A North Korea linked actor known as Konni, also tracked as Earth Imp, Opal Sleet, Osmium, TA406, and Vedalia, has run targeted campaigns that compromise Android and Windows systems, steal credentials, and gain remote control of victims’ devices. Researchers at the Genians Security Center say the group used social engineering to distribute malware disguised as stress relief apps, and crucially abused Google’s Find Hub service to remotely reset and erase devices, a technique observed in early September 2025.
Infection chain and social engineering tactics
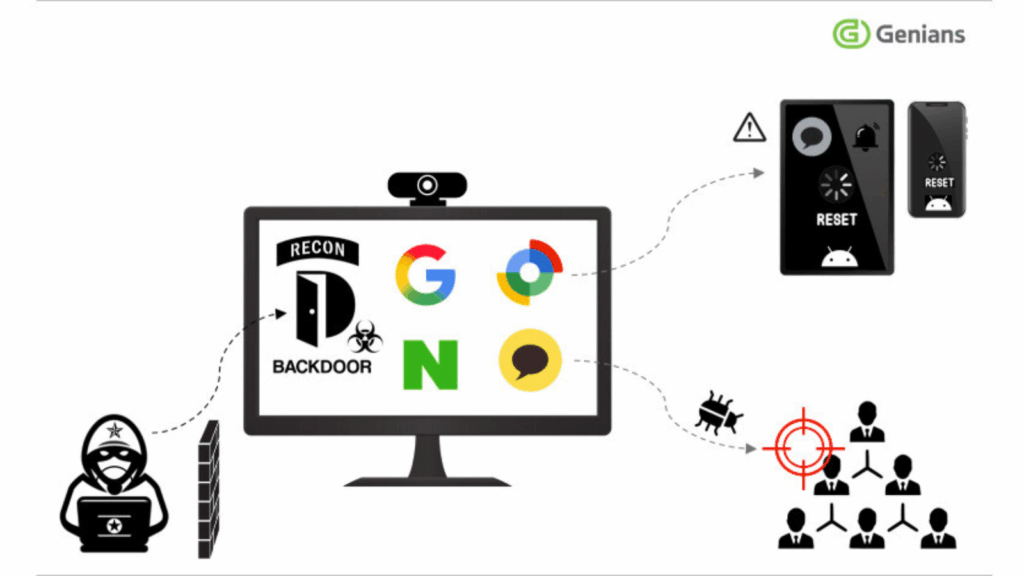
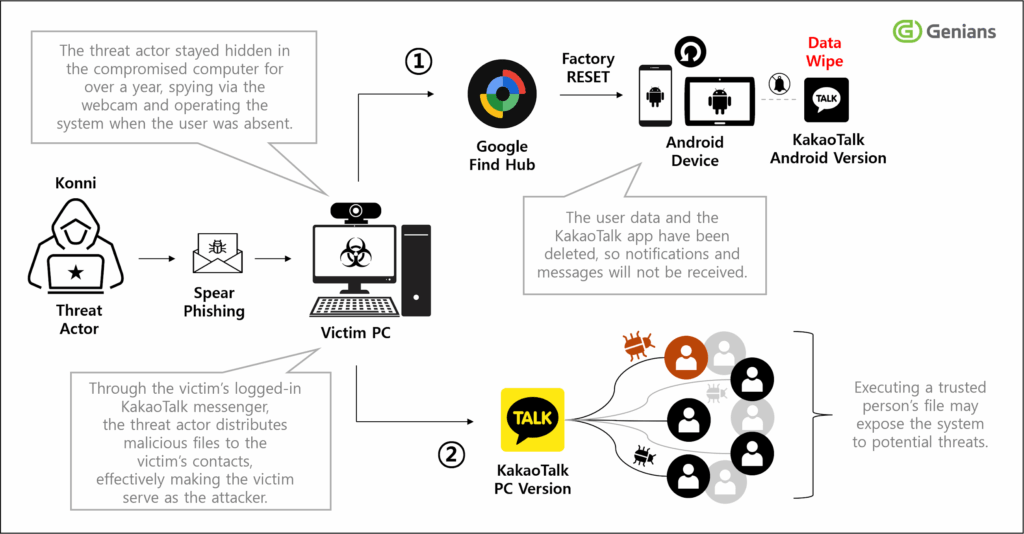
Operators behind the campaign impersonated counsellors and North Korean human rights activists to trick victims into installing what looked like benign stress relief tools. Initial access often came from spear phishing, where messages mimicked trusted institutions such as tax authorities and delivered malicious attachments. Once a victim executed the payload, the attackers used persisted access on compromised PCs to harvest credentials and spread malicious ZIP files via logged in KakaoTalk sessions to the victim’s contacts.
The ZIP archive includes a signed Microsoft Installer package named Stress Clear.msi, which abuses a legitimate digital signature from a Chinese firm to appear authentic. When run, the installer launches scripts and VBScript that display a fake compatibility error while running hidden commands, including an AutoIt script scheduled to run every minute. That AutoIt component communicates with a remote server at 116.202.99[.]218 to fetch and execute further instructions.
Remote wipe via Find Hub, credential theft, and cleanup tactics
With Google account credentials stolen from victims, Konni operators logged into Google’s Find Hub, and initiated remote device resets that result in the deletion of personal data. In one case the attackers also used a recovery account on Naver to delete Google security alert emails and emptied trash folders to erase traces of their actions.
The attackers combined long term stealth on infected systems with active surveillance, spying through webcams and controlling machines when users were away, according to Genians. The campaign shows how credential theft enabled by PC malware can be weaponized against mobile devices by abusing legitimate account management features.
Malware family details and capabilities
Although some components resemble Lilith RAT, researchers labeled the Windows payload EndRAT, sometimes called EndClient RAT, to reflect observed differences. EndRAT supports a wide set of commands, for example, shellStart, shellStop, refresh, list, goUp, download, upload, run, delete, enabling remote shells, file exfiltration, execution, and file removal. Genians also observed the adversary deploying Remcos RAT version 7.0.4, released on September 10, 2025, as well as Quasar RAT and RftRAT, indicating the actor uses multiple trojans and keeps current with newer tool releases.
Additionally, the campaign leverages staged droppers and scheduled tasks to ensure persistence and periodic execution, while hiding malicious activity behind seemingly benign user prompts.
Related activity from other North Korea linked actors
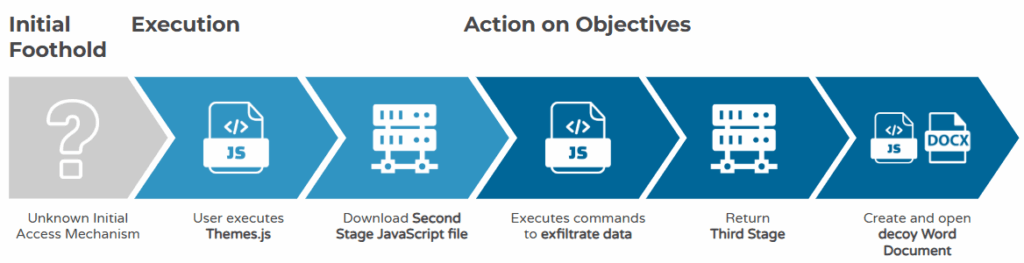
The report arrived alongside separate disclosures about Lazarus Group using an updated Comebacker loader in targeted lures against aerospace and defense entities, and Kimsuky deploying a new JavaScript based dropper that fetches additional payloads and creates scheduled tasks, possibly using an empty Word document as a decoy. These findings underline an active period of tailored espionage efforts across the region.
Vendor response and recommendations
Google told The Hacker News that no Android or Find Hub vulnerability was exploited, and that these attacks depended on PC malware to steal Google credentials before abusing legitimate account controls. Google recommended enabling 2 Step Verification or passkeys, and advised high risk users to enroll in Google’s Advanced Protection Program.
To reduce exposure, organizations and individuals should, at minimum, enable multi factor authentication on accounts, apply strict endpoint protections and application allow listing, keep software and signature checks current, limit use of recovery accounts that share contact email infrastructure, and educate users to avoid opening suspicious attachments or running signed installers that arrive unexpectedly. Monitoring for unusual account activity and promptly responding to suspicious login notifications also helps limit abuse of account management services like Find Hub.