Cybersecurity researchers have uncovered an active malware campaign that abuses a DLL side-loading weakness in a legitimate binary linked to the open-source c-ares library. By exploiting this technique, attackers are able to bypass traditional security controls and deliver a wide range of commodity malware, including trojans, stealers, and remote access tools.
How the Attack Works
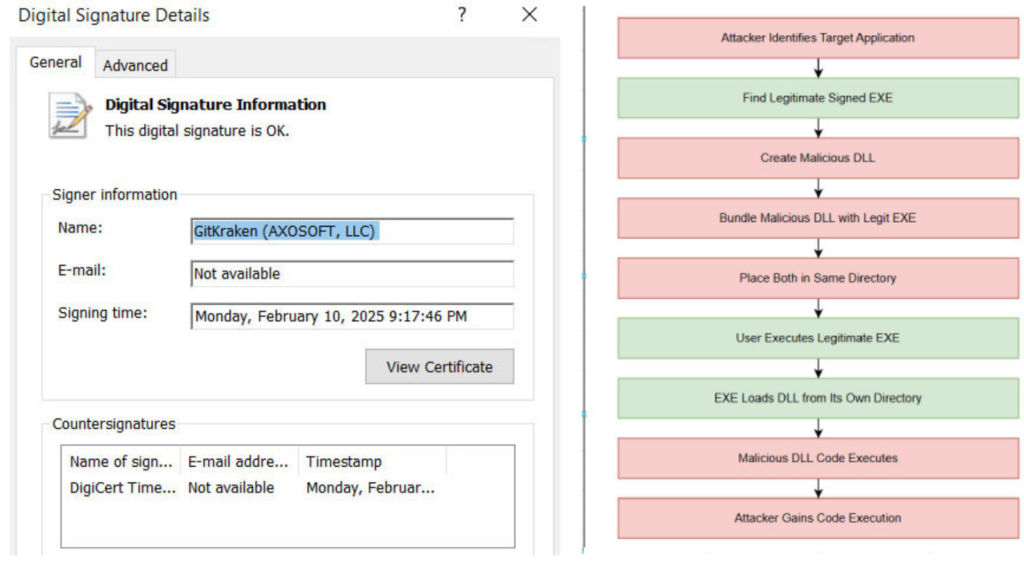
According to researchers, threat actors pair a malicious libcares-2.dll with a legitimate and signed executable called ahost.exe, often renamed to appear harmless. This binary is typically associated with GitKraken Desktop and is digitally signed, making it appear trustworthy to security solutions.
Because the executable is vulnerable to DLL search order hijacking, it loads the malicious DLL placed in the same directory instead of the legitimate one. This allows attackers to achieve code execution without triggering signature-based defenses, effectively bypassing many endpoint protection mechanisms.
Malware Distributed in the Campaign
The campaign has been observed deploying a wide range of malware families, including:
These payloads enable credential theft, data exfiltration, and persistent remote access to compromised systems.
Targeted Sectors and Social Engineering
Targets include employees working in finance, procurement, supply chain, and administrative roles. Affected industries span commercial and industrial sectors such as oil and gas, as well as import and export businesses.
The malicious executables are distributed under convincing filenames that use invoice and RFQ themes, for example fake PDFs or purchase orders. Lures have been observed in multiple languages, including Arabic, Spanish, Portuguese, Farsi, and English, suggesting region-focused targeting.
Abuse of Trusted Software
Analysis of samples shared on VirusTotal shows that the same malicious artifact is distributed under dozens of different names. By abusing a trusted and signed binary like GitKraken’s ahost.exe, attackers significantly increase the likelihood of successful execution.
Researchers warn that this technique highlights the growing threat of DLL side-loading attacks, where legitimate software is misused as a delivery vehicle for stealthy and powerful malware.
Parallel Surge in Facebook Phishing
Alongside the DLL side-loading activity, researchers also reported an increase in Facebook phishing campaigns using the Browser-in-the-Browser (BitB) technique. These attacks simulate a realistic Facebook login pop-up within the victim’s browser using iframes, making fake pages almost indistinguishable from real ones.
The phishing flow often begins with an email impersonating a law firm or legal notice. Victims are redirected through shortened URLs to fake Meta CAPTCHA pages, followed by a BitB-based login window designed to steal credentials.
Other variants rely on alerts about copyright violations, suspicious logins, or account suspension warnings. These phishing pages are commonly hosted on legitimate platforms like Netlify or Vercel, further increasing trust and bypassing filters. Evidence suggests these attacks have been active since at least July 2025.
AsyncRAT Campaign Using Cloudflare Tunnels
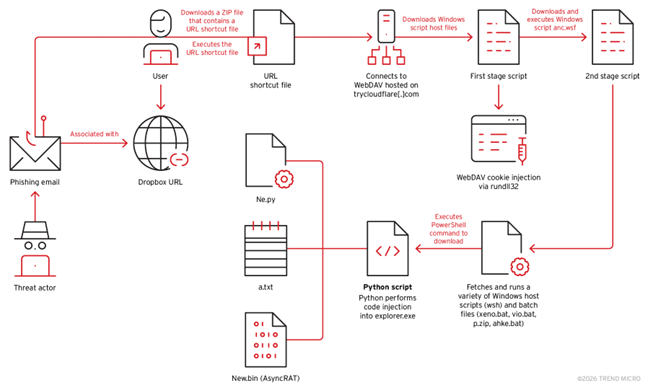
The findings also align with a separate multi-stage phishing campaign distributing AsyncRAT through Python-based payloads and TryCloudflare tunnels. In this campaign, victims receive Dropbox links pointing to ZIP archives containing URL shortcut files.
Once opened, a Windows Script Host file downloads additional scripts from a WebDAV server hosted on Cloudflare’s free-tier infrastructure. These scripts install a Python environment, establish persistence via startup folder scripts, and inject AsyncRAT shellcode into explorer.exe. A decoy PDF is shown to distract the victim and make the activity appear legitimate.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.