Microsoft security researchers have revealed a large scale ClickFix social engineering campaign that abuses the Windows Terminal application to execute malicious commands and ultimately deploy the Lumma Stealer malware.
The campaign, detected in February 2026, introduces a new technique where attackers persuade victims to run commands inside Windows Terminal (wt.exe) instead of the commonly abused Windows Run dialog.
Social Engineering Through Trusted Tools
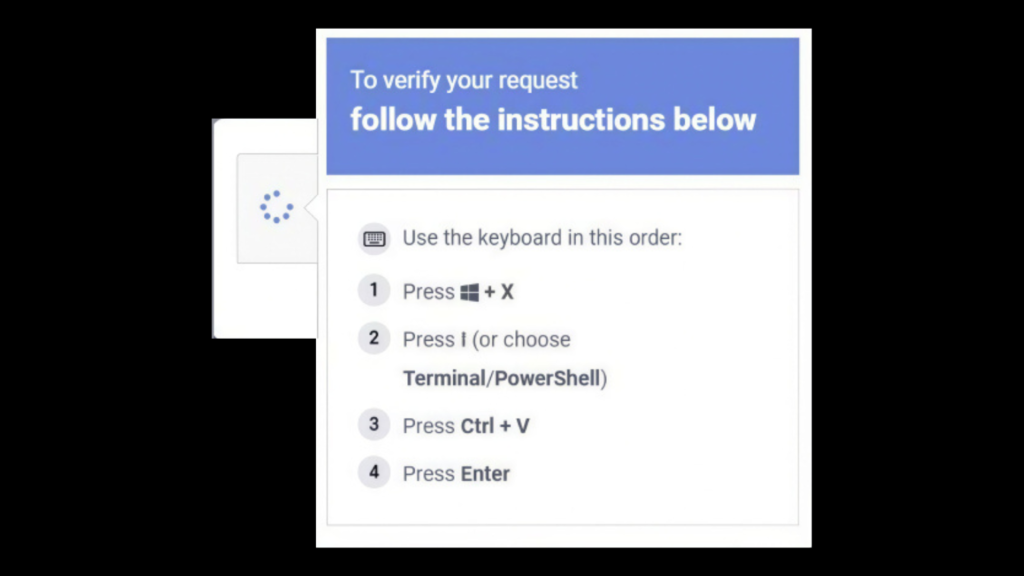
According to Microsoft Threat Intelligence, victims are guided through instructions that tell them to press Windows + X followed by I, which launches Windows Terminal directly. This shortcut opens a command execution environment often used by administrators, making the activity appear legitimate.
By exploiting the credibility of this built in tool, attackers can trick users into running harmful commands while bypassing detection mechanisms that normally monitor misuse of the Run dialog.
The malicious commands are typically copied from fake verification pages, including CAPTCHA prompts, troubleshooting instructions, or other convincing web based lures.
Multi Stage Malware Execution
Once the victim pastes the command into the terminal window, a complex attack chain begins. The command is usually hex encoded and XOR compressed, which hides its real purpose.
The execution process launches additional Terminal and PowerShell instances that decode the malicious script. After decoding, the script downloads a compressed archive and a legitimate but renamed 7 Zip utility, which is stored on the system under a randomized file name.
The renamed archive tool then extracts the downloaded files, starting a multi stage infection process.
Malicious Actions Performed on Infected Systems
During the attack chain, several activities take place on the compromised machine:
- Downloading additional malicious payloads
- Establishing persistence using scheduled tasks
- Adding exclusions within Microsoft Defender security settings
- Collecting device and network information
- Deploying Lumma Stealer through a process injection technique called QueueUserAPC()
The malware injects itself into running browser processes such as chrome.exe and msedge.exe.
Credential Theft and Data Exfiltration
The Lumma Stealer focuses on extracting sensitive browser artifacts including Web Data and Login Data, which store saved credentials and authentication information.
These details are then transmitted to attacker controlled infrastructure, allowing cybercriminals to access user accounts and potentially expand the intrusion.
Alternate Infection Technique Observed
Microsoft researchers also identified a second infection path used in the campaign.
In this scenario, the command pasted into Windows Terminal downloads a randomly named batch script into the AppData\Local directory using the cmd.exe process. This script generates a Visual Basic Script inside the system’s temporary directory.
The batch script is then executed multiple times, including through MSBuild.exe, which represents a classic Living Off the Land Binary (LOLBin) abuse technique.
Use of Blockchain Infrastructure for Stealth
The script also communicates with Crypto Blockchain RPC endpoints, indicating the use of a stealth technique known as etherhiding. This method allows attackers to store or retrieve malicious instructions using blockchain infrastructure.
At the final stage, the malware once again performs QueueUserAPC based code injection into browser processes to steal stored credentials and browsing data.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.