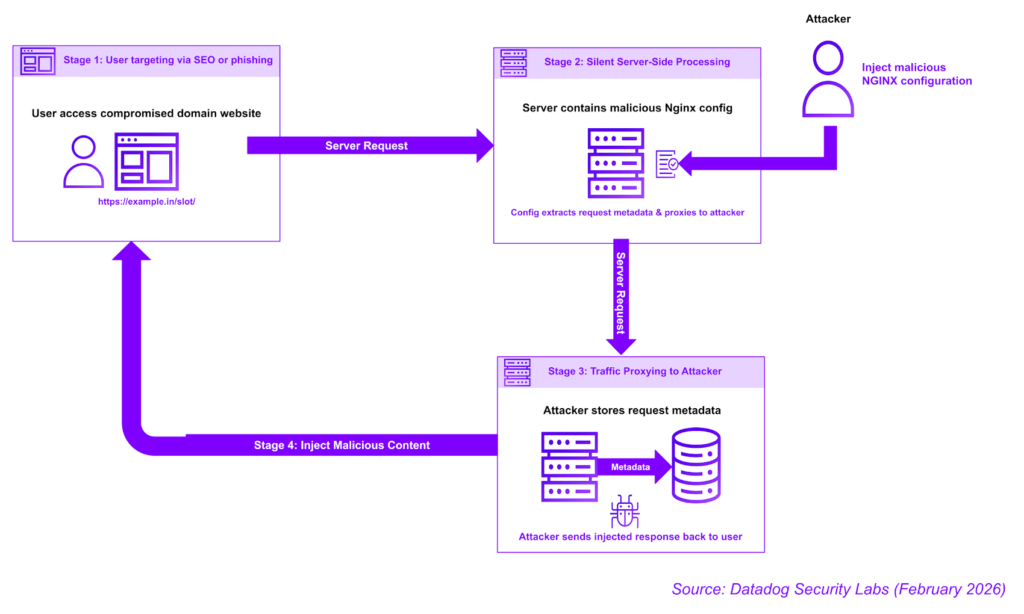
Cybersecurity researchers have identified an active campaign in which attackers exploit NGINX installations and management platforms such as Baota (BT) Panel to hijack web traffic on a large scale. The operation manipulates web requests, routing them through infrastructure controlled by threat actors.
Datadog Security Labs reported that the campaign leverages React2Shell (CVE-2025-55182, CVSS score: 10.0) exploits alongside malicious NGINX configurations to intercept and redirect traffic.
“The attackers insert malicious configuration files that reroute legitimate user requests to attacker-controlled backend servers,” explained security researcher Ryan Simon. “Targets include Asian top-level domains (.in, .id, .pe, .bd, .th), Chinese hosting infrastructure via Baota, and government and educational domains (.edu, .gov).”
Attack Methodology
The campaign uses shell scripts to inject rogue directives into NGINX, an open-source reverse proxy and load balancer. The scripts modify “location” blocks to capture traffic on specific URLs and forward it using the proxy_pass directive.
The attack employs a multi-stage toolkit designed for persistence and precise configuration injection. Key components include:
- zx.sh – Orchestrates further stages, using curl or wget. If blocked, it establishes a raw TCP connection to send HTTP requests.
- bt.sh – Targets the Baota (BT) Panel environment to overwrite NGINX configuration files.
- 4zdh.sh – Enumerates common NGINX configuration paths while minimizing errors during modifications.
- zdh.sh – Focuses on Linux or containerized NGINX setups and specific TLDs like .in and .id.
- ok.sh – Generates reports detailing all active hijacking rules within NGINX.
These scripts collectively enable attackers to discover targets, maintain persistence, and redirect web traffic efficiently.
Scope and Observations
GreyNoise intelligence reported that just two IP addresses (193.142.147[.]209 and 87.121.84[.]24) accounted for 56% of exploitation attempts two months after the React2Shell vulnerability was disclosed. Between January 26 and February 2, 2026, researchers tracked 1,083 unique IP addresses involved in attacks exploiting React2Shell.
Distinct post-exploitation payloads were observed: one set retrieved cryptocurrency-mining binaries from staging servers, while the other opened reverse shells directly to the attackers’ scanners. This indicates a focus on interactive access rather than automated resource theft.
The campaign also mirrors previous coordinated reconnaissance targeting Citrix ADC Gateway and Netscaler Gateway, where attackers used tens of thousands of residential proxies and a single Microsoft Azure IP (52.139.3[.]76) to map login panels and enumerate versions. Researchers note that the dual approach—massive distributed discovery and concentrated Azure-hosted scanning—points to highly organized reconnaissance efforts.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


