Cybersecurity experts have identified a new variant of the MacSync macOS information stealer that uses a digitally signed and notarized Swift application to bypass Apple’s Gatekeeper protections. The malware is disguised as a messaging app installer, fooling users into installing it.
According to Jamf researcher Thijs Xhaflaire, unlike earlier MacSync variants that relied on drag-to-terminal or ClickFix-style methods, this version employs a more deceptive, automated approach.
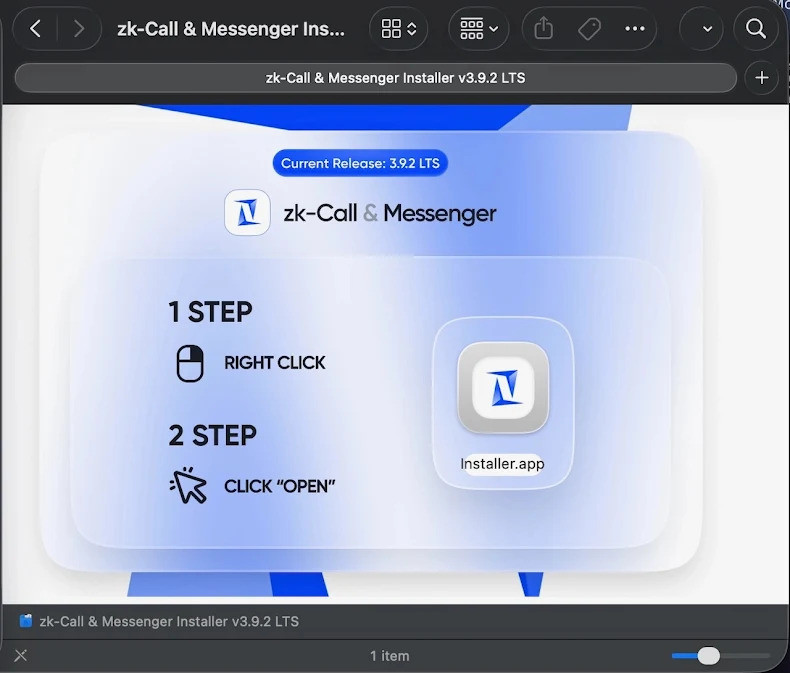
The malicious installer is packaged as a code-signed and notarized Swift app within a DMG file named zk-call-messenger-installer-3.9.2-lts.dmg, hosted at zkcall[.]net/download. Because it is signed and notarized, it can execute without triggering Gatekeeper or XProtect alerts. Users are often prompted to right-click and open the app, a common tactic to bypass security measures. Apple has since revoked the associated code-signing certificate.
Once executed, the Swift dropper performs several checks before downloading and running an encoded script via a helper component. This includes verifying internet connectivity, enforcing a minimum execution interval of roughly 3600 seconds to maintain a rate limit, removing quarantine flags, and validating the file prior to execution.
Xhaflaire noted changes in the curl command used to retrieve the payload. Instead of the typical -fsSL combination, flags were split into -fL and -sS, with additional options such as –noproxy, indicating a deliberate attempt to enhance reliability or avoid detection.
The campaign also employs evasion techniques such as inflating the DMG file to 25.5 MB by embedding unrelated PDFs, making it harder to detect.
The Base64-encoded payload corresponds to MacSync, a rebranded version of Mac.c that emerged in April 2025. MacSync features a fully-equipped Go-based agent, enabling not just data theft but also remote command and control functions.
Code-signed DMG files mimicking legitimate apps, such as Google Meet, have also been seen in attacks by other macOS stealers like Odyssey. Meanwhile, unsigned disk images continue to be used for distributing malware like DigitStealer.
Jamf noted that this trend reflects a broader shift in macOS malware, with attackers increasingly embedding malicious payloads in signed and notarized executables to appear legitimate and bypass built-in security controls.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


