks, and extracts additional executables from a downloaded ZIP file. Ultimately, the malware enables data theft and the deployment of secondary payloads.
Analysis of the attacker’s infrastructure revealed evidence of Atomic macOS Stealer (AMOS) hosting, suggesting that the threat actors are expanding to cross-platform attacks. The presence of Russian-language comments in the code indicates that the operators may be native Russian speakers.
Arctic Wolf highlighted that by exploiting GitHub’s commit structure and abusing Google Ads, adversaries can convincingly impersonate trusted repositories and bypass both human scrutiny and endpoint defenses.
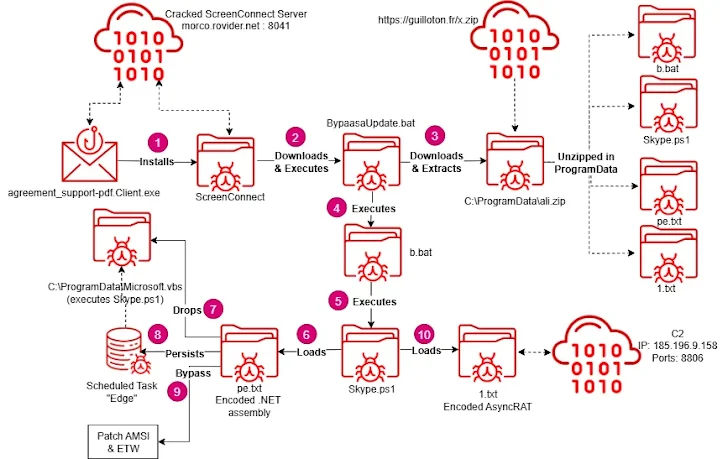
The disclosure also coincides with Acronis’s findings about the continued evolution of a trojanized ConnectWise ScreenConnect campaign targeting U.S. organizations since March 2025. This campaign delivers malware families such as AsyncRAT, PureHVNC RAT, and a custom PowerShell RAT through social engineering techniques. The new version uses a ClickOnce runner installer, which fetches malicious components at runtime instead of embedding them, making traditional detection methods less effective.