A sharp escalation in hacktivist cyber activity has followed the coordinated U.S. and Israeli military campaign against Iran, known as Epic Fury and Roaring Lion. Cybersecurity analysts warn that the digital battlefield is rapidly expanding alongside physical hostilities, with distributed denial of service, DDoS, campaigns dominating the threat landscape.
According to a new assessment from Radware, two hacktivist collectives, Keymous+ and DieNet, were responsible for nearly 70 percent of all recorded attacks between February 28 and March 2, 2026. The first documented DDoS incident in this wave was launched on February 28 by Hider Nex, also known as Tunisian Maskers Cyber Force.
Emergence of Coordinated Hacktivist Campaigns
Intelligence shared by Orange Cyberdefense identifies Hider Nex as a Tunisian pro Palestine hacktivist group that surfaced in mid 2025. The group blends DDoS disruption with data theft and public leaks, using a hack and leak model to amplify geopolitical messaging.
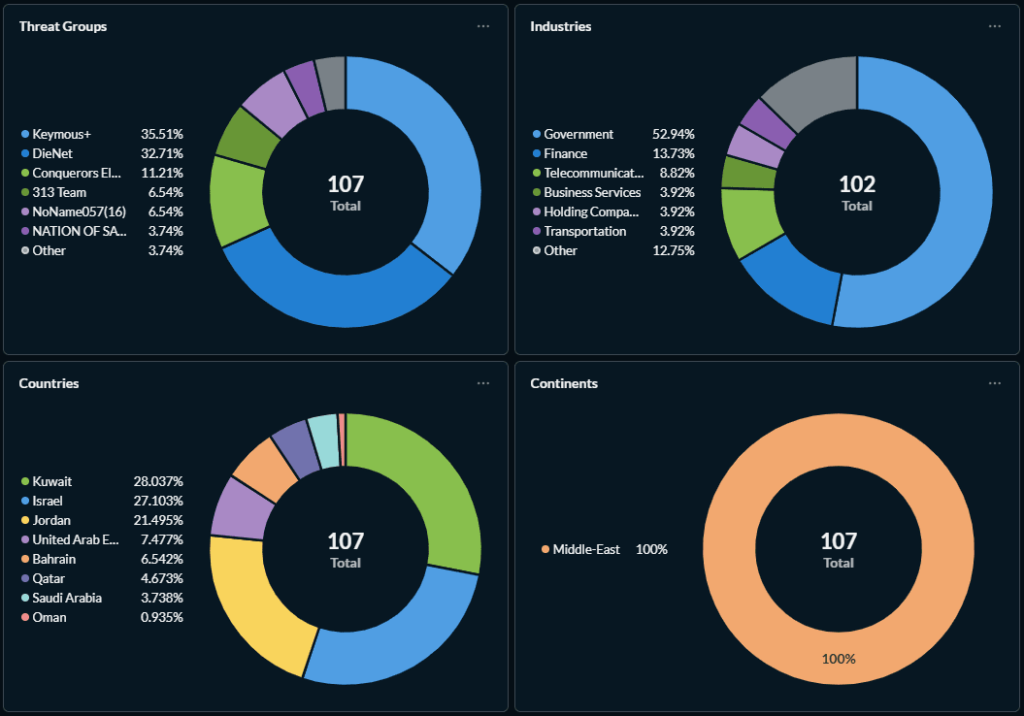
In total, researchers tracked 149 hacktivist DDoS claims targeting 110 organizations across 16 countries. Twelve separate groups were involved, with Keymous+, DieNet, and NoName057(16) collectively accounting for nearly three quarters of the activity.
The Middle East absorbed the majority of attacks, with 107 incidents directed at regional targets. Europe represented 22.8 percent of global activity during the same period. Government entities were the primary victims, comprising 47.8 percent of targets, followed by finance at 11.9 percent and telecommunications at 6.7 percent.
Regional Concentration of Attacks
Radware noted that the distribution of attacks was heavily concentrated in Kuwait, Israel, and Jordan. Kuwait accounted for 28 percent of claims, Israel for 27.1 percent, and Jordan for 21.5 percent.
Security firms including Flashpoint, Palo Alto Networks Unit 42, and Radware confirmed that additional groups such as Nation of Saviors, Conquerors Electronic Army, Sylhet Gang, 313 Team, Handala Hack, APT Iran, Cyber Islamic Resistance, Dark Storm Team, FAD Team, Evil Markhors, and PalachPro participated in disruptive operations.
Broader Cyber Operations and Escalation Indicators
The conflict has triggered more than DDoS activity. Several high impact cyber developments were recorded during this period.
Pro Russian groups Cardinal and Russian Legion claimed breaches of Israeli military systems, including components linked to the Iron Dome missile defense network, though such claims remain unverified.
An SMS phishing campaign was also detected distributing a malicious replica of the Israeli Home Front Command RedAlert mobile application. The campaign delivered surveillance malware by convincing users to sideload a fake emergency update. Threat analysis from CloudSEK suggests the malware masked espionage functionality behind a realistic alert interface.
Iran’s Islamic Revolutionary Guard Corps, IRGC, reportedly targeted regional energy and digital infrastructure. Intelligence from Flashpoint indicates attempts to disrupt Saudi Aramco and an Amazon Web Services data center in the United Arab Emirates, aiming to create economic pressure amid military tensions.
Revival of Legacy Threat Actors
Check Point researchers observed that Cotton Sandstorm, also called Haywire Kitten, reactivated its Altoufan Team persona and claimed website intrusions in Bahrain. Meanwhile, telemetry collected by Nozomi Networks showed that Iranian linked actor UNC1549, also known as GalaxyGato or Nimbus Manticore, ranked as the fourth most active threat group in the second half of 2025. Its focus included defense, aerospace, telecommunications, and government targets.
Sophos reported an increase in hacktivist disruption, particularly from pro Iran personas such as Handala Hack and APT Iran. However, the firm noted no confirmed evidence of widespread compromise escalation.
The National Cyber Security Centre (NCSC) in the United Kingdom issued an advisory warning organizations about heightened Iranian cyber risk, encouraging preparation against DDoS attacks, phishing campaigns, and industrial control system targeting.
Cryptocurrency and Economic Cyber Pressure
Major Iranian cryptocurrency exchanges remained operational but introduced withdrawal limitations and risk advisories due to connectivity concerns. Analysts from TRM Labs described the situation as a stress test of Iran’s shadow crypto economy, which has historically been leveraged to navigate sanctions pressure.
Security company SentinelOne assessed with high confidence that organizations in Israel, the United States, and allied nations are likely to face continued direct or indirect targeting. High risk sectors include government, defense, finance, media, academia, and critical infrastructure.
Strategic Implications and Defensive Measures
Experts emphasize that Iranian cyber actors often blend espionage, disruption, and psychological operations. During instability, these campaigns typically intensify and extend beyond immediate conflict zones.
Organizations are strongly advised to implement continuous threat monitoring, update intelligence signatures, reduce exposed internet facing assets, conduct exposure assessments, verify segmentation between IT and operational technology environments, and isolate IoT devices where possible.
The surge in hacktivist DDoS attacks and hybrid cyber operations underscores how modern conflicts increasingly unfold across both kinetic and digital domains.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


