Cybersecurity researchers have uncovered a new and more deceptive variant of the MacSync malware targeting macOS users. Unlike earlier versions that depended on visible user interaction tricks such as ClickFix techniques, this updated strain disguises itself as a legitimately signed and notarised Apple application. By doing so, it successfully bypasses macOS Gatekeeper protections and quietly steals sensitive user data.
Code Signed Malware Evades macOS Protections
Jamf Threat Labs recently analyzed this evolved MacSync stealer and identified two major technical shifts in its design. Most notably, the malware is now built as a Swift based application, Apple’s official programming language for macOS development, and is both code signed and notarised.
This approach allows the malware to appear as a trusted application from a verified developer, preventing Gatekeeper from displaying the usual warnings about unidentified or untrusted software.
Threat actors reportedly obtain valid Apple developer certificates through multiple methods, including stealing certificates, purchasing compromised developer accounts, or creating fake developer entities using fraudulent identities. Once signed, the malicious application blends in with legitimate software, significantly lowering user suspicion.
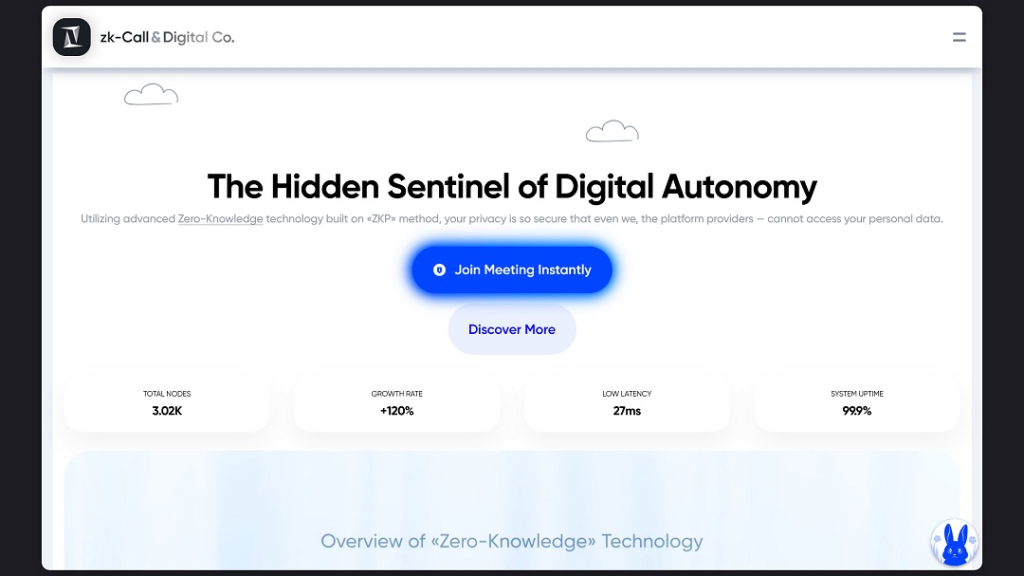
Social Engineering Through App Impersonation
The new MacSync variant heavily relies on social engineering to trick users into installation. Researchers observed that it impersonates online messaging platforms, with a particular focus on services such as zk-Call, an Estonia based calling and messaging application.
By mimicking real world communication tools, attackers increase the likelihood that victims will willingly install the malware, believing it to be a legitimate utility.
Technical Evolution of MacSync
This version of MacSync represents a clear departure from earlier variants. Previous samples were lightweight and primarily executed modular payloads directly in memory, leaving minimal traces on disk.
In contrast, Jamf researchers reported that the new variant uses a large disk image measuring approximately 25.5MB. This suggests expanded functionality and additional embedded components designed to enhance persistence and capability.
Capabilities and Command and Control
Once installed, MacSync can carry out a range of malicious activities. These include deploying backdoors for remote access, stealing stored system and browser data, harvesting cryptocurrency wallet credentials, and maintaining persistent hidden access on the infected system.
Jamf identified focusgroovy[.]com as a command and control server used to retrieve additional payloads. According to Moonlock, modern web browsers are already flagging this domain for suspected phishing behavior.
Distribution Methods and User Risk
Although the exact initial infection vector has not been confirmed, researchers believe the malware may be distributed through malicious advertising, social media abuse, search engine manipulation, or targeted spear phishing campaigns.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.