Security researchers have published a full proof-of-concept exploit for a serious vulnerability in the Linux kernel ksmbd module, showing a reliable route to local privilege escalation. The issue, tracked as CVE-2025-37947, is an out-of-bounds write that an authenticated local user can abuse to gain full root control on affected systems.
What the bug is, and where it lives
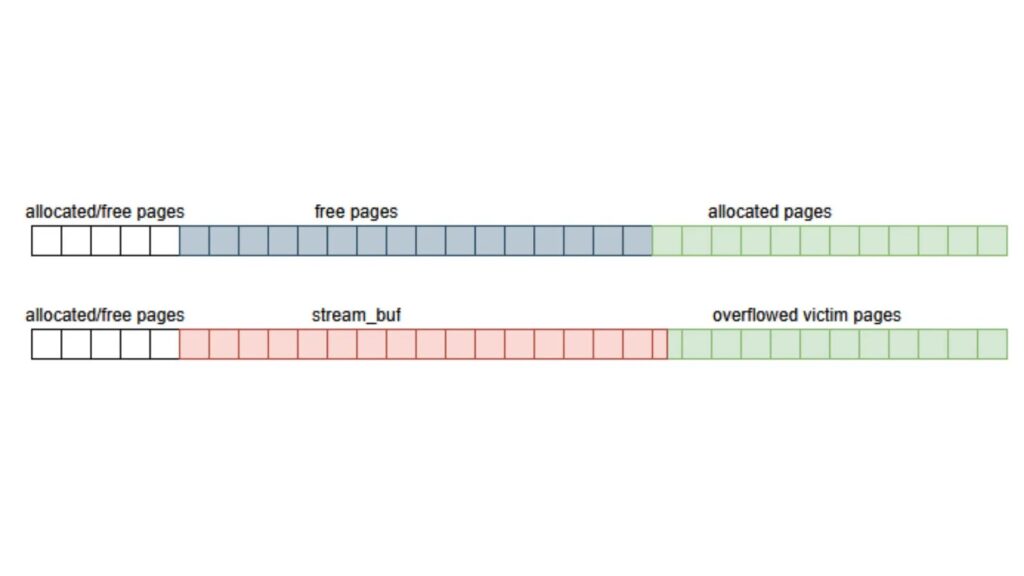
The vulnerability exists in the ksmbd_vfs_stream_write() function, which handles write operations to file streams that use extended attributes. When ksmbd is configured with a writable share and the streams_xattr VFS feature is enabled, an authenticated user can trigger the flaw. The root cause is improper size validation, when a user-supplied position and data count together exceed the XATTR_SIZE_MAX limit of 65,536 bytes. Although the code truncates the buffer allocation, it does not reduce the count used in memcpy, letting an attacker write past the allocated kernel buffer and corrupt adjacent memory.
From out-of-bounds write to root privileges
Doyensec researchers demonstrated a multi-stage exploitation path on a modern Linux distribution, for example Ubuntu 22.04.5 LTS. The exploit chain begins with heap shaping, where the attacker forces kernel allocations and frees to position a controlled kernel object, typically a msg_msg structure, immediately after the vulnerable buffer. The out-of-bounds write corrupts the msg_msg header, creating a use-after-free condition. That UAF is used to leak kernel memory addresses, defeating Kernel Address Space Layout Randomization (KASLR). With KASLR bypassed, the attacker reuses the UAF to overwrite a function pointer in a pipe_buffer object, hijacking kernel control flow to run a ROP chain that yields root.
Proof-of-concept, practical risk, and limits
Doyensec published the complete local privilege escalation PoC on GitHub, enabling security teams to review and test their exposure. The published code highlights the practical risk for systems with ksmbd enabled and writable streams_xattr. The researchers noted that remote exploitation would be considerably harder, because a remote attack would likely also need an information disclosure vulnerability to reliably bypass KASLR and enable stable heap grooming.
Broader context and previous findings
This disclosure is part of a wider security audit of the ksmbd module by Doyensec. The team has previously reported other serious issues in ksmbd, including unauthenticated race conditions and memory exhaustion vulnerabilities. As ksmbd adoption has grown in recent Linux releases, these kernel-level SMB server issues have increasing impact on real world deployments.
Recommendations for administrators
System administrators should immediately review their use of ksmbd, check whether streams_xattr is enabled for writable shares, and apply distribution security updates as they become available that address CVE-2025-37947. Until fixes are applied, consider restricting ksmbd access to trusted users, disabling writable streams_xattr where possible, and monitoring for unusual local activity that could indicate exploitation attempts.