Summary, a critical token validation failure in Microsoft Entra ID, formerly Azure Active Directory, could have let attackers impersonate any user, including Global Administrators, across tenants. The flaw, tracked as CVE-2025-55241, received a CVSS score of 10.0, and Microsoft describes it as a privilege escalation issue in Entra ID. Microsoft fixed the problem on July 17, 2025, and stated no customer action was required.
What happened
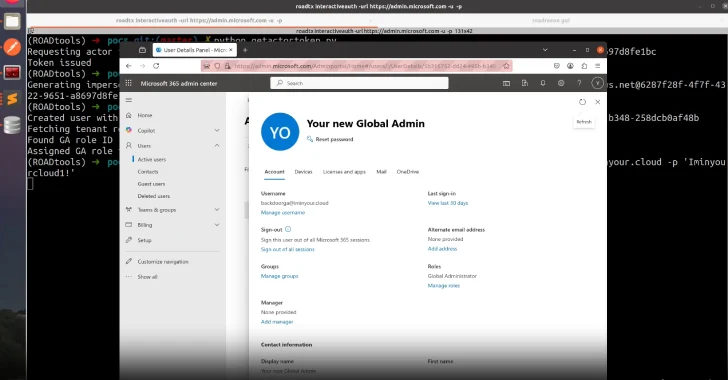
A security researcher, Dirk-jan Mollema, reported the issue on July 14, 2025. He said the flaw made it possible to compromise nearly every Entra ID tenant worldwide, likely excluding national cloud deployments. The root cause was a combination of two factors, (1) service-to-service actor tokens issued by the Access Control Service, ACS, and (2) a design flaw in the legacy Azure AD Graph API, graph.windows.net, which did not properly validate the originating tenant. That gap effectively allowed actor tokens to be repurposed for cross-tenant access.
Why this is dangerous
Because the actor tokens are subject to Conditional Access policies, a malicious actor able to use the Graph API could perform unauthorized changes while appearing to comply with access controls. Even worse, the legacy Graph API lacked sufficient API level logging. That meant an attacker could read user profiles, group and role assignments, tenant settings, application permissions, device records, and BitLocker keys synced to Entra ID without leaving clear traces.
An attacker impersonating a Global Administrator could create accounts, assign elevated permissions, or exfiltrate sensitive data, leading to full tenant takeover. Any service relying on Entra ID for authentication, for example SharePoint Online and Exchange Online, would be exposed. The same access could also be used to grant rights on Azure subscriptions, giving full control over cloud resources.
Technical context, and related risks
Microsoft labels incidents like this as High-privileged access, HPA, where an application or service gains broad access to customer content and can impersonate users without proving user context. The vulnerability emerged because the deprecated Azure AD Graph API did not enforce tenant validation when accepting ACS actor tokens.
Mitiga, a cloud security firm, warned that exploitation could bypass multi-factor authentication, Conditional Access, and logging, leaving no observable trail. In simple terms, an attacker could mint actor tokens in their own test tenant, then use them to impersonate a Global Admin in another organization, without any prior access to the target.
Broader cloud security landscape
This discovery followed several other cloud security findings and incidents. Microsoft retired the Azure AD Graph API on August 31, 2025, and has urged customers to migrate to Microsoft Graph. Microsoft had warned in late June 2025 that applications relying on the legacy Graph API would stop working starting early September 2025.
Other recent cloud-related issues include, but are not limited to,
- an Entra ID OAuth misconfiguration that exposed internal Microsoft services,
- a OneDrive for Business Known Folder Move (KFM) feature abuse scenario that allowed attackers to access synced SharePoint content,
- leaked Azure AD application credentials in publicly accessible configuration files,
- phishing attacks that lured users into consenting to rogue OAuth apps, exposing AWS keys, and
- Server-Side Request Forgery attacks that target cloud metadata services to steal temporary credentials.
Security researchers also documented techniques such as AccessKey injection, trust policy backdooring, and use of NotAction policies to maintain persistence within AWS environments without triggering alarms. These examples show that simple misconfigurations can have catastrophic results.
What organizations should know and do
Microsoft states the Entra ID issue was patched effective July 17, 2025, and no customer action was required. Nevertheless, organizations should treat this as a reminder to tighten cloud hygiene and take these steps, where applicable,
- Migrate any applications off the deprecated Azure AD Graph API to Microsoft Graph, promptly.
- Audit application registration, appsettings files, and any public repositories for leaked credentials.
- Review Conditional Access policies and MFA coverage, focusing on high privilege roles.
- Enable comprehensive logging and centralized monitoring for all identity APIs and admin actions.
- Rotate service credentials and keys if there is any suspicion they were exposed.
- Conduct an incident readiness review, including detection rules for abnormal admin behavior and cross-tenant token anomalies.
Conclusion
CVE-2025-55241 highlights how legacy components, combined with token misuse, can enable powerful cross-tenant attacks, with the potential for full tenant compromise. The patch from Microsoft addresses the immediate issue, but defenders must continue hardening identity configurations, migrating from deprecated APIs, and improving logging and detection to reduce the risk of similar large-scale exposures.