In a recent Advanced Continual Threat Hunt (ACTH) operation, Trustwave’s SpiderLabs uncovered a stealthy campaign where cybercriminals weaponized ScreenConnect, a legitimate remote management tool, to deliver the Xworm Remote Access Trojan (RAT) through a layered infection chain.
By using fake AI-related content and tampered digital certificates, the attackers managed to bypass many Endpoint Detection and Response (EDR) solutions, leaving manual threat hunting as the key method of detection.
Infection Chain Through Fake AI Sites
The campaign began with social engineering tactics. Victims were lured to a fake AI platform, gptgrok[.]ai, which redirected them to anhemvn6[.]com.
From there, users downloaded files named:
- Creation_Made_By_GrokAI.mp4 Grok.com
- Creation_Made_By_GoogleAI.mp4 Google.com
- Creation_Made_By_SoraAI.mp4 OpenAI.com
These were not videos but disguised ScreenConnect installer files (ScreenConnect.ClientSetup.msi). By leveraging AI-related keywords, attackers gave credibility to their malicious campaign.
Code-Signing Certificate Abuse

Researchers discovered that the attackers abused Microsoft Authenticode code-signing certificates. Instead of altering the binary directly, they embedded malicious parameters within the digital signature. This allowed the installer to retain a valid signature, helping it evade tampering checks and user suspicion.
Once executed, the installer placed ScreenConnect in the Temp directory, configured it to run in hidden mode, and connected back to the attacker’s server. Icons and notifications were disabled, keeping the session invisible.
Fileless Execution with Python Payloads
During the remote session, a batch file named X-META Firebase_crypted.bat launched mshta.exe, which fetched 5btc.zip from anhemvn4[.]com. Inside were:
- pw.exe (a renamed Python interpreter)
- basse64.txt (an encoded payload)
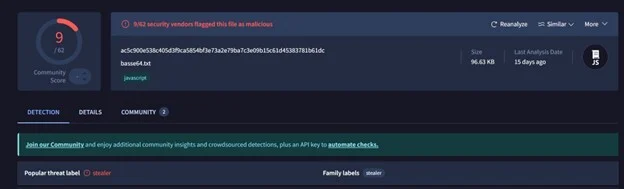
Instead of writing malicious files to disk, the attackers used process hollowing in msedge.exe and chrome.exe. The Base64-encoded Python commands were pulled from a public GitHub repository, enabling stealthy, fileless execution of Xworm RAT.
Persistence and Long-Term Access
Persistence was achieved through a Windows Run key entry labeled “Windows Security,” pointing to backup.bat inside C:\xmetavip. This script re-executed pw.exe on every login with updated Base64 commands, fetching additional payloads like buquabua.txt.
The RAT also attempted credential harvesting by extracting stored browser passwords (Chrome, Edge, Firefox) and gathering system details via WMI queries.
GitHub-Hosted Malware and Final Payload
SpiderLabs noted that the GitHub repository hosted 11 obfuscated scripts, split between RAT loaders and persistence modules, created shortly before the attacks.
One final payload, Exppiyt.txt, contained a command-and-control (C2) IP (5[.]181[.]165[.]102:7705), which at the time was not flagged on VirusTotal.
Why This Matters
This campaign highlights a dangerous trend: attackers abusing legitimate software, AI branding, and digital signatures to bypass security solutions. Traditional EDR struggled to detect this, reinforcing the importance of skilled human threat hunters who can spot subtle anomalies.
The SpiderLabs report shows that blending automation with expert analysis remains the most effective way to expose advanced threats before they cause damage.
Indicator of Compromise (IoC) Hashes
| File Name | Hash Type | Hash Value |
|---|---|---|
| basse64.txt | MD5 | 01cb34d362e688ea637582370b981402 |
| backpuppure.txt | MD5 | bcd902751a6bebda00a417c880937a25 |
| abcdegia.txt | MD5 | 2c0ac59a823ff90a179ba1144d142eb2 |
| Nhwneafyp.txt | MD5 | b33c6c77a7adda12e70766f02dbe8205 |
| Hzcbmqnqwlv.txt | MD5 | 8c2e092079906c5f59c7d9ee5e139bb5 |
| Exppiyt.txt | MD5 | 07c20378fc00934bf62a0986f8da58c8 |
| x-metavn.txt | MD5 | 4f17dbaf42ad92f56b24d33067a4d52f |
| purecoookielog.txt | MD5 | f9f6e3826343cc9c11495852596593d4 |
| exepurelog.txt | MD5 | a1377a061b6da88d81bd104e85cb3101 |
| cccccccccccccccccccccc.txt | MD5 | 2fa26c5f869c26e17ce5617cce46efd0 |
| buquabua.txt | MD5 | 3baf507303132c234dba993cc804bd68 |
| Btxeialrzt.exe | MD5 | b7d98c93307eb75126d41bf40fa3d724 |
| Exzdjz.dll | MD5 | 94b3eab92f9ff8cd02bf4b5dbcc17e5c |
| ClassLibrary4.dll | MD5 | 9b34d9dccd512ededa25ba0a2d13a875 |
| Creation_Made_By_GrokAl.mp4 (Grok.com) | SHA256 | e4a7853cacf4dfe42d465ee64e9b4b7aaaa229a34ac913e1fd2359c09578db5f |
| Temp\X-META Firebase_crypted.bat | SHA256 | 5769ce40411966de7085fd4a551f65900d77d7badee2c818f16b54d0dc4f5e46 |
| abcdegia.txt | MD5 | 2c0ac59a823ff90a179ba1144d142eb2 |