Cybersecurity researchers have uncovered large scale activity linked to an Android botnet known as Kimwolf, which has compromised more than two million devices by abusing exposed Android Debug Bridge (ADB) services and tunneling through residential proxy networks. The findings were revealed in a recent analysis by Synthient.
According to researchers, threat actors operating the Kimwolf botnet are actively monetizing their access by forcing app installations, selling residential proxy bandwidth, and offering distributed denial of service (DDoS) attack capabilities to third parties. This multi layered monetization strategy highlights the growing commercialization of Android based botnets.
Kimwolf was first publicly documented last month by QiAnXin XLab, which identified its technical and operational links to another botnet known as AISURU. Active since at least August 2025, Kimwolf is believed to be an Android focused variant of AISURU. Researchers have also found increasing evidence suggesting the botnet may be responsible for several record breaking DDoS attacks observed toward the end of last year.
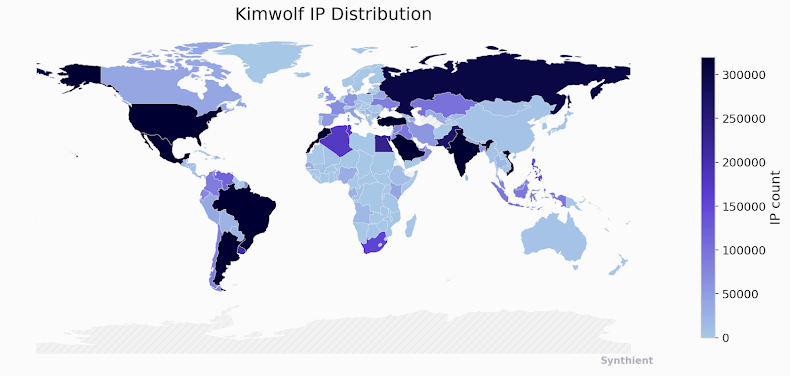
Once a device is infected, the malware converts it into a relay point for malicious traffic and uses it to participate in large scale DDoS operations. Synthient reports that infections are heavily concentrated in Vietnam, Brazil, India, and Saudi Arabia, with approximately 12 million unique IP addresses associated with the botnet observed every week.
The infection chain primarily targets Android devices that expose their ADB service to the internet. Attackers use scanning infrastructure backed by residential proxies to locate vulnerable systems and silently install the malware. Analysis shows that at least 67 percent of the devices connected to the botnet have unauthenticated ADB enabled by default, making them easy targets.
Researchers suspect that many of these devices are shipped pre infected with software development kits from proxy providers, allowing threat actors to enroll them into the botnet without user awareness. Unofficial Android based smart TVs and set top boxes are among the most commonly compromised devices.
As recently as December 2025, Kimwolf operators were observed leveraging proxy IP addresses rented from China based provider IPIDEA. The company implemented a security patch on December 27 to block access to local network devices and sensitive ports. IPIDEA markets itself as a global IP proxy provider, maintaining millions of frequently updated IP addresses worldwide.
Investigators believe the attackers abuse IPIDEA and similar proxy networks to tunnel into local environments where proxy software is installed, enabling malware delivery from within trusted networks. The main Kimwolf payload listens on port 40860 and connects to 85.234.91[.]247:1337 to receive commands from its control infrastructure.
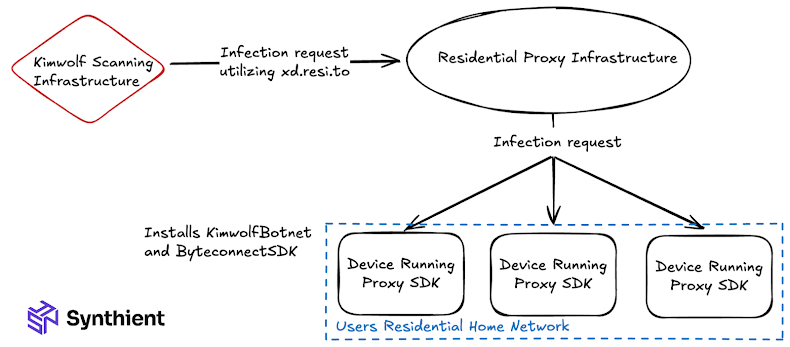
Synthient described the exposure created by this technique as unprecedented, stating that millions of devices were left open to exploitation. Beyond DDoS activity, the infected systems are also enrolled into a bandwidth monetization service called the Plainproxies Byteconnect SDK. This SDK relies on 119 relay servers that distribute proxy tasks from a central command server to compromised devices.
The same infrastructure has been observed conducting credential stuffing attacks against IMAP servers and widely used online platforms. Researchers noted that Kimwolf’s aggressive pricing model, offering residential proxies for as little as $0.20 per gigabyte or around $1,400 per month for unlimited bandwidth, helped drive early adoption among proxy resellers.
Security experts warn that the discovery of pre infected TV boxes and the use of secondary monetization SDKs such as Byteconnect point to an increasingly close relationship between cybercriminal groups and commercial proxy providers.
To reduce the risk, proxy service operators are advised to block access to RFC 1918 private IP address ranges. Organizations and users are also urged to secure Android devices by disabling unauthenticated ADB access and restricting unnecessary network exposure.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


