In a sophisticated evasion technique, the Russia-aligned threat actor known as Curly COMrades is now exploiting Windows’ native Hyper-V virtualization to create a hidden Linux environment. This covert space is used to host custom malware, effectively bypassing traditional Endpoint Detection and Response (EDR) security measures.
A Hidden Virtual Environment for Stealthy Operations
According to a detailed report from Bitdefender, the attackers enable the Hyper-V role on carefully selected victim systems. Within this virtualized environment, they deploy a minimal, Alpine Linux-based virtual machine that requires only 120MB of disk space and 256MB of memory.
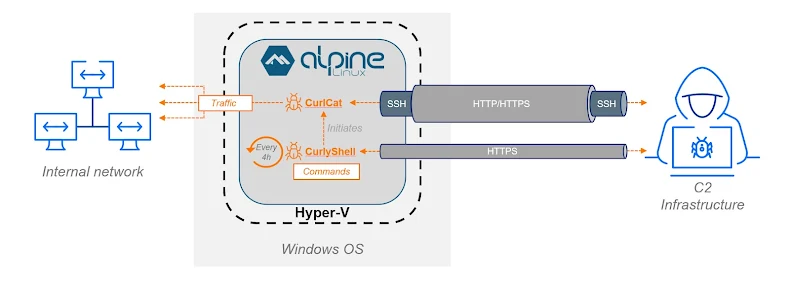
This lightweight, hidden VM serves as a secure operational base, hosting two key custom tools: a reverse shell named CurlyShell and a reverse proxy called CurlCat. By isolating their malicious activities within this virtual machine, the attackers successfully evade many host-based EDR solutions that monitor the primary Windows operating system.
The Curly COMrades Arsenal and Evolution
Curly COMrades was first identified by Bitdefender in August 2025 for its campaigns targeting entities in Georgia and Moldova. The group has been active since late 2023 and is assessed to have interests aligned with Russian strategic goals.
Their toolkit is extensive and includes:
- CurlCat & CurlyShell: Custom tools for bidirectional data transfer and persistent remote access.
- RuRat: A known remote access trojan for maintaining persistence.
- Mimikatz: A credential-dumping tool for harvesting passwords.
- MucorAgent: A modular .NET implant with iterations dating back to November 2023.
A follow-up investigation with Georgia CERT revealed the group’s persistent efforts to establish long-term access, with the Hyper-V method being a key part of their updated strategy.
Sophisticated Tooling for Persistent Control
The threat actors demonstrated a strong determination to maintain their foothold, repeatedly deploying new tools into the compromised environment. Beyond their custom malware, they used a variety of proxy and tunneling utilities like Ligolo-ng, Stunnel, and SSH-based methods.
The centerpiece of their hidden VM operation is CurlyShell, a previously undocumented ELF binary written in C++. It runs as a headless background daemon, connecting to a command-and-control (C2) server to provide a persistent reverse shell.
How the Custom Malware Communicates
Bitdefender’s analysis revealed that CurlyShell and CurlCat share a largely identical codebase but differ in their function. Communication with the C2 server is conducted over HTTP:
- The malware uses HTTP GET requests to poll the server for new commands.
- It then uses HTTP POST requests to send the results of the command execution back to the operators.
This method allows for flexible and encrypted command execution, with CurlyShell running commands directly and CurlCat specializing in funneling traffic through SSH tunnels.