Cybersecurity analysts have identified a new trend in phishing operations, where browser notifications are being misused to push malicious links through a command and control platform known as Matrix Push C2. According to a recent report from BlackFog researcher Brenda Robb, the framework operates entirely within the browser environment, using push alerts, fake system style warnings, and redirect links to deceive victims across different operating systems.
How the Attack Begins
The attack initiates when a user is convinced through social engineering to enable notifications on a malicious or compromised website. Once permission is granted, attackers immediately begin sending notifications that resemble legitimate alerts from the browser or the operating system. These alerts often use familiar branding, logos, and carefully crafted wording to maintain credibility.
Common notification themes include security warnings, suspicious login messages, and browser update prompts. Each message contains a button such as Verify or Update, which redirects the victim to a fraudulent webpage designed to harvest credentials or deliver additional payloads.
Why the Technique Is Effective
The entire attack chain relies on browser functions, without requiring malware installation. This method mirrors the ClickFix style approach where victims are persuaded to perform actions that weaken their own security protections. Since the browser operates across all platforms, any device that subscribes to these malicious notifications becomes part of the attacker’s network, enabling long term access and communication.
Matrix Push C2 Offered as a MaaS Kit
Matrix Push C2 is being sold as a malware as a service kit on platforms like Telegram and cybercrime forums. Subscription pricing includes one month for 150 dollars, three months for 405 dollars, six months for 765 dollars, and one year for 1500 dollars. Payments are accepted in cryptocurrency.
BlackFog CEO Dr. Darren Williams stated that the tool was first spotted in early October and appears to be entirely new with no evidence of older versions or legacy infrastructure.
Capabilities of the Malware Kit
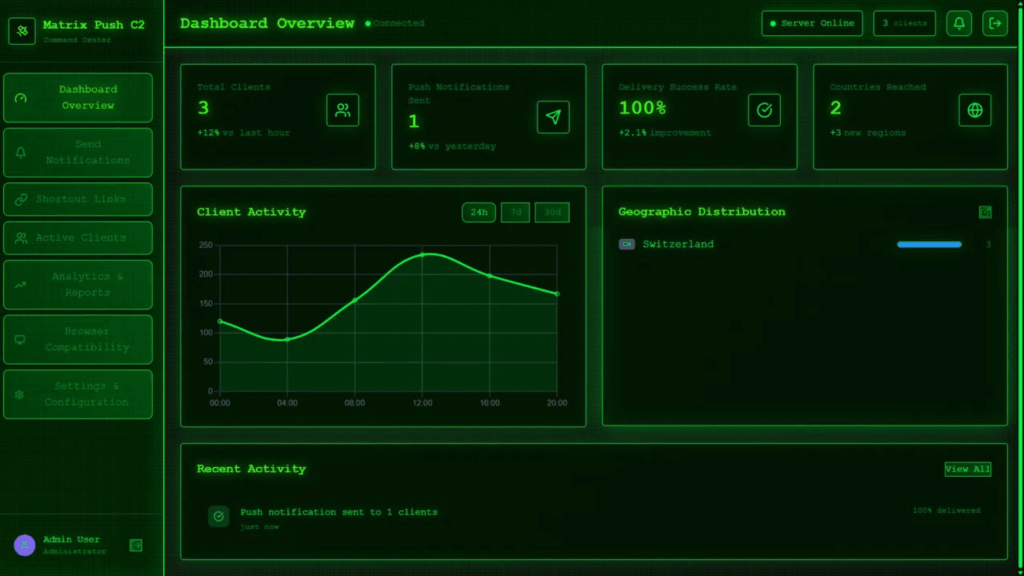
The service includes a web based dashboard where threat actors can manage victims, send notifications, track interactions, and create shortened URLs. The system also records installed browser extensions, including cryptocurrency wallets.
Robb confirmed that the tool contains ready made phishing templates designed to impersonate known brands such as MetaMask, Netflix, Cloudflare, PayPal, and TikTok. An analytics section further helps attackers refine their campaigns.
Potential for Escalation
BlackFog warned that once attackers gain influence over a user’s device through notifications, they can escalate the attack over time. This may include stealing credentials, persuading users to install persistent malware, or exploiting browser vulnerabilities. The final objective often involves financial theft or unauthorized data extraction.
Rise in Attacks Misusing Velociraptor
In a separate development, Huntress reported an increase in misuse of the legitimate Velociraptor DFIR tool. On November 12, 2025, the company observed attackers deploying Velociraptor after exploiting a vulnerability in Windows Server Update Services, tracked as CVE 2025 59287 with a CVSS score of 9.8.
Once inside the system, threat actors executed discovery commands to gather information about services, users, and configurations. Huntress stated that the attack was stopped before it could escalate further.
Researchers added that attackers frequently weaponize legitimate security tools, noting that Velociraptor will not be the first or the last dual use tool to appear in such campaigns.