A new Android malware campaign linked to the North Korean threat actor Kimsuky has been uncovered, using QR code based phishing techniques to distribute an updated variant of malware known as DocSwap. The activity was analyzed by South Korean cybersecurity firm ENKI, which reported that the attackers are impersonating a major logistics provider in South Korea to deceive victims.
According to the findings, the malicious QR codes are hosted on phishing websites designed to closely mimic the branding of CJ Logistics, previously known as CJ Korea Express. Victims are lured through pop up notifications and messages that prompt them to install what appears to be an official shipment tracking application on their Android devices.
Researchers explained that the attackers exploit Android’s default security warnings, which block apps from unknown sources. To bypass this protection, the malicious app is presented as a legitimate and safe release, persuading users to ignore the warnings and proceed with the installation.
Some of the malware samples are disguised as package delivery applications. ENKI assesses that the campaign is likely initiated through smishing messages or phishing emails that impersonate delivery companies. These messages direct recipients to malicious URLs hosting the fake applications.
A notable feature of the campaign is its QR code based redirection mechanism. When the phishing URL is accessed from a desktop system, users are shown a QR code and instructed to scan it using their Android device. This step leads them to download a supposed shipment tracking app and check delivery status directly on their phone.
The QR code redirects users to a tracking.php script that performs server side checks on the browser User Agent. Based on this information, the page displays a message instructing the user to install a so called security module, claiming it is required for identity verification due to international customs security policies.
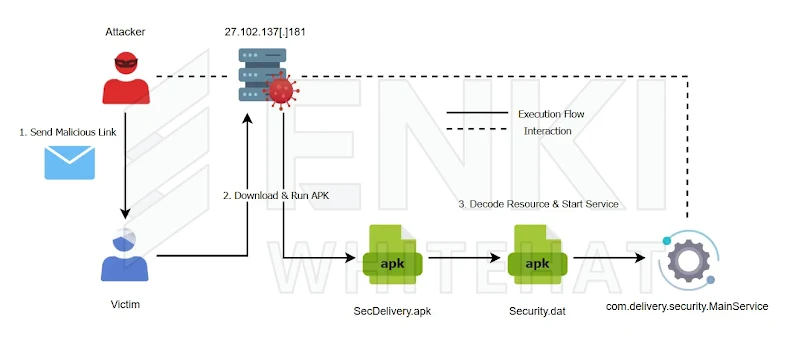
If the victim proceeds, an APK file named SecDelivery.apk is downloaded from a remote server. Once installed, the application decrypts and loads an encrypted APK embedded within its own resources, launching a new variant of the DocSwap malware. Before activation, the malware verifies that it has permissions to manage external storage, access the internet, and install additional packages.
After confirming permissions, the malware registers a background service under the name com.delivery.security.MainService. At the same time, it launches an authentication screen that masquerades as an OTP verification process. Victims are asked to enter a delivery number, which is hard coded inside the application.
Once the delivery number is submitted, the app generates a random six digit verification code and displays it as a notification. The user is then prompted to re enter this code, creating the illusion of a legitimate identity check. Following this step, the app opens a legitimate CJ Logistics tracking webpage to avoid suspicion.
In the background, however, the malware establishes a connection to an attacker controlled command and control server. Through this channel, the threat actor can issue dozens of commands, enabling full remote access. The capabilities include keystroke logging, audio capture, camera control, file operations, command execution, file transfer, and the collection of sensitive data such as location information, SMS messages, contacts, call logs, and installed applications.
ENKI also identified additional malicious samples posing as a P2B Airdrop application and a trojanized version of a legitimate VPN app called BYCOM VPN, which is officially available on the Google Play Store and developed by Bycom Solutions. This suggests that the attackers injected malicious code into a genuine APK and repackaged it for use in the campaign.
Further investigation into the infrastructure revealed phishing websites imitating popular South Korean platforms such as Naver and Kakao. These sites were designed to steal user credentials and were found to overlap with earlier Kimsuky credential harvesting operations.
ENKI concluded that while the malware continues to deploy remote access trojan functionality similar to previous campaigns, it demonstrates clear evolution. The latest variant introduces new native decryption routines and enhanced decoy techniques, making detection and user awareness significantly more challenging.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


