A new and highly coordinated malware campaign has surfaced in Indonesia, specifically preying on senior citizens who depend on the nation’s official pension system. The attackers are exploiting the credibility of PT Dana Tabungan dan Asuransi Pegawai Negeri (TASPEN), the state-owned pension fund that manages more than $15.9 billion in assets for millions of retired civil servants.
This campaign represents a serious shift in cybercrime tactics, where cybercriminals weaponize institutional trust to carry out widespread financial fraud. With more senior citizens moving toward digital platforms for pension services, they have become the latest high-value targets.
Phishing Website Disguised as Official TASPEN App
The malicious actors created a phishing website at taspen[.]ahngo[.]cc, which convincingly imitates an official TASPEN mobile app download page. The fake page includes TASPEN’s branding and the slogan: “A reliable app, easy with TASPEN” in Bahasa Indonesia.
The site displays clickable Google Play and Apple App Store icons. However, the Android link directly downloads malicious APK files, while the iOS button shows a fake maintenance message to maintain the appearance of legitimacy.
Cybersecurity firm CloudSEK discovered the campaign through its threat intelligence operations. Their investigation revealed that the malware uses advanced evasion techniques designed to bypass conventional security solutions.
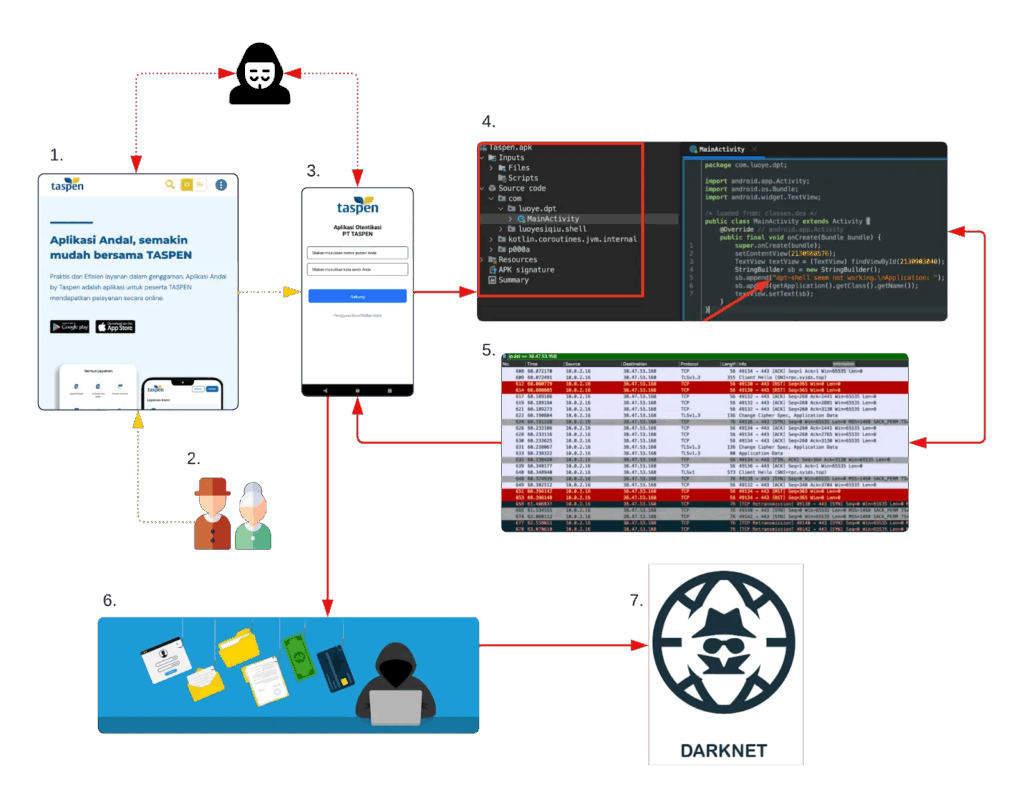
Advanced Obfuscation Through DPT-Shell
The malicious APK is shielded by DPT-Shell, an open-source Android packer that encrypts executable code. The payload is only decrypted and executed at runtime, making it extremely difficult for static analysis tools to detect.
When launched, DPT-Shell decrypts the malicious code in memory and stores it inside the app’s private code_cache directory under the name i111111.zip. This method ensures the dangerous payload only becomes visible once the malware is actively running on a device.
Runtime Payload Deployment and Data Theft
Once operational, the malware activates multiple background services designed for surveillance and data theft:
- SmsService — Intercepts and forwards all incoming SMS messages, including sensitive two-factor authentication codes.
- ScreenRecordService — Records live screen activity, enabling attackers to monitor victim actions.
- CameraService — Captures facial video for biometric theft.
- ContactData — Exfiltrates the victim’s complete contact list, emails, phone numbers, and call history.
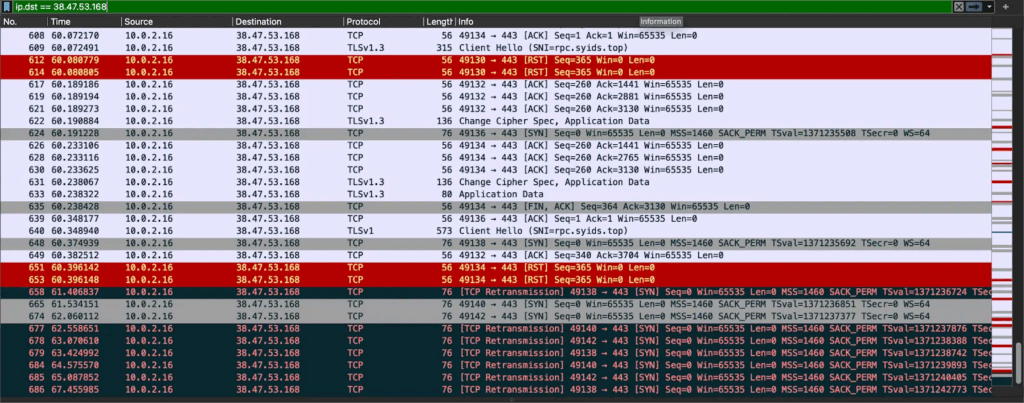
The malware communicates with its command-and-control server at rpc.syids.top using both HTTP POST requests for stolen data and WebSocket connections for real-time attacker commands.
Whenever users enter banking credentials, the malware encrypts and secretly transmits the data while simultaneously showing fake Indonesian error messages, tricking victims into believing their login attempt simply failed.
Evidence of Chinese-speaking Threat Actors
Attribution analysis uncovered strong linguistic markers suggesting Chinese-speaking cybercriminals. Simplified Chinese error strings were found hidden inside both the phishing infrastructure and the malware’s server communications.
A Threat to Indonesia’s Public Institutions
This campaign not only endangers retirees’ financial security but also sets a dangerous precedent for future attacks on Indonesian public service platforms. With millions of citizens relying on digital government portals for pensions, healthcare, and financial services, this operation highlights a growing national cybersecurity risk.