Cybersecurity researchers have exposed a cybercriminal group, known as Jingle Thief, that targets cloud systems used by retailers and consumer service companies, to carry out large scale gift card fraud. The group focuses on stealing credentials through phishing and smishing, then uses those credentials to access cloud-based gift card issuance workflows, issue high value cards, and monetize them on gray markets.
How Jingle Thief Operates, and why gift cards are attractive
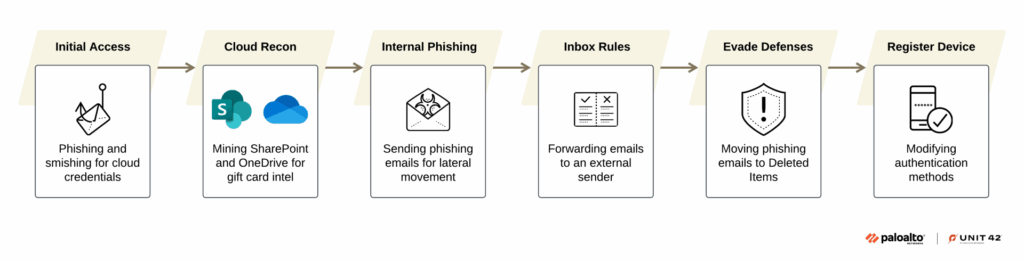
Jingle Thief uses targeted email phishing and SMS based smishing campaigns to harvest employee credentials, often fooling victims into entering Microsoft 365 login details on convincing fake pages. With those credentials, the attackers log into cloud environments, and carry out detailed reconnaissance, searching SharePoint and OneDrive for documentation about gift card issuance, VPN setups, internal spreadsheets, and operational workflows. Gift cards are lucrative because they can be redeemed with little personal information, are hard to trace, and can be resold quickly, which makes investigation and recovery difficult.
Attack lifecycle, persistence, and identity misuse
After initial access, the group moves laterally inside the cloud environment, mapping services and accounts, and escalating privileges as needed to reach gift card issuance systems. In some cases, Jingle Thief has kept access for many months, sometimes over a year, enabling them to break into dozens of accounts within a single organization. The actors prefer identity misuse, rather than custom malware, to reduce detection risk, they create inbox rules to forward messages, they delete or move sent items to hide traces, and they may register rogue authenticator apps or enroll devices in Entra ID, so they can remain connected even after passwords are reset or sessions are revoked.
Targeting methods, internal phishing, and stealth techniques
The actors tailor their attacks to each victim, using reconnaissance to craft persuasive phishing pages and internal messages that mimic legitimate IT notifications or ticket updates. They often use information found in internal documents to add credibility. Once inside, they send phishing messages from compromised accounts to expand their foothold, and they set automatic forwarding rules to siphon communications to addresses they control, while covering tracks by moving or deleting evidence.
Recent activity and attribution
Researchers observed a surge of coordinated attacks in April and May 2025, where attackers used phishing to gain the credentials needed to access cloud infrastructure, and maintained long term footholds in several victims. The activity cluster is tracked by some firms as CL, CRI, or under names like Atlas Lion and Storm-0539. Microsoft attributes a financially motivated group to Morocco, which appears to be active since at least late 2021. The moniker Jingle Thief reflects the group’s tendency to time fraud around holiday seasons, to maximize gift card exploitation.
Why this is dangerous for organizations
Because Jingle Thief focuses on cloud identities and issuance workflows, it can issue large volumes of high value gift cards with minimal logging, which complicates incident response and forensic analysis. Persistent access, careful reconnaissance, lateral movement, and identity-based evasion make these campaigns both scalable and stealthy. Gift card fraud therefore combines high rewards with low visibility, posing a serious threat to retailers and any organization that issues digital value instruments.
Mitigations, practical defenses, and recommendations
- Enforce strong multi factor authentication, however monitor for unauthorized authenticator registrations or Entra ID enrollments, and block suspicious registrations.
- Limit and monitor administrative and issuance privileges for gift card systems, apply least privilege, and require approval workflows for high value issuance.
- Harden Microsoft 365, SharePoint, and OneDrive, enable logging and retention for audit trails, and monitor for unusual access patterns.
- Detect and block phishing and smishing campaigns with email filtering, URL inspection, and user awareness training.
- Regularly review mailbox rules and forwarding settings, and alert on new automatic forwards or mass rule changes.
- Maintain robust incident response plans for cloud identity compromise, including credential rotation, session revocation, and forensic preservation.
These steps help reduce exposure, increase detection chances, and limit the impact of gift card fraud.


