Cybersecurity researchers have identified insecure legacy code inside several Python packages that could allow attackers to compromise the Python Package Index (PyPI) through a domain takeover scenario.
ReversingLabs reported that the issue originates from old bootstrap scripts associated with a build and deployment tool known as zc.buildout. According to researcher Vladimir Pezo, these bootstrap files were created to automate the downloading, building, and installation of necessary tools and libraries.
He explained that when the bootstrap script is executed, it retrieves and runs an installation script for a package called Distribute from python-distribute[.]org. This domain is a legacy asset that is currently up for sale at a premium price and is being maintained only to generate advertising revenue.
Packages containing bootstrap scripts that attempt to contact this domain include tornado, pypiserver, slapos.core, roman, xlutils, and testfixtures.
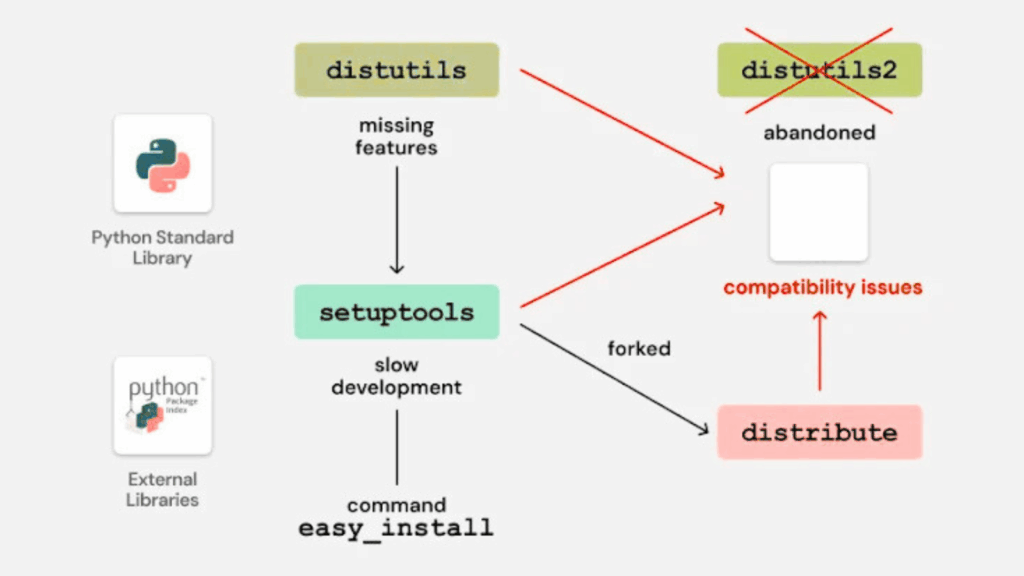
The core problem lies in an outdated bootstrap script named bootstrap.py, which was previously used with zc.buildout to prepare the Buildout environment. Within this process, the script had an option to install a packaging utility called Distribute. This tool was briefly developed as a fork of Setuptools before being reintegrated in 2013, at which point Distribute became unnecessary.
To install Distribute, the bootstrap script downloaded distribute_setup.py from python-distribute[.]org. Since the domain has been available for purchase since 2014, this behavior now creates a security gap. An attacker who gains control of the domain could supply malicious content, which would then be executed if a developer unknowingly runs the old bootstrap script.
ReversingLabs noted that even though Distribute is obsolete, many packages still include bootstrap scripts that either try to install Distribute automatically or enable the option through command line arguments such as -d or –distribute. Because the domain is unclaimed, this puts users at risk of hidden supply chain attacks.
Some packages have already removed the vulnerable code, but slapos.core continues to ship with the affected script. The script is also still present in development versions of Tornado.
Another factor mentioned by the researchers is that the bootstrap script is written in Python 2, which means it does not run under Python 3 without manual adjustments. Even so, its existence leaves an unnecessary entry point for attackers, particularly if a developer can be misled into running legacy code during a build process.
The danger of such takeovers is not hypothetical. In 2023, a domain related to the npm package fsevents, fsevents-binaries.s3-us-west-2.amazonaws[.]com, was taken over by a malicious party. The attacker used the unclaimed cloud resource to deliver harmful executables to users installing certain versions of the package, tracked under CVE-2023-45311 with a severity score of 9.8.
Pezo added that the risky pattern here is the use of hard coded domains to fetch and execute code, which is similar to the behavior of many downloader style malware families. Because Distribute was never formally removed from circulation, old bootstrap scripts remained active in multiple projects without being flagged, leaving developers exposed to a potential attack chain.
The disclosure coincides with a separate finding by HelixGuard, which uncovered a malicious PyPI package called spellcheckers. It claimed to offer spell checking features using OpenAI Vision, but instead connected to an external server to fetch a second payload. That payload ultimately deployed a remote access trojan (RAT).
The package was uploaded on November 15, 2025, by a user named leo636722 and was downloaded 955 times before its removal.
HelixGuard stated that the RAT can receive remote commands and execute attacker supplied Python code through exec(), giving the threat actor complete control of the infected system. Once a user installs and runs the package, the hidden backdoor activates and allows remote manipulation of the victim device.
Found this article interesting? Follow us on Twitter , Facebook, Blue sky and LinkedIn to read more exclusive content we post.