Three leading ransomware groups—DragonForce, LockBit, and Qilin—have officially joined forces, signaling a notable shift in the global cyber threat landscape. This strategic partnership aims to enhance the effectiveness of ransomware operations, according to a report by ReliaQuest shared with The Hacker News.
“Following LockBit’s recent return, this alliance is expected to enable the sharing of techniques, resources, and infrastructure, thereby strengthening each group’s operational efficiency,” the report stated in its Q3 2025 ransomware overview.
The collaboration could also help restore LockBit’s credibility among affiliates after last year’s takedown, potentially leading to a rise in attacks on critical infrastructure and expanding risks to previously low-risk sectors.
Qilin’s involvement is unsurprising, as the group has emerged as one of the most active ransomware operators in recent months, claiming over 200 victims in Q3 2025 alone. “In Q3 2025, Qilin primarily targeted organizations in North America,” ZeroFox noted in its quarterly ransomware summary, adding that the group’s activity notably surged from Q4 2024, with at least 46 attacks recorded.
This development coincides with the launch of LockBit 5.0, designed to target Windows, Linux, and ESXi systems. The new version was first promoted on September 3, 2025, through the RAMP darknet forum, marking the sixth anniversary of the LockBit affiliate program.

LockBit faced a major disruption in early 2024 during a law enforcement operation called Cronos, which seized its infrastructure and led to several arrests. At its peak, the group had targeted over 2,500 victims globally and amassed more than $500 million in ransom payments.
“If LockBit successfully rebuilds trust with its affiliates, it could reemerge as a dominant ransomware threat, motivated both financially and by revenge against previous law enforcement actions,” ReliaQuest noted.
Meanwhile, the Scattered Spider threat actor appears ready to launch ShinySp1d3r, a ransomware-as-a-service (RaaS) program, becoming the first English-speaking extortion group to offer such a service.
ReliaQuest reports monitoring 81 data leak sites, a sharp increase from 51 sites tracked in early 2024. The professional, scientific, and technical services sector suffered the highest number of attacks, impacting over 375 organizations. Other heavily targeted sectors include manufacturing, construction, healthcare, finance, insurance, retail, accommodation, education, arts, entertainment, information, and real estate.
Additionally, ransomware activity is spreading beyond traditional regions like Europe and the U.S., with a notable surge in countries including Egypt, Thailand, and Colombia. However, most victims listed on data leak sites remain in the U.S., Germany, the U.K., Canada, and Italy.
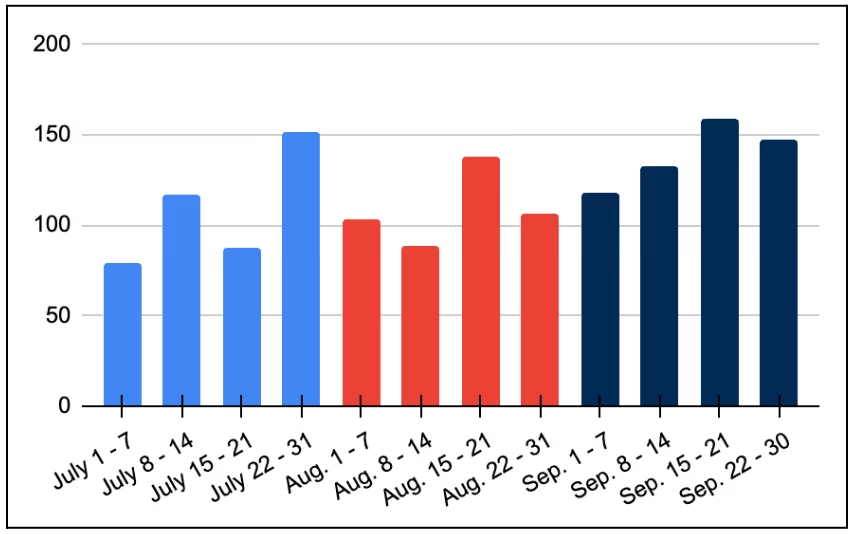
According to ZeroFox, Q3 2025 saw at least 1,429 ransomware and digital extortion incidents, a decrease from 1,961 incidents in Q1 2025. Qilin, Akira, INC Ransom, Play, and SafePay were responsible for approximately 47 percent of all global ransomware attacks during Q2 and Q3 2025.
“The high targeting of North American entities is influenced by geopolitical and ideological factors, as threat groups oppose Western political and social norms,” the report said. “Additionally, North America’s fast-growing digital infrastructure, cloud services, and IoT adoption make it an attractive target for cybercriminals.”


