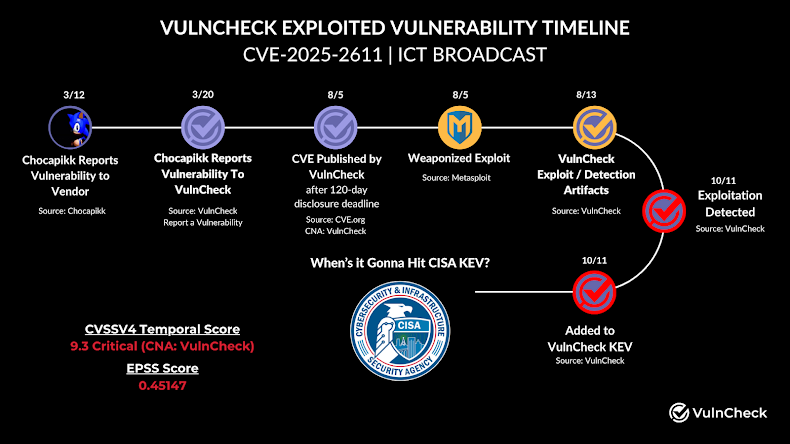
Cybersecurity researchers have reported an active exploitation of a serious security flaw in ICTBroadcast, the autodialer software developed by ICT Innovations.
The vulnerability, tracked as CVE-2025-2611 and assigned a CVSS score of 9.3, arises from insufficient input validation. This flaw allows unauthenticated remote code execution, as the call center application improperly passes session cookie data to shell processing.
As a result, attackers can inject shell commands into session cookies, which are then executed on vulnerable servers. The issue impacts ICTBroadcast versions 7.4 and earlier.
Jacob Baines of VulnCheck explained in a recent alert, “Attackers are exploiting unauthenticated command injection via the BROADCAST cookie to achieve remote code execution. Around 200 online instances are currently exposed.”
The firm reported observing real-world attacks beginning on October 11, which occurred in two stages: an initial time-based exploit check followed by attempts to establish reverse shells.
Threat actors have been injecting Base64-encoded commands, such as one translating to “sleep 3,” into the BROADCAST cookie through specially crafted HTTP requests to verify command execution and set up reverse shells.
Baines added, “The attacker used a localto[.]net URL in the mkfifo + nc payload and connected to 143.47.53[.]106 in other payloads.”
Interestingly, both the localto[.]net URL and the IP address were previously flagged by Fortinet for distributing a Java-based RAT called Ratty RAT, targeting organizations in Spain, Italy, and Portugal.
These overlaps suggest that attackers may be reusing tools or collaborating, VulnCheck noted. At this time, no information is available on whether a patch for this flaw has been released. The Hacker News has contacted ICT Innovations for comment and will provide updates when available.