Israeli organizations across academia, engineering, local government, manufacturing, technology, transportation, and utilities have become targets of a sophisticated campaign by Iranian-linked hackers deploying a new backdoor called MuddyViper.
ESET attributed the attacks to the MuddyWater group, also known as Mango Sandstorm or TA450, linked to Iran’s Ministry of Intelligence and Security (MOIS). One Egyptian technology company was also affected.
Background on MuddyWater
The group first surfaced in November 2017 when Palo Alto Networks Unit 42 documented attacks across the Middle East using a custom backdoor named POWERSTATS. MuddyWater has previously conducted destructive campaigns against Israeli organizations with ransomware variants such as PowGoop, in an operation Quicksand.
According to Israel National Cyber Directorate (INCD), their targets include local authorities, civil aviation, tourism, healthcare, telecommunications, IT, and SMEs.
Attack Methodology
The typical attack chain involves spear-phishing emails and exploiting known VPN vulnerabilities to deliver legitimate remote management tools. Since May 2024, phishing campaigns have been delivering a backdoor named BugSleep (aka MuddyRot).
Other malware and tools used by MuddyWater include:
- Blackout – Remote Administration Tool (RAT)
- AnchorRat – RAT supporting file upload and command execution
- CannonRat – RAT for information exfiltration
- Neshta – File infector virus
- Sad C2 – Command-and-control framework delivering TreasureBox loader and BlackPearl RAT
The attacks usually start with PDF-laden phishing emails linking to legitimate remote desktop tools like Atera, Level, PDQ, and SimpleHelp.
MuddyViper Deployment
The MuddyViper backdoor is executed through a loader named Fooder, capable of decrypting and running C/C++ code. Fooder variants also deploy go-socks5 reverse tunnels and HackBrowserData utility to steal browser data, except Safari on macOS.
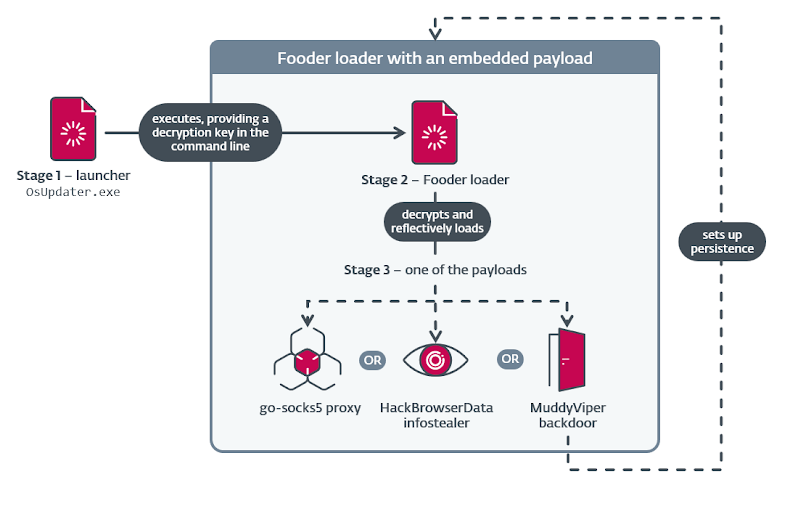
MuddyViper allows attackers to collect system information, execute files and shell commands, transfer files, and steal Windows credentials and browser data. The backdoor supports 20 commands, enabling stealthy system control. Some Fooder versions disguise themselves as the classic Snake game and include delayed execution to evade detection.
Additional Tools Observed
- VAXOne – Backdoor impersonating Veeam, AnyDesk, Xerox, and OneDrive updaters
- CE-Notes – Browser-data stealer bypassing Chrome encryption
- Blub – C/C++ browser-data stealer targeting Chrome, Edge, Firefox, Opera
- LP-Notes – Credential stealer using fake Windows Security dialog
ESET noted that the deployment of MuddyViper and Fooder shows an evolution in operational maturity, enhancing stealth, persistence, and credential harvesting.
Charming Kitten Leaks and Broader Context
The disclosure comes after the Israel National Digital Agency linked APT42, also known as Charming Kitten or Fresh Feline (APT35), to espionage campaigns targeting high-value individuals and organizations.
Anonymous leaks on GitHub by KittenBusters revealed internal Iranian operations, including the leadership of Abbas Rahrovi (aka Abbas Hosseini) and front company networks managing operations. Source code for BellaCiao malware, used globally in attacks, was also exposed.
DomainTools described the leak as evidence of a structured, bureaucratic cyber-intelligence organization with defined hierarchies, workflows, and performance monitoring. Clerical staff log activity, measure phishing success, and track reconnaissance, while technical teams weaponize exploits for active vulnerabilities.
Found this article interesting? Follow us on Twitter , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


