In a stark reminder of the vulnerabilities within open-source ecosystems, cybersecurity analysts have unearthed ten deceptive npm packages engineered to pilfer sensitive developer credentials. These packages, capable of operating on Windows, macOS, and Linux, employ sophisticated stealth techniques to avoid detection while harvesting a treasure trove of personal and corporate data.
The Deceptive Packages and Their Disguise
The malicious modules were published to the npm registry on July 4, 2025, and managed to amass a staggering collective download count of over 9,900. They strategically impersonate well-known and widely-used libraries through typosquatting, relying on common misspellings to trick developers.
The list of fraudulent packages includes:
- deezcord.js
- dezcord.js
- dizcordjs
- etherdjs
- ethesjs
- ethetsjs
- nodemonjs
- react-router-dom.js
- typescriptjs
- zustand.js
These names are designed to mimic popular tools like TypeScript, discord.js, and zustand, catching developers in a moment of inattention.
A Multi-Layered Attack Strategy
The malware’s operation is a masterclass in deception. Upon installation, it does not immediately reveal its malicious intent. Instead, it initiates a complex, multi-stage process to steal information.
The Fake CAPTCHA and Postinstall Hook
The attack is automatically triggered by a postinstall hook, which runs a script named install.js. To appear legitimate, the script displays a fake CAPTCHA prompt and mimics the authentic output of a standard package installation. This reassures the developer that the process is normal.
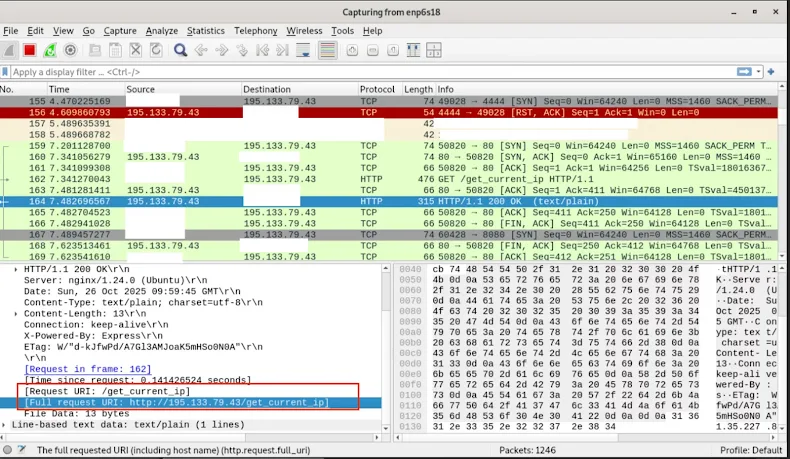
In the background, however, the script is busy fingerprinting the victim by capturing their IP address and sending it to a remote server (195.133.79[.]43).
Stealthy Execution and Advanced Obfuscation
To run independently of the npm process, the malware spawns a new terminal window—Command Prompt on Windows, Terminal on macOS, or GNOME/x-terminal-emulator on Linux. This new window briefly flashes and is immediately cleared, a fleeting sight most developers would dismiss.
The core malicious code resides in a file called app.js, which is protected by four distinct layers of obfuscation. These include XOR cipher encryption with a dynamic key, URL-encoding of the payload, and the use of hexadecimal and octal arithmetic to confuse analysis tools. This makes reverse-engineering the code exceptionally difficult.
The Final Payload: A Comprehensive Data Extractor
The ultimate objective is to download and execute a massive, 24MB information stealer packaged with PyInstaller, known as data_extracter. This powerful binary performs a comprehensive scan of the developer’s machine, targeting:
- Web browsers for saved passwords, cookies, and session data.
- System configuration files and stored SSH keys.
- Authentication tokens for various services.
The Critical System Keyring Breach
Perhaps the most alarming capability is the stealer’s direct targeting of the system keyring. Using the keyring npm library, it extracts credentials in their decrypted form from the operating system’s secure storage.
These keyrings typically safeguard credentials for critical applications, including:
- Email clients like Outlook and Thunderbird.
- Cloud storage tools such as Dropbox, Google Drive, and OneDrive.
- VPN clients (Cisco AnyConnect, OpenVPN).
- Password managers and database connection strings.
“As the malware directly targets the keyring, it effectively bypasses application-level security measures,” explained Socket researcher Kush Pandya. “The stolen decrypted credentials offer attackers immediate access to corporate email, internal networks, file storage, and even production databases.”