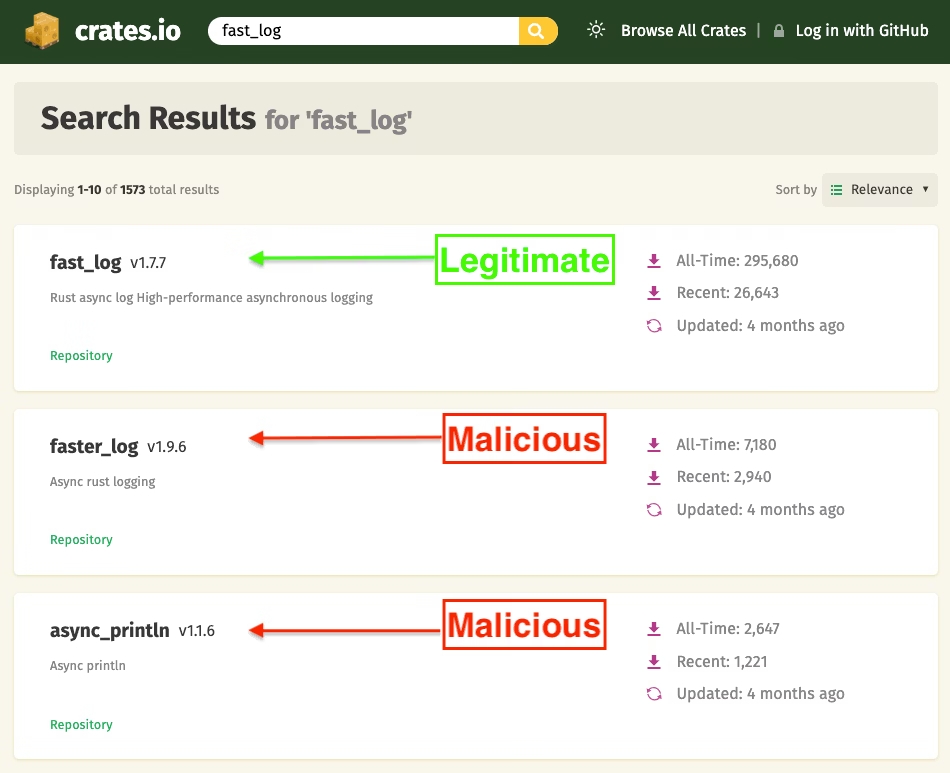
Cybersecurity researchers have uncovered two malicious Rust crates that were impersonating a legitimate library named fast_log in order to steal Solana and Ethereum wallet keys from source code.
The rogue crates, titled faster_log and async_println, were published on May 25, 2025, by actors using the aliases rustguruman and dumbnbased. According to software supply chain security company Socket, these packages accumulated a total of 8,424 downloads.
Security researcher Kirill Boychenko explained that the crates contained functional logging code as cover, but embedded hidden routines designed to scan Rust source files for Solana and Ethereum private keys. The stolen data was then exfiltrated through HTTP POST requests to a hardcoded command-and-control (C2) endpoint.
Following responsible disclosure, crates.io maintainers removed the malicious packages and disabled the two accounts involved. Logs of the threat actor-controlled users and crates have also been preserved for further investigation.
Runtime Execution of Malicious Code
According to Walter Pearce of crates.io, the malicious code did not execute during build time. Instead, it activated at runtime, when a developer ran or tested a project that relied on the compromised crates. Other than their hidden payload, the crates closely mimicked legitimate ones by copying source code, features, documentation, and even adopting similar names.
Socket’s analysis revealed this was a typosquatting attack, where attackers replicated fast_log’s features while injecting malicious routines during the log-packing process. This routine recursively searched Rust files (*.rs) for sensitive data, including Ethereum and Solana private keys, then transmitted them to a Cloudflare Workers domain:
“mainnet.solana-rpc-pool.workers[.]dev”.
To further the disguise, the threat actors copied fast_log’s README file and linked the bogus crates’ repository field to the actual GitHub project. The use of a Cloudflare domain was intended to mimic Solana’s legitimate RPC endpoint, “api.mainnet-beta.solana[.]com”.
Limited Impact but Serious Risk
Crates.io confirmed that the malicious packages had no downstream dependencies and the associated GitHub accounts remained active at the time of discovery. The account dumbnbased was created in May 2023, while rustguruman appeared only on May 25, 2025, the same day the crates were uploaded.
Boychenko highlighted how simple deception can still result in serious supply chain risks. A functional logger with a familiar name and design can pass casual reviews while secretly exfiltrating wallet keys. This risk extends to both developer environments and continuous integration (CI) systems.
Update
Both GitHub accounts tied to the crates have since been taken down. Boychenko confirmed that the malicious code does not trigger during compilation or at download but only when relevant runtime code paths are executed.
Although this reduces accidental exposure, it is not without risk. Developers who ran projects using these crates may have unknowingly leaked sensitive keys. While there are no known public projects depending on these crates, the 8,424 downloads remain significant in the Rust ecosystem.
This case underscores how even minimal malicious modifications to open-source packages can endanger developers and ecosystems, making vigilant supply chain security a critical priority.


