A newly discovered variant of the Hook Android banking trojan has surfaced with extraordinary capabilities, placing it among the most powerful mobile malware strains identified so far.
Evolution of Hook Trojan
The latest build, called Hook Version 3, marks a major advancement in Android malware technology. It introduces a massive toolkit of 107 remote commands, including 38 brand new features, merging the traits of banking trojans, ransomware, and spyware into one hybrid threat.
Distribution via GitHub
Unlike earlier versions that relied heavily on phishing websites, this new variant also spreads through GitHub repositories. Cybercriminals exploit the platform’s trustworthiness to host and distribute malicious APK files. This strategy makes victims more likely to download infected apps since they appear to come from a credible source.
Researchers also found GitHub being used to distribute other malware families such as Ermac and Brokewell, pointing to a growing malware-as-a-service ecosystem.
Key Advancements Identified by Analysts
Security experts at Zimperium highlighted several cutting-edge capabilities in Hook Version 3:
- Ransomware-like overlays that demand cryptocurrency payments.
- Fake NFC scanning screens designed for fraudulent use.
- Lock screen bypass mechanisms enabling attackers to unlock devices remotely.

At its core, the malware still abuses Android Accessibility Services. However, it now integrates transparent overlays to capture gestures secretly and supports real-time screen streaming, giving hackers near-total control over infected devices.
Overlay Attack Enhancements
The most striking improvement lies in Hook Version 3’s multi-layered overlay attacks that trick users and steal sensitive data.
- Ransomware-style overlays: Full-screen warnings demanding cryptocurrency payments appear, with wallet addresses and amounts fetched dynamically from the attacker’s command-and-control (C2) servers.
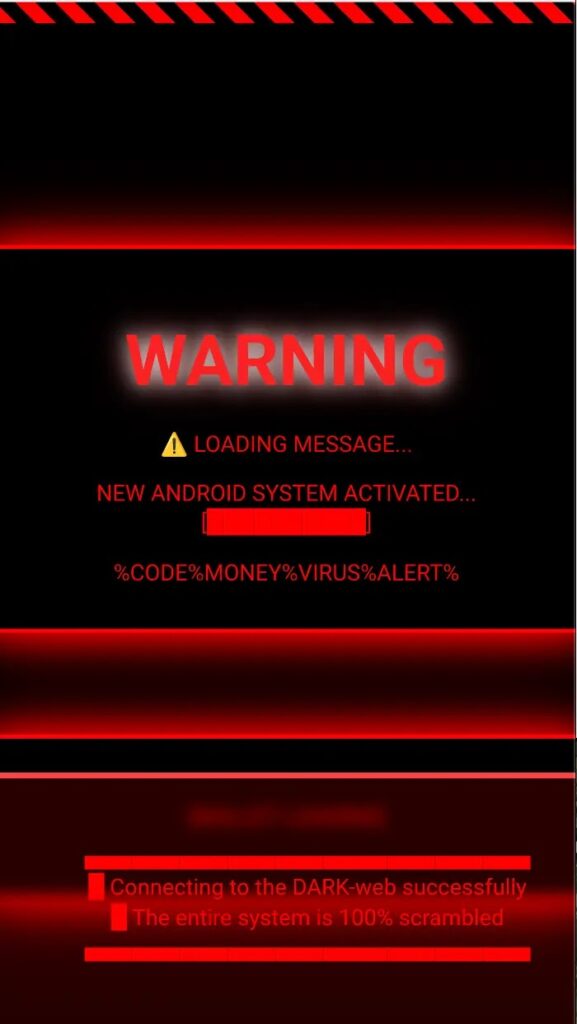
These overlays are powered by embedded HTML inside the APK, allowing instant deployment when the “ransome” command is triggered. Attackers can dismiss it remotely using the “delete_ransome” command.
- Fake NFC overlays: Through the “takenfc” command, Hook displays fraudulent NFC scanning pages using fullscreen WebView overlays.
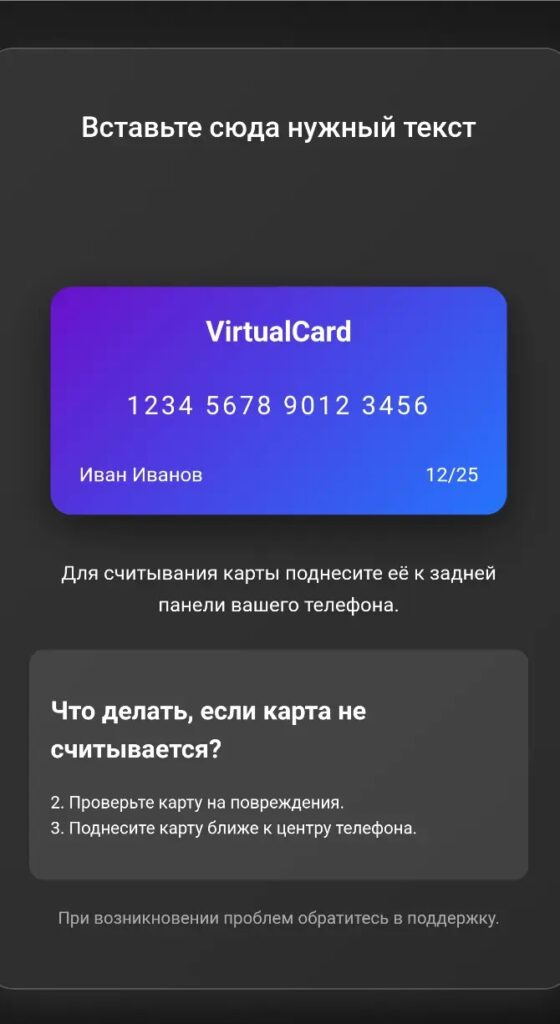
Though not yet fully integrated with JavaScript for data theft, this feature signals ongoing development toward advanced NFC-based phishing attacks.
Lock Screen Bypass Threat
Perhaps the most alarming function is Hook’s ability to bypass device lock screens. Using the “unlock_pin” command, it:
- Gains WakeLock privileges
- Performs swipe-up gestures to display the lock screen
- Enters stolen PINs with simulated button presses
This process effectively breaks through Android’s primary defense, granting attackers unrestricted device access for further malicious operations.